Overview
The Takeover room focuses on reconnaissance techniques used to discover hidden assets of a web application. The challenge demonstrates how subdomain enumeration and certificate inspection can reveal additional domains that may expose sensitive information.
In this room, the goal is to identify hidden subdomains associated with the target domain and analyze them to locate the flag.
Key concepts demonstrated in this challenge include:
- Network enumeration using Nmap
- Subdomain discovery using FFUF
- Host resolution through the hosts file
- Information gathering through SSL certificate analysis
This room highlights how small pieces of publicly accessible information can lead to the discovery of hidden resources.
Initial Enumeration
Performing a port scan on the target machine using Nmap.
nmap -vv <target-ip>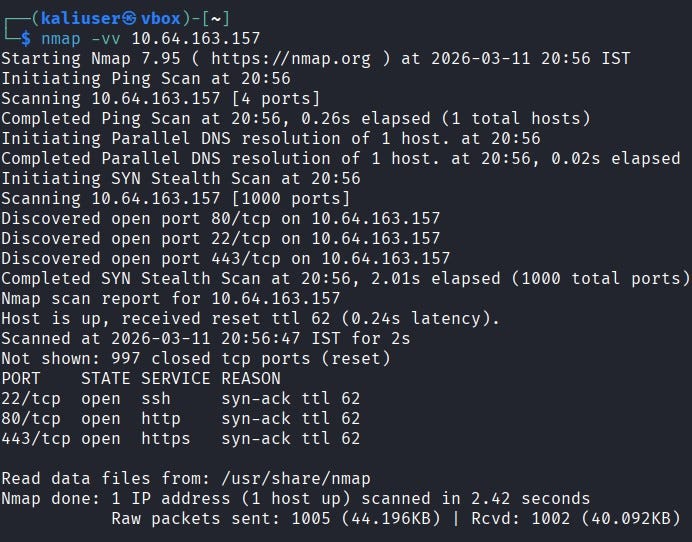
The scan reveals that three ports are open:
- 22 — SSH
- 80 — HTTP
- 443 — HTTPS
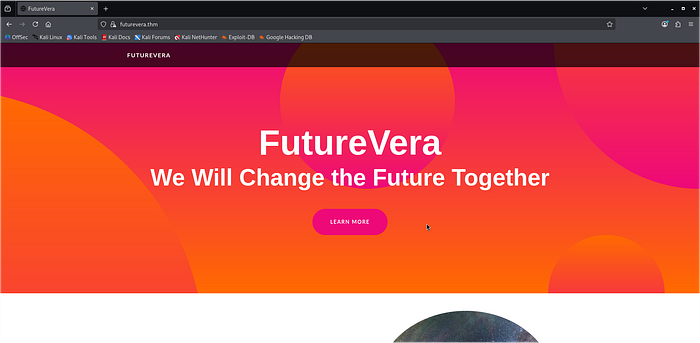
Attempting to access the website through HTTP (port 80) did not load the page correctly.
Next, the HTTPS service (port 443) was tested, but the domain was not resolving.
To resolve this issue, the target domain was added to the hosts file.
echo "<target ip> futurevera.thm" >> /etc/hostsAfter updating the hosts file, the website became accessible.
Subdomain Enumeration
After inspecting the main page, no useful information was found.
The next step was to perform subdomain enumeration using FFUF.
ffuf -u https://10.64.163.157 -H "Host: FUZZ.futurevera.thm" -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt -fs 0,4605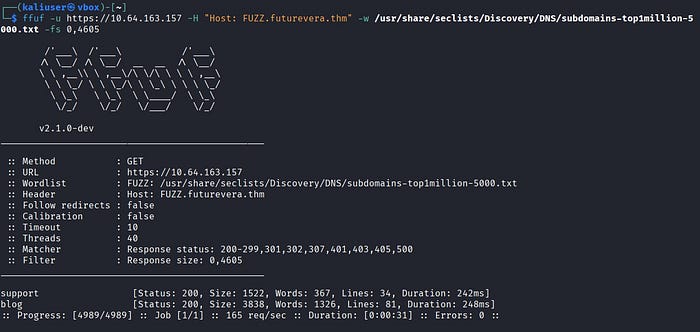
The scan discovered two subdomains:
- support.futurevera.thm
- blog.futurevera.thm
However, these subdomains did not initially resolve.
