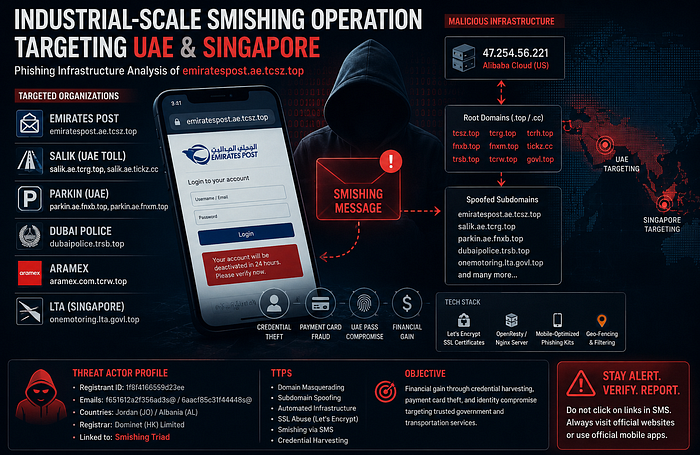
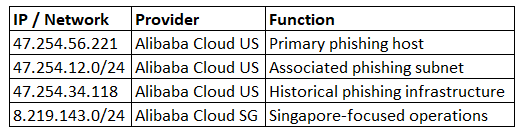
A large-scale phishing and smishing infrastructure has been identified leveraging spoofed UAE and Singapore government, transportation, and logistics brands through dynamically generated subdomains hosted primarily on Alibaba Cloud infrastructure. My investigation centered on the phishing domain emiratespost.ae.tcsz.top and the hosting IP 47.254.56.221 revealed a coordinated phishing-as-a-service (PhaaS) ecosystem exhibiting characteristics strongly aligned with operations commonly associated with the "Smishing Triad" threat cluster.
The campaign heavily abuses .top and .cc domains, using short randomized root domains combined with legitimate organization names as deceptive subdomains. The infrastructure targets high-trust public-facing services, including Emirates Post, Salik, Parkin, Dubai Police, Aramex, and Singapore's Land Transport Authority (LTA).
The operational objective is assessed with high confidence to be financial fraud through credential harvesting, payment card theft, and potential compromise of national digital identity platforms such as UAE Pass. The infrastructure demonstrates signs of industrial-scale automation, including rapid domain provisioning, SSL certificate issuance, geo-targeted phishing delivery, and centralized hosting architecture.
1. Threat Overview
1.1 Campaign Characteristics
The identified infrastructure represents a mature smishing ecosystem designed to impersonate trusted government and transportation services across the UAE and Singapore. The campaign employs:
- High-volume domain registration
- Dynamic phishing subdomain generation
- Mobile optimized credential harvesting portals
- Centralized hosting infrastructure
- Regional geo-fencing capabilities
- Automated SSL certificate deployment
The infrastructure primarily abuses short four-character root domains under the .top and .cc TLDs, which are commonly leveraged in phishing campaigns due to low registration costs, weak abuse enforcement, and rapid provisioning capabilities.
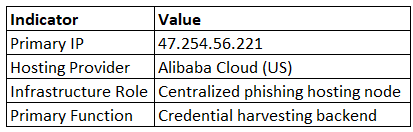
2. Infrastructure Analysis
2.1 Core Infrastructure
Primary Hosting Node
2.2 Domain Naming Convention
The threat actor utilizes a structured naming methodology:
[legitimate-service].[country-domain].[actor-root-domain]Examples

This structure intentionally creates visual legitimacy, especially on mobile devices where URLs are often truncated.
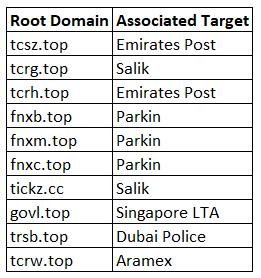
3. Targeted Organizations
3.1 UAE-Focused Targeting
The operation demonstrates a strong concentration on UAE public services and transportation infrastructure.
Identified UAE Targets
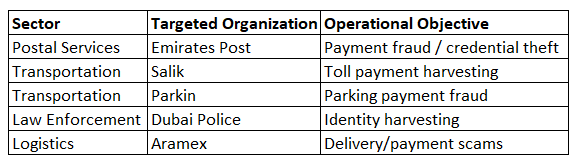
3.2 Singapore-Focused Targeting
Singapore's infrastructure targeting suggests regional expansion beyond Gulf countries.
Target: Singapore LTA
Domain: onemotoring.lta.govl.top
The selection of transportation and government services indicates the actor prioritizes entities associated with recurring payments, vehicle registration, and identity verification.
