Introduction to DOM Based Vulnerabilities
The Document Object Model (DOM) is a fundamental concept in web development, representing a hierarchical structure of elements on a web page. It allows JavaScript to interact with and manipulate the page's content, creating a dynamic and engaging user experience. However, when JavaScript handles user-controlled data insecurely, it can lead to various attacks, compromising the security of the website and its users. In this article, we will delve into the world of DOM-based vulnerabilities, exploring what they are, how they arise, and the potential risks they pose.
What is the Document Object Model (DOM)?
The DOM is a programming interface for HTML and XML documents, representing a tree-like structure of nodes and objects. It enables JavaScript to access, modify, and manipulate the elements on a web page, creating a dynamic and interactive experience. The DOM is not a vulnerability in itself, but rather a framework that can be exploited by malicious JavaScript code.
Understanding DOM-Based Vulnerabilities:
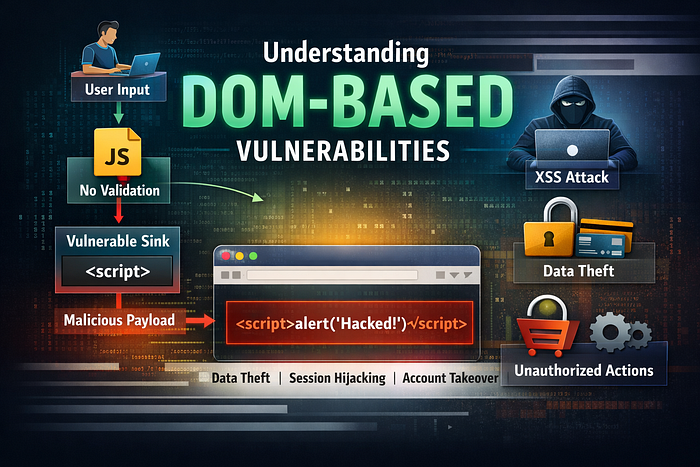
DOM-based vulnerabilities arise when a website's JavaScript code takes user-controlled values, known as the "source," and passes them to a dangerous function, known as the "sink." This can happen when user input is not properly sanitized or validated, allowing an attacker to inject malicious code into the website. The sink function can be any method that can cause harm, such as executing arbitrary code, stealing sensitive data, or performing unauthorized actions.
SOURCE → JAVASCRIPT → SINK (User) → (Logic) → (Dangerous Function)
If input is not validated → DOM-Based Vulnerability If validated & sanitized → Secure Application
Real-World Examples of DOM-Based Vulnerabilities:
To illustrate the concept of DOM-based vulnerabilities, let's consider a few examples:
- A web application uses JavaScript to display user-inputted data on a page. An attacker injects malicious code into the input field, which is then executed by the JavaScript code, allowing the attacker to steal sensitive data or perform unauthorized actions.
- A website uses a JavaScript library to handle user input, but the library is not properly configured, allowing an attacker to inject malicious code into the library's functions.
- A web application uses JavaScript to dynamically generate content based on user input. An attacker injects malicious code into the input field, which is then executed by the JavaScript code, allowing the attacker to execute arbitrary code on the server.
The Risks of DOM-Based Vulnerabilities:
DOM-based vulnerabilities can have severe consequences, including:
Cross-Site Scripting (XSS): An attacker can inject malicious code into the website, allowing them to steal sensitive data, perform unauthorized actions, or take control of the user's session. Data Theft: An attacker can use DOM-based vulnerabilities to steal sensitive data, such as login credentials, credit card numbers, or personal identifiable information. Unauthorized Actions: An attacker can use DOM-based vulnerabilities to perform unauthorized actions, such as making purchases, transferring funds, or modifying sensitive data.
Key Takeaways:
To protect your website from DOM-based vulnerabilities, it's essential to follow best practices for secure JavaScript development, including:
Validating and Sanitizing User Input: Ensure that all user input is properly validated and sanitized to prevent malicious code from being injected into your website. Using Secure JavaScript Libraries: Use reputable and secure JavaScript libraries to handle user input and dynamic content generation. Implementing Content Security Policy (CSP): Implement a CSP to define which sources of content are allowed to be executed within a web page, reducing the risk of XSS attacks.
By understanding the risks of DOM-based vulnerabilities and following best practices for secure JavaScript development, you can protect your website and users from these types of attacks. Remember, a secure website is not just about protecting your users' data, but also about maintaining their trust and loyalty.