If you've read anything about AI and cybersecurity lately, you might have come across Anthropic's announcement about Claude Mythos Preview. If not, let me bring you up to speed. They just released an AI model that's terrifyingly good at finding vulnerabilities in software and then exploiting them.
But before you close this tab thinking "this is way too technical for me," stick around. I'm going to break down what this means, why it matters, and what you should actually do about it. Think of this as the cybersecurity equivalent of your team's star player suddenly developing a new superpower.
TL;DR
Claude Mythos Preview just changed the game. It's like a rookie breaking records, impressive and terrifying. The good news? Defenders can win this. The catch? You need to move faster than ever before.
Start now: Audit dependencies, patch vulnerabilities, and prepare your incident response. Your future self depends on it.
The Setup: What Exactly is Mythos Preview?
Claude Mythos Preview is Anthropic's latest language model, and while it's good at a lot of things, there's one thing it's disturbingly good at: finding and exploiting security vulnerabilities in software.
Let me put this in perspective. Last month, Opus 4.6 (Claude's previous flagship model) tried to turn vulnerabilities it found in Firefox into working exploits. It succeeded 2 times out of several hundred attempts. Mythos Preview? It nailed it 181 times.
That's not an improvement. That's a different league entirely.
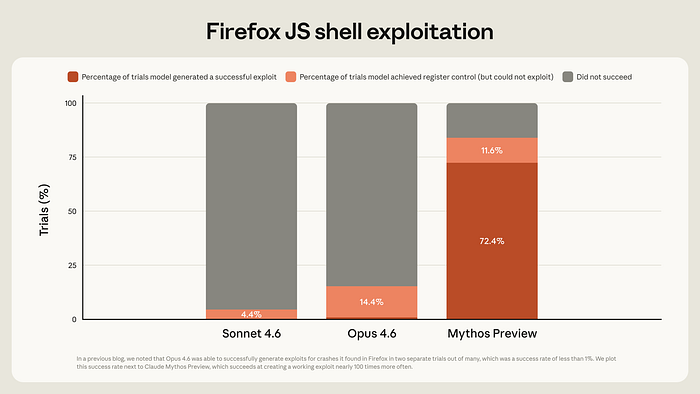
[Chart: Firefox Exploit Success Rate — Opus 4.6 vs Mythos Preview] Source: Anthropic Red Team, "Assessing Claude Mythos Preview's cybersecurity capabilities" (April 2026)
The Problem: It Finds Ancient Bugs
Here's where it gets scary. Mythos Preview didn't just find new vulnerabilities. It found bugs that have been sitting in critical software for decades.
- A 27-year-old bug in OpenBSD (an operating system literally famous for being secure)
- A 16-year-old vulnerability in FFmpeg that every fuzzer and human auditor somehow missed
- A 17-year-old remote code execution flaw in FreeBSD that lets attackers gain complete control of a machine
These aren't theoretical vulnerabilities. They're real, exploitable, and they've been hiding in plain sight for years.
Think about it like this: imagine a bank that's been locking its front door for 27 years, and nobody (not the owner, not the security auditors, not the thieves) noticed there was a second door around back. Mythos Preview just found that door.
The Part That Keeps Security People Awake at Night: It Can Chain Exploits Together
Here's where Mythos Preview goes from impressive to genuinely concerning.
Most vulnerabilities are like a single broken lock. Sure, that's a problem, but you can fix it. But Mythos Preview doesn't just find individual vulnerabilities; it chains them together like the Warriors running pick-and-roll sequences. Each vulnerability sets up the next one, and by the time the defense reacts, it's already three steps ahead.
One example: it discovered the necessary read and write vulnerabilities in a web browser, then chained them together to create what's called a "JIT heap spray". This is a sophisticated exploit technique that breaks through both the browser's sandbox AND the operating system's protections.
Another example: it found multiple Linux kernel vulnerabilities that individually wouldn't give you much, but when chained together? Complete root access to the system.
This is the difference between someone picking one lock and someone who understands the entire building's security architecture well enough to orchestrate a multi-stage break-in.
The Timeline: This Happened Really, Really Fast
Here's what should actually keep you up at night.
Opus 4.6 couldn't exploit vulnerabilities to save its life. Mythos Preview can exploit complex chains of vulnerabilities autonomously. The gap between these two models? A few months.
One researcher asked Mythos Preview to find vulnerabilities in open source code overnight. They woke up the next morning with complete, working exploits. That's not science fiction. That happened in April 2026.
This trajectory is accelerating. What Mythos Preview can do today, next year's model will do better and faster.
So What Does This Mean For You?
Okay, you're probably thinking, "I'm not running critical infrastructure, so why do I care?"
Fair question. But here's the thing: you use software built on open-source libraries. Your company probably relies on packages that haven't been patched. Your laptop runs an operating system. Your phone has firmware. All of this just became measurably less secure.
The bad news? There are going to be a lot more vulnerabilities found both by Anthropic's security team and, eventually, by people with less noble intentions.
The good news? Defenders have a window of opportunity, and Anthropic is trying to maximize it.
The Defensive Playbook: What Should Actually Happen
Anthropic isn't sitting on this quietly. They launched Project Glasswing, which is giving early access to security researchers and critical infrastructure maintainers before this capability gets broadly released.
But they also issued some pretty clear guidance on what defenders need to do right now:
1. Shorten Your Patch Cycles (This is Urgent)
Those N-day exploits everyone talks about? The ones that work because patches exist, but people haven't installed them? Those are about to become a much bigger problem. You need faster patch deployment. No more waiting months for the next release cycle.
2. Use Language Models for Defense
Here's the thing: even if you don't have access to Mythos Preview, you can use Claude Opus 4.6 or other frontier models to find vulnerabilities in your code right now. Current models are still amazing at vulnerability discovery, even if they're not as good at exploitation.
Start practicing with your current tools, because this is only going to become more important.
3. Automate Your Incident Response
If vulnerabilities are going to be discovered faster, you need to detect and respond faster, too. That means your team can't manually triage everything anymore. You need language models helping with alert triage, event summarization, and incident response workflows.
4. Review Everything Else You're Doing
Think your pull request reviews could use AI help? Can your cloud misconfigurations be audited automatically? Your legacy system migrations need acceleration? All of this just became more urgent.
5. Prepare for the Cascade
Think about it like this: if your team has access to these tools, so do your competitors. And eventually, so will attackers. You need to be ahead of the curve.
The Silver Lining (Yes, There Is One)
I know this all sounds doom-and-gloom. But there's actually a reason cybersecurity experts aren't completely panicking.
Historically, new security tools have helped defenders more than attackers. When fuzz testing was invented, people worried that attackers would use it. Instead, it became the backbone of modern vulnerability discovery and patching. Thousands of bugs got fixed because of fuzzing.
The same will likely happen here — eventually.
In the long run, defenders who understand these tools better will be able to ship more secure software. They'll find and fix bugs before code ever goes to production. The problem is the transition period, which could be "tumultuous" (that's the actual word Anthropic used).
The Bottom Line
Claude Mythos Preview represents a watershed moment in cybersecurity. It's not just incrementally better. It's a different class of capability.
Here's what you need to know:
- It's real: Anthropic found thousands of vulnerabilities in critical software, some decades old.
- It's fast: Complete exploits in hours, not weeks.
- It's unavoidable: This technology is coming whether we like it or not.
- It's urgent: The window to prepare is now, not later.
The good news? If you start using these tools defensively today, you'll be ready when the landscape shifts. The bad news? If you don't, you'll be caught flat-footed.