To fix this, both subdomains were added to the hosts file.
echo "<target ip> support.futurevera.thm" >> /etc/hosts
echo "<target ip> blog.futurevera.thm" >> /etc/hostsAfter doing this, both websites loaded successfully.

Investigating the Websites
Both websites were inspected manually. However, no visible clues or sensitive information were found.Since the support site uses HTTPS, the SSL certificate was inspected for additional information.
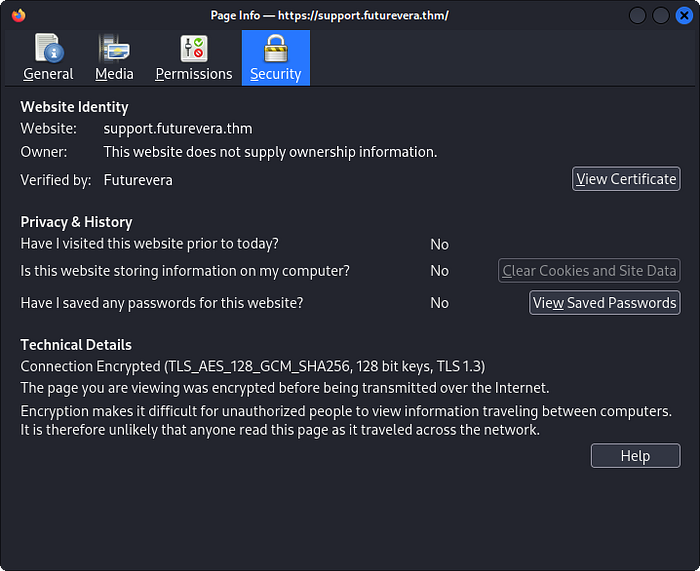
In the certificate details, a DNS name was discovered under the Subject Alternative Name (SAN) section.
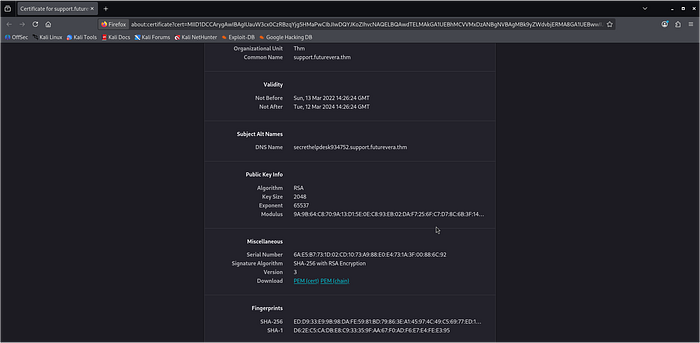
Discovering the Flag
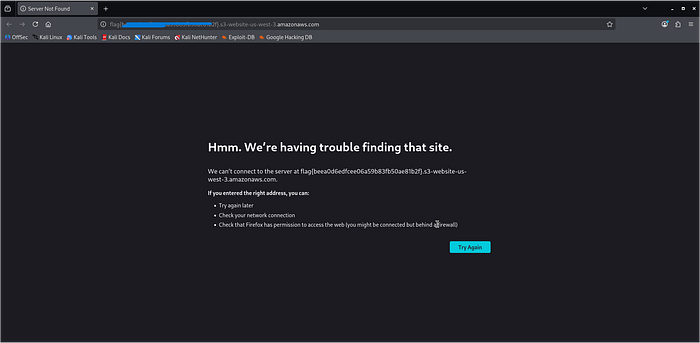
The discovered DNS name was searched in the browser.
Upon accessing that domain, the flag was revealed.
Conclusion
This room demonstrates how simple reconnaissance techniques can reveal hidden assets in a web environment.
Key takeaways from this challenge:
- Subdomain enumeration can uncover hidden services.
- The hosts file can be used to manually resolve discovered domains.
- SSL certificates often contain additional domain information in the Subject Alternative Name (SAN) field.
- Even small misconfigurations can expose sensitive information.