Web applications face constant threats — from SQL injection to cross-site scripting (XSS) and API abuse. Organizations that deploy code frequently need a security solution that is accurate, scalable, and automation-friendly. That's where Invicti comes in.
In this guide, you'll learn what Invicti is, how it works, its key features, real-world use cases, and how it compares to other web application security scanners.
Official website: 👉 https://www.invicti.com/
What Is Invicti?
Invicti is an enterprise-grade Dynamic Application Security Testing (DAST) platform designed to detect vulnerabilities in live web applications and APIs.
It evolved from well-known security tools such as:
- Netsparker
- Acunetix
Today, these technologies are unified under the Invicti platform.
Unlike static code scanners, Invicti tests applications while they are running, simulating real attacker behavior.
Why Web Application Security Matters
Web applications are common targets because they are publicly accessible. Common vulnerabilities include:
- SQL Injection (SQLi)
- Cross-Site Scripting (XSS)
- Cross-Site Request Forgery (CSRF)
- Authentication bypass
- Broken access control
- Misconfigured security headers
Many of these risks are documented in the OWASP Top 10.
Without automated scanning, vulnerabilities can remain undetected until exploited.
How Invicti Works
Invicti performs automated vulnerability scanning by:
- Crawling your web application
- Mapping endpoints and parameters
- Injecting safe test payloads
- Validating exploitability
- Generating detailed remediation reports
Its standout feature is Proof-Based Scanning™.
What Is Proof-Based Scanning?
Many scanners report "potential" vulnerabilities. That creates:
- False positives
- Wasted verification time
- Developer fatigue
Invicti automatically verifies vulnerabilities by safely exploiting them, proving they are real.
For example:
If a login form is vulnerable to SQL injection, Invicti will:
- Inject a test payload
- Confirm database response manipulation
- Provide evidence in the report
- Include remediation guidance
This reduces noise and increases confidence.
Key Features of Invicti
1️⃣ Automated Web Application Security Scanning
Invicti detects:
- Injection flaws
- XSS vulnerabilities
- Security misconfigurations
- Server-side request forgery
- API vulnerabilities
- Authentication issues
It supports modern technologies including:
- Single Page Applications (SPAs)
- REST APIs
- GraphQL APIs
- JavaScript-heavy frontends
2️⃣ CI/CD Integration for DevSecOps
Security must be continuous. Invicti integrates with:
- GitHub
- GitLab
- Azure DevOps
- Jenkins
- Jira
- Slack
This enables:
- Automated scans during builds
- Blocking deployments with critical vulnerabilities
- Automatic ticket creation for developers
This is essential for organizations practicing DevSecOps.
3️⃣ API Security Testing
APIs are often overlooked attack surfaces.
Invicti allows you to:
- Import OpenAPI/Swagger definitions
- Authenticate against secured endpoints
- Test token-based authentication
- Detect injection flaws in API parameters
With the rise of microservices, this is critical.
4️⃣ Enterprise-Level Scalability
Large organizations benefit from:
- Role-based access control
- Centralized dashboards
- Compliance reporting
- Multi-target scanning
- Asset discovery
Invicti is built to handle hundreds or thousands of applications.
Real-World Use Cases
Example 1: SaaS Company With Weekly Releases
A SaaS platform deploys code every week.
Before Invicti:
- Manual security reviews
- Delayed releases
- Missed vulnerabilities
After integrating Invicti:
- Automated scans run in CI pipeline
- Developers receive tickets instantly
- High-risk issues block production
- Faster and safer releases
Example 2: Financial Institution Needing Compliance
A financial company must meet:
- PCI DSS
- ISO 27001
- SOC 2
Invicti provides:
- Scheduled scans
- Audit-ready reports
- Evidence-based vulnerability confirmation
This simplifies compliance validation.
Example 3: API-Heavy Microservices Environment
A company running dozens of APIs integrates Invicti to:
- Automatically scan new endpoints
- Validate authentication flows
- Detect injection flaws in JSON payloads
This prevents exposed backend services.
Invicti vs Traditional Web Vulnerability Scanners
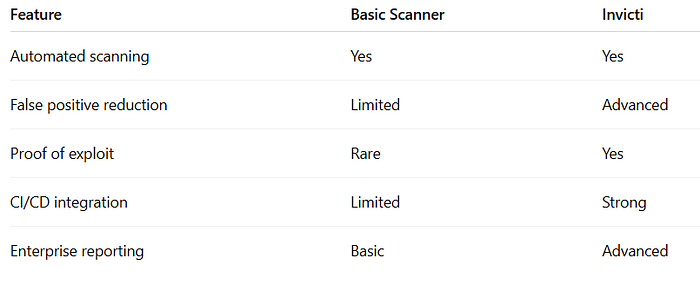
The key differentiator is verified vulnerability detection.
Is Invicti Free?
Invicti is a commercial security platform with custom pricing.
However, organizations can request:
- Product demos
- Trial access
- Consultations
Pricing depends on:
- Number of applications
- Deployment model (cloud or on-premises)
- Enterprise features required
More information: 👉 https://www.invicti.com/pricing/
Best Practices When Using Invicti
- Scan staging environments before production
- Integrate into CI/CD early
- Review high-risk findings first
- Combine DAST with SAST tools
- Schedule recurring scans
A layered approach improves overall application security posture.
Who Should Use Invicti?
Invicti is ideal for:
- Enterprise security teams
- DevSecOps engineers
- Financial institutions
- SaaS providers
- Government agencies
- Organizations with large web app inventories
If your business relies heavily on web applications and APIs, automated and verified scanning is essential.
Final Thoughts
Invicti is a powerful enterprise web application security scanner designed to detect and verify real vulnerabilities in modern web applications and APIs. Its Proof-Based Scanning, CI/CD integration, and enterprise reporting capabilities make it a strong choice for organizations that prioritize accuracy and scalability.
As web threats continue to evolve, proactive vulnerability scanning and continuous security testing are no longer optional — they are critical.
Thank you for reading this blog article.

More books available on Amazon. Click my Authors page link to check them all out — Dennis Duke Authors Page
If you like this blog and want to read more feel free to follow me on Medium. More to come and thanks for the support.
You can find more of my blog articles here

