Short Story
How a forgotten endpoint quietly introduced client-side injection risk.
The original domain, abc.com, presented a simple login page.
- Clean interface.
- No visible parameters.
- No reflected input.
- No obvious injection points.
There were no query strings to tamper with.
- No dynamic user-controlled inputs.
- No client-side reflections relevant to XSS testing
Instead of stopping at the login interface, I expanded the scope and began mapping the domain structure. But security assessments shouldn't stop at what's visible. While mapping the domain structure, I discovered something that wasn't linked from the main interface:
/doc/index.php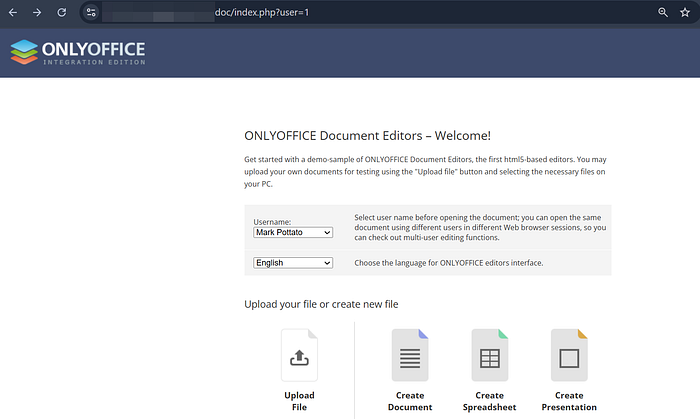
Completely unlinked and outside the authentication flow, this endpoint existed under the same primary domain, silently expanding the attack surface.
Expanding the Surface
The endpoint included a parameter:
/doc/index.php?user=1Numeric parameters always deserve attention.
So instead of treating it like a static demo page, I tested it as part of the application.
What I found wasn't just reflection.
It was unsanitized input handling inside a component running on the same primary domain as the authenticated portal.
And that changed the impact entirely.


Scenario
If a user is already authenticated on:
https://abc.comand is sent a crafted link such as:
https://abc.com/doc/index.php?user=<xss>the injected script executes within the user's active session context because it resides on the same primary domain.
This means the payload runs with the same origin trust as the main portal, potentially allowing:
- Execution of authenticated actions on behalf of the user
- Show fake prompts inside the real domain
- Potentially access session cookies if they are not properly protected
The risk isn't just input reflection — it's shared trust under the same origin.
When hidden components inherit the authentication boundary of a production domain, even small injection flaws can have meaningful impact.
Lessons Learned
· Attack surface is larger than the visible UI. If it runs under the domain, it matters.
· Recon beats randomness. Mapping directories revealed more than attacking the login page ever would.

