In this article, I'll walk through a hands-on lab where I explored how a Remote Code Execution (RCE) vulnerability can be exploited in an IPv6-enabled environment. The exercise was carried out in a fully controlled setup, with the goal of understanding real-world attack techniques and strengthening defensive awareness.
Lab Setup
To simulate a realistic attack scenario, I used the following environment:
- Attacker Machine: Kali Linux
- Target Machine: Metasploitable 3 running Windows Server 2008 R2 (with IPv6 enabled)
- Tools & Frameworks: Nmap and Metasploit Framework
- Exploit Used: EternalBlue
This setup allowed me to safely replicate a vulnerable enterprise-like environment and test exploitation techniques without any real-world risk.
Step 1: Network Reconnaissance
The first step in any penetration testing workflow is reconnaissance. I began by scanning the network using a TCP SYN scan with Nmap. This helped identify active hosts and open ports within the network.
Through this scan, I was able to detect that the target system had SMB services exposed, which is a common entry point in many real-world attacks.
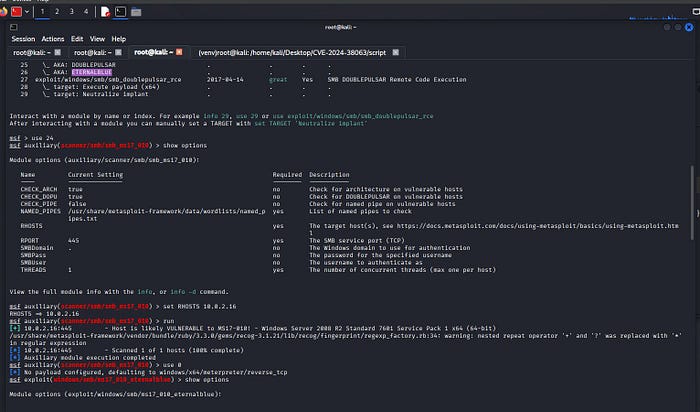
Step 2: Identifying the Vulnerability
After identifying open SMB ports, I focused on checking for known vulnerabilities. The scan results indicated that the system was likely vulnerable to MS17–010, a critical flaw in SMBv1.
This vulnerability is widely known due to its use in large-scale cyberattacks such as WannaCry, making it an important case study for both offensive and defensive security professionals.
Step 3: Exploitation with EternalBlue
To exploit the identified vulnerability, I used the EternalBlue module available in the Metasploit Framework.
Once configured correctly, the exploit was launched against the target system. The attack was successful, and I gained access to the system with NT AUTHORITY\SYSTEM privileges, the highest level of access on a Windows machine.
This step clearly demonstrated how unpatched systems can be completely compromised with publicly available tools.
Step 4: Post-Exploitation Analysis
After gaining access, I moved into the post-exploitation phase to gather more information about the compromised system.
During this stage, I:
- Accessed the system shell
- Identified the IPv6 link-local address of the machine
- Traced the associated MAC address
- Explored the network configuration for further insights
This phase is critical because attackers often use it to expand their access, move laterally, or maintain persistence within a network.
Step 5: Remote Code Execution via Python
To extend the attack scenario, I used a custom Python script to execute commands remotely on the compromised system.
This demonstrated how an attacker, after gaining initial access, can automate tasks and execute arbitrary code effectively taking full control of the target environment.
Key Takeaways
This lab provided several important insights:
- IPv6 environments can introduce additional attack surfaces if not properly secured
- Legacy vulnerabilities like MS17–010 remain highly dangerous if left unpatched
- The exploitation process follows a clear methodology: reconnaissance → exploitation → post-exploitation
- Tools like Metasploit significantly simplify complex attack techniques
- Post-exploitation is where attackers gain real operational control
Final Thoughts
While this lab focused on offensive techniques, the ultimate goal is defensive improvement. Understanding how these attacks work helps organizations better secure their infrastructure.
Regular patching, disabling outdated protocols like SMBv1, and monitoring network activity are essential steps in preventing such attacks.
Disclaimer: This experiment was conducted in a controlled lab environment strictly for educational and ethical cybersecurity research purposes.