Turning a technical implementation into a sustainable program — adoption strategies, governance models, and the holistic security posture view that ties FAST SAST and DEEP SAST together.
You've got the architecture, the tool, the lifecycles, and the metrics. Now comes the hardest part: getting hundreds of development teams across multiple business units to actually use it, trust it, and benefit from it. This is where SAST programs live or die.
The Adoption Challenge
The single biggest mistake organizations make when rolling out a SAST program is treating it as a top-down security mandate. Adoption has to be earned, not mandated. It's earned through three things: demonstrating value on a small scale first, making the developer experience frictionless, and being transparent about the program's own quality metrics.
The Phased Rollout Strategy
- Phase 1 (Foundation): Controlled POC with Champions. Start with 2–3 teams running in warn-only mode to tune rules and collect FPR data.
- Phase 2 (Early Adopters): Expand to Willing Teams. Keep block mode limited to highest-confidence rules. Build the triage and PR annotation experience based on real feedback.
- Phase 3 (BU-Level Rollout): Business Unit by Business Unit. Each BU gets a security champion. Enable block mode for proven high-confidence rules.
- Phase 4 (Organization-Wide): Default-On for All Repos. Teams can request exceptions, but the default is on.
At each phase, the key question is not "how many repos are scanned?" but "are the teams that are scanned finding the program useful?" Premature scaling of a broken experience creates organizational antibodies.
Governance Model
Governance is the connective tissue between the technical implementation and organizational adoption. Without it, you have a tool. With it, you have a program.
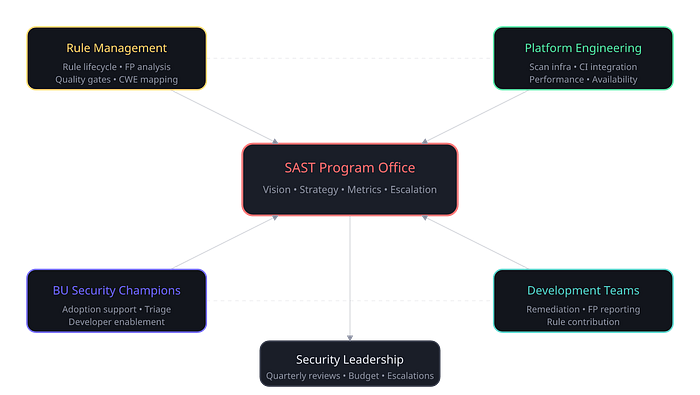
The SAST Program Office sits at the center and owns the overall vision, strategy, and metrics. It coordinates between four stakeholder groups:
- Rule Management Team: Rule quality and lifecycle.
- Platform Engineering: Scanning infrastructure and CI integration.
- BU Security Champions: Adoption support within their business unit.
- Development Teams: Consumers and rule contributors.
- Security Leadership: Quarterly review and budget oversight.
The Three Stakeholder Views Different stakeholders need different views built into your dashboard:
- Developer View: Wants a holistic risk view. Summarize security posture, show open PR scan results, and allow them to trace findings.
- Rule Owner View: Wants a rules summary lens. Which rules have the highest FPR? Which fire most often? Needs alerts for threshold breaches.
- Leadership View: Wants program-level health metrics. Fix rates trending over time, coverage percentages, and ROI (e.g., TTR improvements).
The Holistic View: Combining FAST and DEEP SAST
The ultimate goal is not two separate programs running in parallel — it's a unified security posture that combines the speed of FAST SAST with the depth of DEEP SAST.
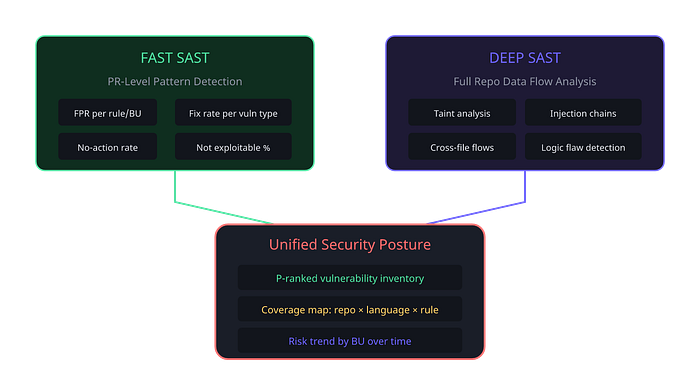
The combined metrics include shared items like FPR, TPR, and not exploitable rate — sliced across both scan types. You also need coverage metrics mapping your total code footprint: how many eligible repos are enrolled, languages covered, and whether top vulnerability types have corresponding rules. Tracking this prevents a false sense of security.
Lessons from the Trenches
After leading this transformation at a major enterprise, here are the lessons that don't fit neatly into any framework:
Developer Trust is Your Most Scarce Resource Every false positive costs you trust. Every scan that adds 90 seconds to a pipeline costs you trust. Trust doesn't scale linearly — losing it is exponential, and rebuilding it takes years. Starting with a low-FPR, fast-scan approach is the only viable path.
Split Your Bets: FAST + DEEP Splitting into FAST SAST and DEEP SAST was the most consequential architectural choice. It allowed us to optimize speed for FAST and depth for DEEP without compromise. FAST SAST is a productivity tool; DEEP SAST is an analysis tool.
Metrics Drive Behavior — Choose Them Carefully If you measure "number of findings," teams will tune rules to fire more. Measure "fix rate" without the FPR denominator, and teams mark everything as fixed. Design metrics to create balanced incentives: precise rules, responsive developers, improving coverage.
Open Questions Are a Feature, Not a Bug At the end of every lifecycle document, keep a section of open questions. Acknowledging what you don't know yet builds more credibility with stakeholders than pretending you have all the answers.
The Bottom Line A successful SAST program is 20% tooling and 80% everything else — the vision that gets buy-in, the evaluation that builds confidence, the lifecycles that create predictability, the metrics that maintain accountability, the governance that scales adoption, and the humility to keep improving. Get the fundamentals right, and the tools will do their job. Skip them, and no tool in the world will save you.
The principles in this series are drawn from a real enterprise SAST transformation. Every organization's journey will be different, but the fundamentals — split the problem, earn trust, measure honestly, scale carefully — are universal.