4. Tactics, Techniques, and Procedures (TTPs)
4.1 MITRE ATT&CK Mapping
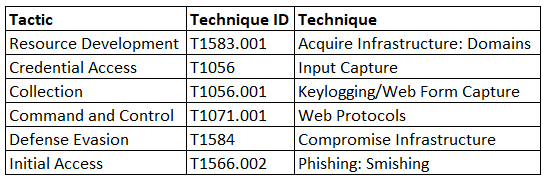
4.2 Domain Masquerading
The infrastructure relies heavily on domain impersonation techniques:
- Abuse of legitimate UAE domains as subdomains
- Use of short randomized actor-controlled root domains
- Use of visually trusted naming structures
- Rapid rotation between root domains
Examples include:
- tcsz.top
- tcrg.top
- fnxb.top
- tickz.cc
4.3 SSL Certificate Abuse
The actor deploys Let's Encrypt certificates to:
- Increase user trust
- Bypass basic security controls
- Enable HTTPS encryption
- Improve phishing page legitimacy
Observed certificate pattern:
Serial: 60a675df0cdeaf9a4e0369ebc39162e5bf44.4 Geo-Fencing and Traffic Filtering
The phishing infrastructure selectively serves malicious content based on geographic targeting.
Observed targeting includes:
- UAE IP ranges
- Singapore IP ranges
This significantly reduces exposure to:
- Security researchers
- Automated crawlers
- Sandboxes
- Global scanning engines
5. Registrant and Attribution Analysis
5.1 WHOIS and Registration Patterns
Observed Registrant Indicators
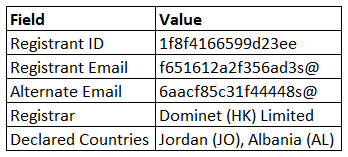
The registrant information is likely synthetic or obfuscated, consistent with industrialized phishing infrastructure.
5.2 Connection to Smishing Triad
The infrastructure strongly aligns with publicly documented "Smishing Triad" tradecraft based on:
- High-volume .top domain abuse
- Mobile-oriented phishing workflows
- SMS-driven lure delivery
- Alibaba Cloud hosting
- Transportation/payment targeting
- Credential harvesting operations
Assessment
While definitive attribution remains difficult, the overlap in infrastructure patterns, hosting behavior, and phishing methodology strongly suggests operational similarities with Smishing Triad ecosystems.
6. Additional Infrastructure Identified
6.1 Related Root Domains
The following root domains are linked through shared registration patterns and infrastructure overlap:
6.2 Infrastructure Pivoting
Related Infrastructure
7. Phishing Workflow Analysis
7.1 Attack Chain
The phishing lifecycle appears structured as follows:
SMS Delivery
↓
Victim clicks phishing URL
↓
Redirect to spoofed domain
↓
Mobile phishing page displayed
↓
Credential/payment data entered
↓
Data exfiltrated to backend server
↓
Potential 2FA interception7.2 Phishing Kit Analysis
Observed Components
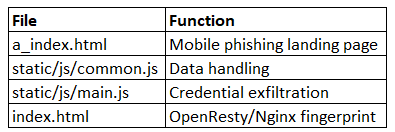
Technical Characteristics
The phishing kit demonstrates:
- Mobile-first optimization
- JavaScript-based credential exfiltration
- Responsive UI cloning
- Backend filtering logic
- Session management
8. Strategic Assessment
8.1 Operational Objective
The campaign's primary motivation is assessed as:
Financially Motivated Credential Theft
Likely targeted data includes:
- Credit card details
- Banking credentials
- UAE Pass credentials
- Toll/parking payment accounts
- Personal identity information
8.2 Regional Implications
The campaign highlights several broader trends:
Increasing Regional Smishing Activity
The UAE and Singapore remain attractive targets due to:
- High digital payment adoption
- Centralized e-government services
- Widespread mobile service integration
- Strong public trust in digital infrastructure
Transportation Sector Abuse
Transportation and toll services provide ideal phishing themes because:
- Users expect frequent payment notifications
- Mobile interactions are common
- Small-value payment requests reduce suspicion
- Urgency messaging is effective
9. Detection Opportunities
9.1 Network Indicators
Suspicious Characteristics
- The .top and .cc domains are impersonating government entities
- Four-letter randomized root domains
- Alibaba Cloud hosted phishing infrastructure
- OpenResty/Nginx phishing servers
- Let's Encrypt certificates with short lifecycle patterns
9.2 Detection Logic Recommendations
High Confidence Detection Patterns
*.ae.[4-letter].top
*.govl.top
*.tickz.cc
*.fnx*.top
*.tcr*.topBehavioral Indicators
- Mobile user-agent targeting
- Geo-fenced content delivery
- Rapid DNS rotation
- HTTP POST credential exfiltration
10. Conclusion
The infrastructure associated with emiratespost.ae.tcsz.top and 47.254.56.221 represents a highly automated, industrialized smishing ecosystem targeting UAE and Singapore transportation, logistics, and government services. The campaign demonstrates mature phishing tradecraft, including infrastructure automation, geo-targeting, SSL abuse, and mobile-optimized credential harvesting workflows.
The observed infrastructure patterns strongly align with known Smishing Triad operational characteristics, indicating the continued evolution of large-scale phishing-as-a-service ecosystems focused on high-trust digital government environments.
The campaign underscores the growing convergence between mobile phishing, transportation sector abuse, and regional digital identity ecosystems across the Middle East and Southeast Asia.