[ACTION REQUEST] You have been red flagged for violating our terms

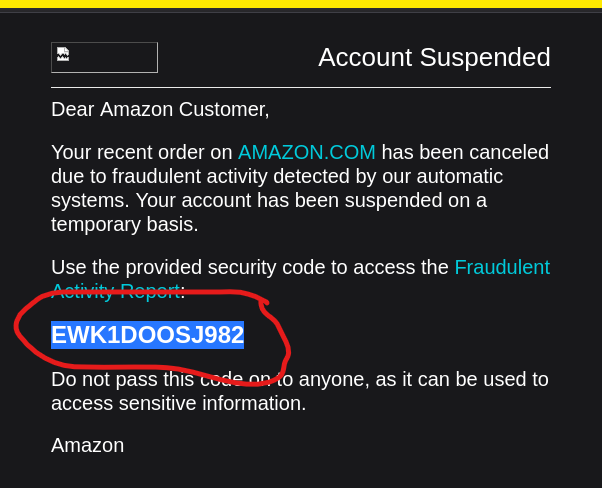
Upon opening the email, it was observed that the attacker attempted to impersonate a trusted brand, presenting the following email identity to the user:
amz@fareast.com.sg

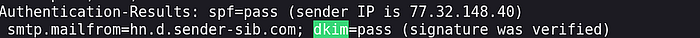
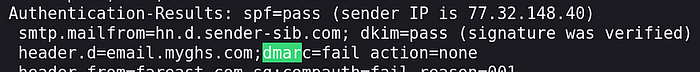
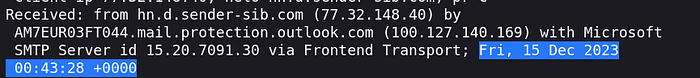
During email path analysis, the true origin of the message was identified as the following IP address:
77.32.148.40

While tracing the message transmission, it was found that attackers relied on third-party infrastructure. The domain used during the SMTP handshake (HELO/EHLO) was:
hn.d.sender-sib.com

Based on infrastructure indicators, the attack was determined to originate from:
France
Although the email appeared legitimate, authentication checks showed the following results:
- SPF: pass
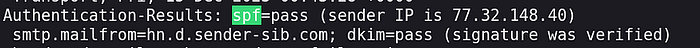
DKIM: pass
DMARC: fail
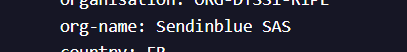
Threat intelligence analysis revealed that the network typically associated with this infrastructure is:
FR-MAILINBLUE-20061213

While tracing bounce handling, the return domain that revealed the actual sending infrastructure was:
hn.d.sender-sib.com
Further ASN/IP intelligence confirmed that the organization associated with this infrastructure is:
Sendinblue SAS
For timeline reconstruction, the original arrival timestamp of the email was extracted as:
2023/12/15 12:43:28
During content analysis, it was discovered that attackers used a tracking/redirection layer instead of a direct malicious domain. The main domain used for this purpose was:
chdgiei.r.bh.d.sendibt3.com

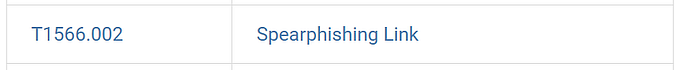
According to MITRE ATT&CK, the phishing sub-technique used in this attack is:
Spearphishing Link
The impersonated organization in this campaign was identified as:
Amazon
To simulate legitimacy and urgency within the email body, the attacker used the following code:
EWK1DOOSJ982
MITRE ATT&CK analysis also identified the related software as:
Pony
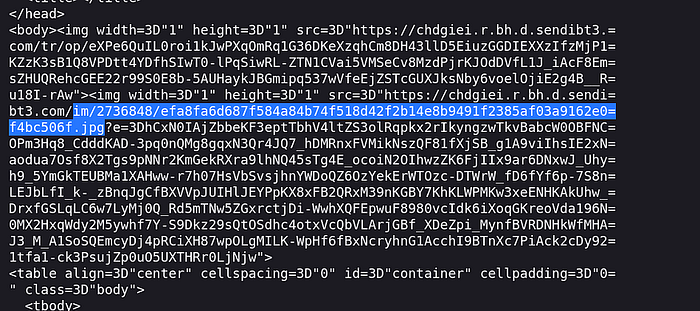
Further investigation revealed a hidden image used to track user interaction with the email. The image path was:
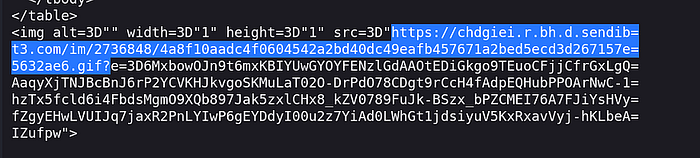
Additionally, a hidden GIF used for tracking user interaction was found at:
The attack was mapped to MITRE ATT&CK technique:
T1566
Finally, the recommended mitigation strategy focusing on increasing user awareness is:
M1017