Previously in Season 1: We finished building the "Engine Room," breaking down the Blockchain, Solidity, and the EVM. Now that we know how the machine works, it's time to start breaking it. Welcome to Phase 2: Translating Web2 Hacks to Web3.
In Web2 security, there is a classic rookie mistake every beginner bug bounty hunter looks for: the hardcoded frontend secret.
You right-click a webpage, hit Inspect Element, poke around the JavaScript source code, and boom, you find an admin password or an API key sitting right there in plain sight. It's the easiest dopamine hit in the VAPT world.
Web2 developers eventually learn to hide those secrets in a secure backend database where the client can't reach them. But when those same developers transition to Web3, they bring a massive, dangerous misunderstanding with them.
They think the private keyword in Solidity acts like a secure backend database. It doesn't.
If you want to hunt logic flaws in smart contracts, here is why you need to stop trusting the private keyword, and how you can "Inspect Element" the entire blockchain.

1. The private Keyword Trap
In traditional object-oriented programming (like Java or C++), setting a variable to private means it cannot be accessed by the outside world. It is securely locked inside the application's memory.
In Solidity, the private keyword does something completely different. It only restricts other smart contracts from calling and reading that variable natively.
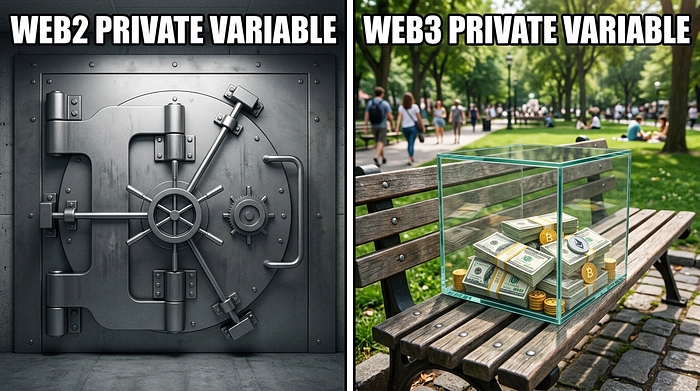
But remember what we learned in Episode 2 about the blockchain being a public crime scene? Every single node on the network has a copy of the contract's data. There is no "backend server" hiding the data from the public. If a developer stores a sensitive password, a price-feed mechanism, or a VIP whitelist as a private variable, they haven't encrypted it. They have simply put it in a glass box and asked other contracts nicely not to look at it.
2. Prying Open the Storage Slots
So, how does a Web3 hacker actually break open the glass box? They bypass the contract entirely and read the raw memory of the blockchain itself.
When a smart contract is deployed, the Ethereum Virtual Machine (EVM) stores all of its state variables in massive data structures called Storage Slots. Each slot holds exactly 32 bytes of data.

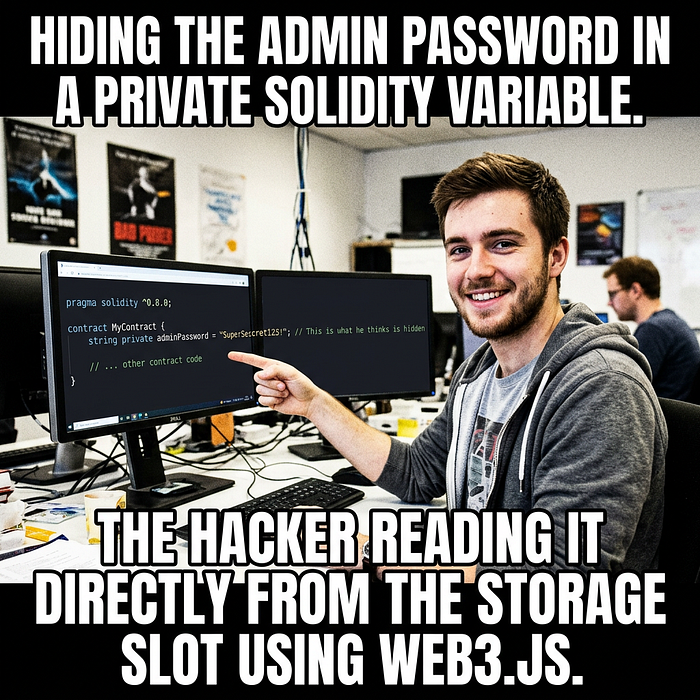
If a Web3 hacker knows the address of the smart contract, they don't need the contract's permission to read its data. They can simply fire up their terminal, connect to an Ethereum node, and use a built-in function like web3.eth.getStorageAt().
By querying the exact storage slot where the private variable is kept, the blockchain will spit out the raw, unencrypted hex data.
3. The Real-World Heist
This isn't just a theoretical vulnerability.
Imagine a decentralized casino contract that uses a private variable as a "random seed" to determine the winner of a lottery. The developers think it's secure because no other contract can read the seed to predict the winner.
A hacker doesn't care. They use getStorageAt(), read the private seed directly from the block's storage slots, calculate the winning number locally on their own machine, and then buy the exact winning ticket. The casino is drained, and the developers are left wondering how their "secure" backend was breached.
The Takeaway: In Web3, transparency is absolute. Nothing on the blockchain is truly hidden unless it is heavily encrypted before it gets uploaded. If you see a private variable holding sensitive logic in a smart contract audit, you haven't just found a bug. You've found the keys to the vault.
Next time on Season 1: We are going to look at what happens when a developer forgets to lock the front door entirely. Get ready for Chapter 6: The Web3 IDOR.
Let's Connect
I'm Tabrez, a CS student diving deep into the intersections of IoT, Cybersecurity, and Web3. If you want to see more of my work or just chat about logic flaws, find me here:
🌐 My Website | 💻 LinkedIn
Shout-outs & Tools: This article was a passion project built on plenty of late-night research and a few too many cups of coffee.
- Creative Partner: I teamed up with Gemini to help bridge my brain-dumps into this final structure.
- Visuals: Huge thanks to my bestie GenSpark AI for taking my chaotic prompts and turning them into these banger 3D visuals and meme layouts.
