Before I start, just note that the full techinacal report containing all IOCs, redirect chain analysis and detection rules is available here.
It started on September 2, 2025.
A message dropped into a WhatsApp group I was in — 600+ members, it was a group where we keep ourselves updated with commercial buses and when its time for vacation. The message advertised recruitment for the Ghana Ports and Harbours Authority which official-looking, urgent and had a link to apply.
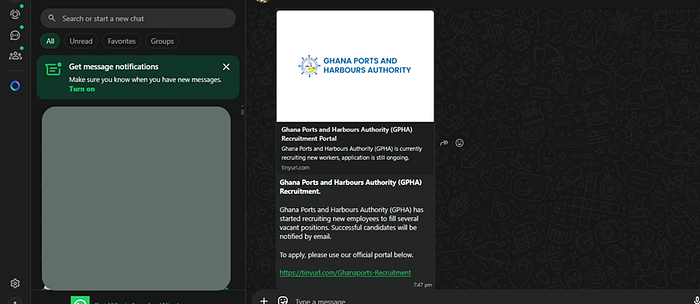
I just knew what was up as soon as I saw that the link was that of github pages. I flagged it in the group and the person who posted it deleted it almost immediately.
That should have been the end of it as many people would ignore what the attacker infrastructure looked like. Instead, it was the beginning of an eight-month investigation into one of the most quietly effective phishing operations I have ever encountered — one that has been running, in various forms, since 2016, and was still posting new content with 2026 branding when I finished writing this.
Why It Works
Before I get into the technical mechanics, let me explain why this campaign is so effective..
It's just because the engineering is primarily social, not technical.
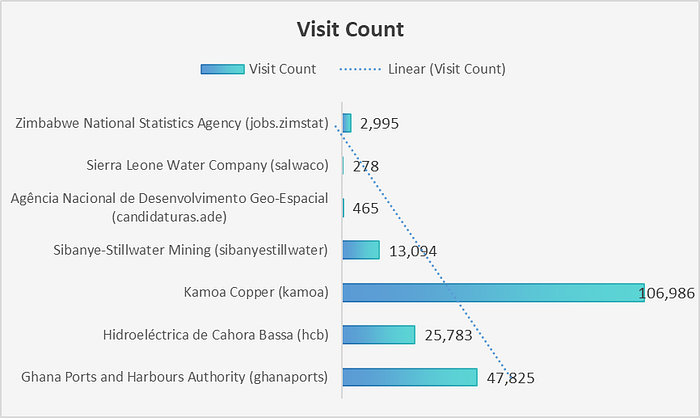
The targets are people who genuinely need jobs. The campaign impersonates employers they would be thrilled to hear from: Ghana Ports and Harbours Authority, Kamoa Copper in DR Congo, IAMGOLD's Essakane gold mine in Burkina Faso, Eskom in South Africa, ZESCO in Zambia, AngloGold Ashanti, Rio Tinto, Petrobras, Sonatrach, Safaricom, Kenya Ports Authority, Sierra Leone Water Company, Zimbabwe National Statistics Agency, UNICEF, The Ghana National Petroleum Corporation and more.
And not just jobs but also free mobile data from MTN, Airtel, and Orange. Government grants, scholarships, exam answers and even Anniversary giveaways. (It was funny seeing one which said Davido was giving away money for his birthday)
The content is localised.. I mean English for Ghana and South Africa, French for Burkina Faso and DR Congo, etc. The logos are real — scraped from official websites. (my view on it was like seeing a carbon copy of a site)
And the link gets to you through WhatsApp — from someone you know. Unlike email phishing, a WhatsApp link from a contact in your community carries implicit endorsement. The person who sent it to you trusted it enough to share. So you click.
The Page
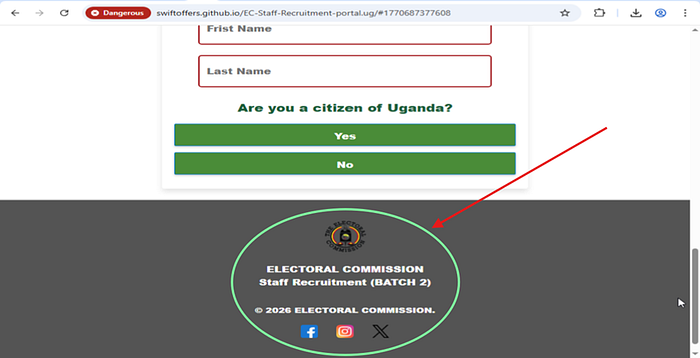
It looks like an official recruitment portal. A popup asks you to confirm the organisation's name — it's pre-filled and auto-accepts when you click OK, creating the psychological impression of a secured, authenticated system.

Then comes the form. Full name. Phone number. Email address. Date of birth. Region. Gender. It feels like a real application.
A fake processing animation plays. Then a congratulations screen.
