Bug bounty hunting always sounds thrilling at first. But let's be real: most of your time isn't spent hacking. It's the prep work that eats up your hours. Recon. Mapping. Organizing. Doing the same steps over and over.
I got sick of bouncing between a dozen tools and losing my flow every time I needed to switch gears. So I finally built the tool I always wanted.
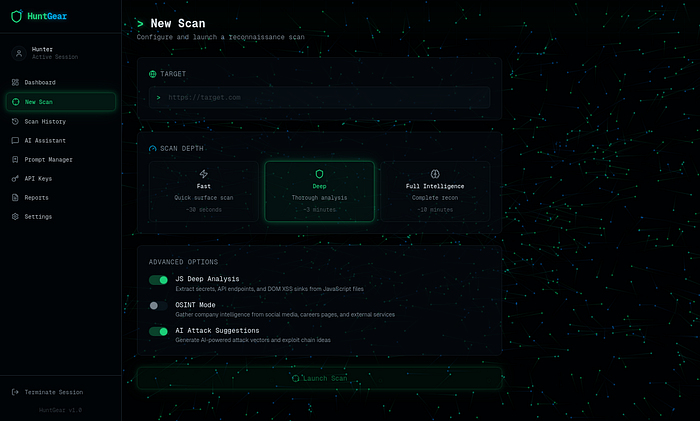
It's not just another scanner. It's a Recon and Attack Vector Online Tool, built from the ground up for bug bounty hunters.
This thing isn't about spitting out endless results. It's about helping you think.
Why I Built This
HuntGear Tool Temporary Access Link :https://vm-rm92wbcnj9bomplw2uau4s.vusercontent.net/
Default Login Credential : admin : admin
Every serious hunter runs into the same headaches.
Recon is all over the place. Subdomains here, endpoints over there, notes scattered everywhere. There's no easy way to connect the dots.
Attack ideas? They slip through the cracks. You spot patterns during a hunt, but later — gone. No memory bank for your own discoveries.
Most tools don't help you think. They just shovel data at you. They don't help you dig deeper or really understand the attack surface.
And honestly, most platforms aren't made for us, the hunters. They're built for big companies or compliance teams. Not for creative attackers.
The Vision: A Hunter's Intelligence Platform
Instead of making yet another scanner, I started with one question:
What if recon tools actually thought like a bug bounty hunter?
That idea turned into this: a Recon and Attack Vector Intelligence platform.
It maps out attack surfaces in depth, suggests attack paths, remembers what you've learned, and actually grows alongside your hunts.
Core Features
Deep Recon Intelligence
This tool goes beyond scanning. It's about understanding your target.
You get multi-domain analysis, subdomain clustering, stack fingerprinting, and ways to uncover hidden surfaces. It's not just about grabbing data — it's about building real context.
Attack Vector Mapping
Forget endless lists of endpoints. The tool organizes everything into clear attack maps.
It spots entry points, trust boundaries, privilege jumps, and lays out possible attack routes. So you're not left wondering, "Where do I even start?"
AI Reasoning Layer
Here's where things get interesting.
The tool picks up on behavioral oddities, permission screw-ups, and weird structural gaps. It's like having a junior pentester working with you, one that never sleeps.
It's not here to replace you. It's here to back you up.
Mathematical Anomaly Detection
False positives are a pain, so I built in statistical analysis.
The system hunts for weird deviations, odd graph patterns, and behaviors that just don't fit. Subtle issues pop up that people usually miss.
Memory That Learns
One of the toughest parts of bug bounty? Forgetting stuff.
You find something cool in one hunt, then later it's like it never happened.
So I added a memory layer. It remembers your old finds, spots when something looks familiar, and nudges you at the right moment.
Now, your past experience actually powers your future hunts.
Probabilistic Confidence Scoring
No more basic severity labels. The tool uses confidence-based scoring.
It checks findings against history, looks at similarity signals, weighs anomaly strength, and helps you focus on what matters instead of chasing ghosts.
Hunter Workspaces
Bug bounty gets messy, fast. Staying organized is half the battle.
The tool gives you dedicated workspaces for each target, keeps scan history, stores notes, and even saves files or payloads. You can always find what you need, when you need it.
Advanced Hunt Notes System
This isn't just a notebook.
It's a real knowledge hub where you can stash payloads, ideas, wild theories, and research links. Everything connects back to your targets and findings.
Over time, it turns into your own offensive research library.
Autonomous Exploration Mode
One feature I'm excited about? Autonomous exploration.
The tool takes its time, explores targets smartly, follows attack paths, connects anomalies, and even suggests new ideas as it goes. It's not about replacing manual testing — it's about amplifying what you can do.
It's a force multiplier, not your replacement.
Can It Discover New Bug Classes?
That's the big dream.
By mixing anomaly detection, memory, and reasoning, the platform highlights weird behavior that doesn't fit any known bug pattern.
That's where real breakthroughs tend to start.
What I Learned While Building This
Bug bounty is intelligence work. It's never just about throwing payloads and hoping for the best. The best hunters build mental models of how systems work (and fail).
Memory is your secret weapon. Top hunters don't just test — they recognize patterns. Turning memory into software changes the whole game.
Tools should make you smarter, not just faster. Good automation cuts out the noise and surfaces what matters, but never takes away your creativity.
The future? It's hybrid hunting. People plus smart tools — never one against the other. That's where the next big wins will come from.

