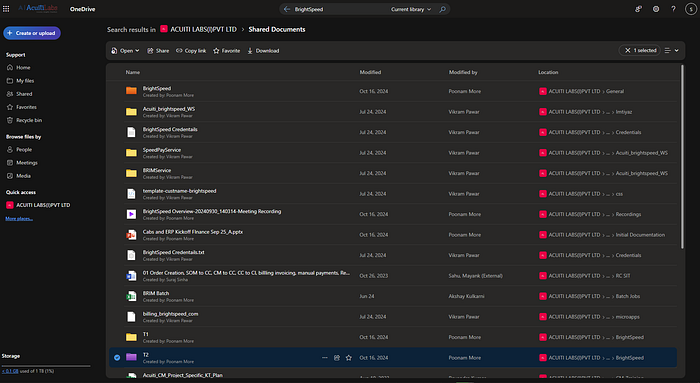
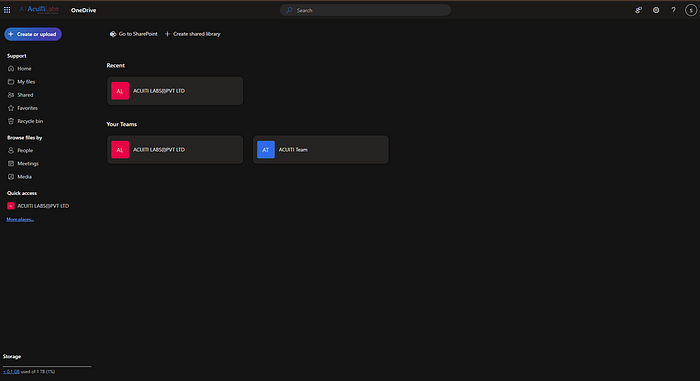
A significant data breach has recently emerged on the dark web, raising serious concerns across the cybersecurity landscape. Sensitive data belonging to multiple organisations — including Yilport Holding Inc, BrightSpeed, Posti, Changi Airport Singapore and SpeedPayService — has reportedly been leaked by Acuiti Labs
Overview of the Incident
According to findings from underground forums and dark web marketplaces, the attacker has published a large dataset allegedly containing confidential corporate and user information. The exposed data appears to span across multiple companies, suggesting either a coordinated campaign or exploitation of shared vulnerabilities.
While the full scope of the breach is still under investigation, early indicators suggest that the leaked information may include:
- User credentials (emails and hashed/plaintext passwords)
- Internal company documents
- Customer records
- API keys or access tokens
- Potential infrastructure-related data

Threat Actor Activity
The individual or group behind the breach, known as Acuiti Labs, has not only released samples of the stolen data but has also provided a contact email address, inviting interested parties to reach out. This behaviour aligns with common tactics used in:
- Data extortion campaigns
- Private sale of exclusive datasets
- Negotiation attempts with affected organizations
Such actions indicate that this may not just be a simple leak, but part of a broader monetization strategy.
Potential Impact
The consequences of this breach could be severe, depending on the sensitivity and validity of the exposed data. Organizations impacted may face:
- Reputational damage
- Regulatory scrutiny and compliance penalties
- Increased risk of phishing and social engineering attacks
- Unauthorized access to internal systems
For customers and users, this leak could translate into identity theft risks, credential stuffing attacks, and financial fraud.
Recommended Actions
Organizations potentially affected by this incident should take immediate steps to mitigate risks:
- Conduct Internal Investigations — Validate whether their data has been compromised.
- Force Credential Resets — Especially for exposed user accounts and internal systems.
- Monitor Dark Web Activity — Track any further انتشار or sale of their data.
- Enhance Security Controls — Implement stronger access controls, logging, and anomaly detection.
- Engage Incident Response Teams — To contain and remediate any breaches effectively.
Users are also advised to:
- Change passwords across critical accounts
- Enable multi-factor authentication (MFA)
- Stay alert for suspicious emails or login attempts
Final Thoughts
This incident highlights the growing sophistication and persistence of cybercriminal operations. The emergence of such leaks on the dark web underscores the importance of proactive security measures, continuous monitoring, and rapid response capabilities.
As more details unfold, both organisations and individuals must remain vigilant and adopt a security-first mindset in an increasingly hostile digital environment.