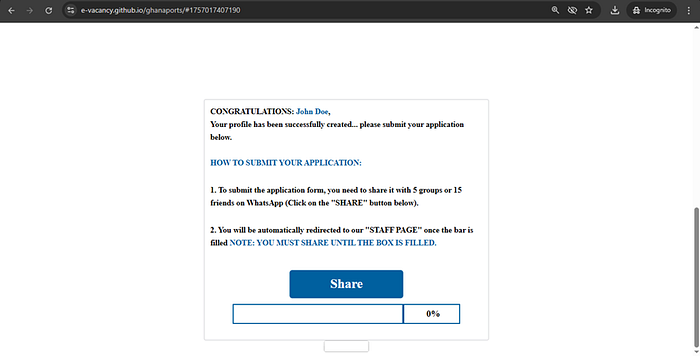
But here's the condition before you can "submit your application": you must share this link with five WhatsApp groups or fifteen contacts. A progress bar appears and fills as you share. It deliberately slows after 80% to extract as many shares as possible. The actual JavaScript controlling it has a developer comment that reads, word for word: // Fakes progress.
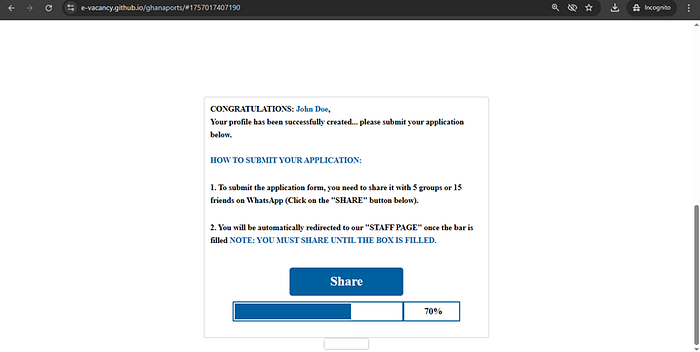
Every person you share to trusts you. So they click. And they share. The campaign distributes itself entirely through the social trust of its own victims, at zero cost to the operator.
On the page, fake comment sections display "beneficiaries" singing the praises of the scheme. The profile photos used for these fake commenters had filenames beginning with "FB" — indicating they were pulled from Facebook to simulate real, identifiable people celebrating their success. This is manufactured social proof, designed to override the hesitation of anyone who is starting to have doubts.
Meanwhile, something else entirely is happening in the background that the victim cannot see. It becomes technically interesting..
The Invisible Layer
Embedded invisibly in every lure page is a visitor analytics widget from a service called SuperCounters. On the surface, it's a free visitor counter. Underneath, it is a pre-screening mechanism.
When the page loads, before you have done anything, a JavaScript function executes and transmits your browser fingerprint to SuperCounters' backend: your user agent (browser, operating system, device type), your screen resolution, the URL you came from, the current page URL.
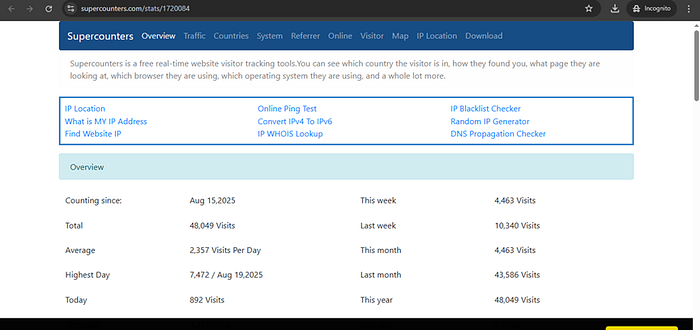
Security researchers at Sucuri documented back in 2019 that SuperCounters' fc.php endpoint conditionally injects additional redirect payloads for visitors who meet specific criteria. In this campaign, that mechanism is used as a filter: mobile users arriving from WhatsApp in target geographies get the redirect payload delivered. Desktop users, VPN users, and security researchers get a harmless visitor count response and nothing more. That is why this campaign evaded detection for so long.
If you pressed the back button at any point, a JavaScript function created an infinite loop — pushing new entries into your browser history so that every back-press sent you forward into the redirect chain instead of backward. There was no way out.
And if you had visited the page before, cookies stored locally on your device from your first visit would skip the entire form. The page would detect you, recognise the cookie, and take you straight to the final redirect page — one click, and you're in the system.
Where the Money Is Made
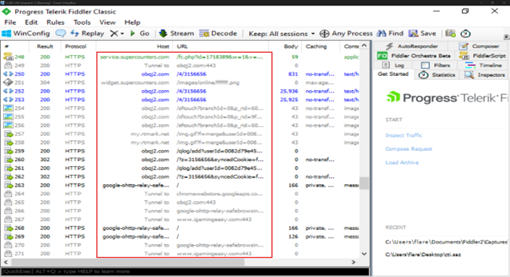
After sharing to others via whatsap, every button on the page — Submit, Print, Download, Report — points to the same destination: obqj2.com.
