Introduction
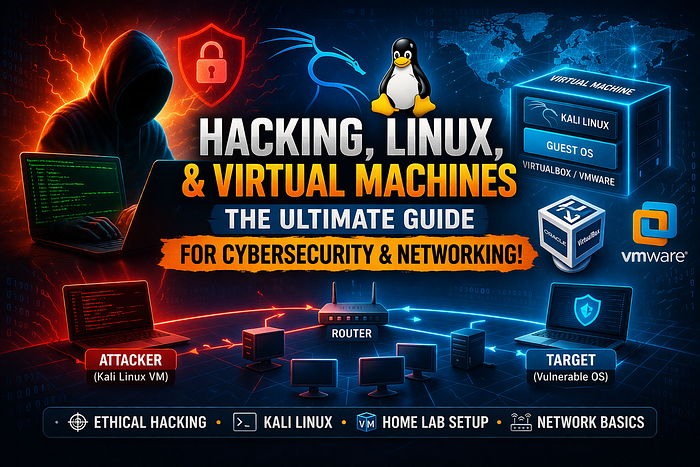
In today's digital world, cybersecurity has become one of the most critical fields in technology. Concepts like hacking, virtual machines, Linux, and networking are deeply interconnected and form the foundation of modern cybersecurity practices. Whether you are a beginner or an aspiring ethical hacker, understanding how these components work together is essential for building secure systems and identifying vulnerabilities.
What is Hacking?
Hacking is often misunderstood as illegal activity, but in reality, it has both ethical and malicious aspects. Ethical hacking, also known as penetration testing, involves testing systems and networks to find vulnerabilities before attackers can exploit them. Kali Linux is one of the most popular platforms used for this purpose, as it comes pre-installed with numerous tools for security testing and analysis.
Ethical hackers simulate real-world attacks to strengthen defenses. For example, they may scan a network to identify open ports, test passwords, or analyze web applications for weaknesses. This proactive approach helps organizations improve their security posture.
Role of Linux in Cybersecurity
Linux plays a central role in hacking and cybersecurity. Unlike traditional operating systems, Linux offers greater control, flexibility, and transparency. Most hacking tools are designed to run on Linux because of its powerful command-line interface and open-source nature.
Distributions like Kali Linux are specifically built for penetration testing. They include tools for:
- Network scanning (e.g., Nmap)
- Packet analysis (e.g., Wireshark)
- Exploitation frameworks (e.g., Metasploit)
Linux also allows users to interact directly with system processes, making it easier to analyze vulnerabilities and perform advanced security tasks. Mastering Linux is often considered the first step toward becoming a skilled ethical hacker.
Virtual Machines: Safe Learning Environment
A Virtual Machine (VM) is a software-based computer that runs inside your physical system. Tools like VirtualBox or VMware allow users to install multiple operating systems on a single machine.
Virtual machines are extremely important in cybersecurity because they provide:
- Isolation: You can test hacking tools without affecting your main system.
- Snapshots: Easily revert to previous states.
- Flexibility: Run multiple environments simultaneously.
For example, a student can run Kali Linux inside a VM on a Windows laptop and practice ethical hacking safely. This setup is commonly called a "home lab."
Networking: The Backbone of Cybersecurity
Networking is the foundation of all hacking and cybersecurity activities. Every system connected to the internet communicates through networks, making them a primary target for attackers.
Key networking concepts include:
- IP Addressing: Identifies devices on a network
- Ports and Services: Entry points for communication
- Protocols: Rules for data transfer (e.g., HTTP, TCP/IP)
Hackers use networking knowledge to scan systems, detect vulnerabilities, and exploit weaknesses. For example, identifying an open port running an outdated service can lead to a potential attack vector.
Practical Integration: How Everything Works Together
To truly understand cybersecurity, you need to combine all these elements:
- Use a virtual machine to create a safe environment
- Install Linux (like Kali Linux) inside the VM
- Learn networking basics
- Practice ethical hacking techniques
This integrated approach allows learners to simulate real-world scenarios. For instance, one VM can act as an attacker (Kali Linux), while another acts as a target system.
Important Insight
One crucial thing to remember is that hacking should always be done ethically and legally. Unauthorized access to systems is illegal and punishable by law. Always practice in controlled environments like virtual labs or authorized platforms.
Conclusion
Hacking, Linux, virtual machines, and networking are deeply interconnected domains that form the backbone of cybersecurity. Linux provides the tools, virtual machines offer a safe environment, and networking connects everything together. By mastering these areas, individuals can build strong skills in ethical hacking and contribute to a safer digital world.