This is a Traffic Distribution System. The concept originally comes from legitimate digital marketing — a routing server that directs visitors to different landing pages based on who they are. Cybercriminals have built entire criminal enterprises on the same infrastructure. Infoblox Threat Intelligence has documented how malicious TDS networks are among the most resilient cybercrime infrastructure in existence, capable of routing victims to scams, phishing, or malware while showing security researchers something completely benign. Palo Alto Networks' Unit 42 found that malicious TDS chains average significantly more hops and more interconnected domains than legitimate ones deliberately so, to make them harder to trace and block.
When I accessed obqj2.com through Burp Suite and the server served me a decoy. The actual code in that decoy response even includes a parameter named prfrev=false — "previous referrer verified: false." The system said I was not a real victim and acted accordingly, lol.
In a genuine victim's browser, the process works like this: your fingerprint data which is collected during your time on the lure page.. is submitted to the TDS. The system runs a real-time advertising auction in milliseconds. The winning advertiser pays approximately $4.61 per thousand visitors. You are then routed through a chain of intermediary ad networks — igamingeasy.com, wheel-game.xyz, ads.adsbridge.top, tmll7.com, and others before landing on the final destination.
That destination could be an online casino, a binary options trading platform, asports betting site, a cryptocurrency exchange, just to mention a few.
These are legitimate companies with affiliate programmes. They pay commissions for every referred user who registers. They may be entirely unaware that the traffic arriving through their affiliate links came from people who were phished through a fake mining company recruitment portal.
I did not find one TDS. I found several: obqj2.com, tmll7.com, outrotomr.com, whouphesaussums.net, zireemilsoude.net, and more — all routing traffic dynamically based on your geography, device, and engagement score. The routing is geographic: a session appearing to come from Germany lands on a German-language casino. A session from Portugal lands on Betano with a Portuguese campaign code. A session from Ghana gets binary options or an online casino. The system knows where you are and serves you accordingly.
The entire TDS infrastructure runs behind Cloudflare's content delivery network, which hides the real server's location completely. Every attempt to identify the origin IP hits a wall.
The Scale of It
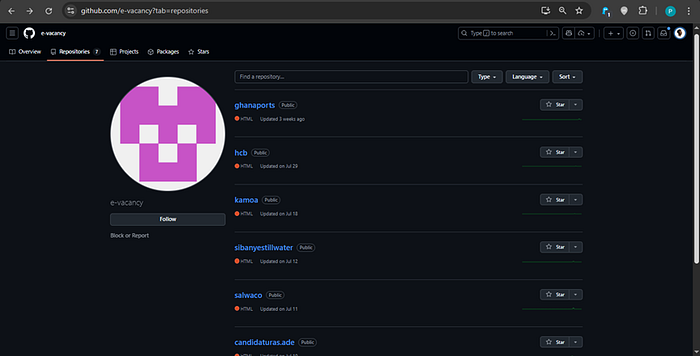
The phishing infrastructure I uncovered spans:
- Seven GitHub Pages sites (all reported and taken down — three separate accounts) targeting institutions across Ghana, Mozambique, DR Congo, South Africa, Sierra Leone, Zimbabwe, and Côte d'Ivoire
- 400+ Blogger-hosted phishing blogs across at least six operator accounts, with content dating back to 2016 and new posts published with 2026 branding as recently as February of this year
- Eleven confirmed target countries including Ghana, Burkina Faso, DR Congo, Mozambique, South Africa, Sierra Leone, Zimbabwe, Uganda, Kenya, Malawi, and Nigeria
Analytics data accessed from the SuperCounters dashboards associated with the GitHub lure pages showed over 152,000 confirmed visits — 43,765 on the Ghana Ports page alone, 76,532 on the Kamoa Copper page, 19,672 on the Mozambique HCB page. More than 95% of those visits came from mobile devices in the target countries. These are real people who clicked, filled in their names and phone numbers, and shared the link to their communities.
Every time I took down a GitHub account, a new one appeared within days. The operators treat platform takedowns as an operational inconvenience, not a campaign-ending disruption.
What I Think Is Actually Happening Here
The personal data collected on the lure pages (names, phone numbers, email addresses, dates of birth) does not appear to be transmitted to a remote server in the visible code. That observation initially made me wonder if this was reconnaissance for something more targeted down the line.
When I uncovered the TDS and the full monetization chain, the primary motive became clear: money. Every qualifying victim session is auctioned and sold. It is, in a very deliberate sense, a business.
But the data collection infrastructure is already built. One backend change and every field submitted by every victim is harvested. Given that hundreds of thousands of people have already submitted genuine personal information, the risk of this pivoting into credential harvesting, or targeted follow-on phishing campaigns is not hypothetical but is a ready capability waiting to be activated.
These blogs have been active since 2016. New ones are being created today. The people being targeted are job seekers, students, parents — people hoping for something better, exploited at the intersection of economic pressure and digital trust. Like, you get the pain?
If a job opportunity arrives via WhatsApp, verify it directly through the official organisation's website. No legitimate employer requires you to share a link with fifteen people before you can submit your application.
Once again, all that you've read here is thery. The full technical report including all indicators of compromise, redirect chain analysis, detection rules and the complete Blogger blog IOC list is available via this link.
Peace.