By ThreatWatch360 Security Research Team
📅 Dec 2025 — Mar 2026
Executive Summary
Cyber criminals are no longer relying on crude phishing emails alone. Modern campaigns are highly targeted, visually convincing, and strategically timed, often exploiting trusted brands, financial urgency, and user behavior.
This research is part of our early warning and anti-phishing capabilities, where we actively hunt threats that often remain undetected in their early stages.
This report analyzes threat intelligence from Dec 2025 — Mar 2026, highlighting a sharp rise in phishing and scam campaigns. Thousands of malicious domains are created daily, with many remaining undetected during their most active phases (including gaps in detection by VirusTotal).
The blog emphasizes that reactive security fails, as threats are detected post-attack. Instead, proactive threat intelligence using early indicators, enables faster detection, prevention, and takedown.
Scammer's Pattern
Attackers use a scalable and repeatable model for phishing and brand impersonation. They start by registering low-cost lookalike domains, then clone legitimate websites (design, content, login pages) using automation tools.
These malicious sites are promoted via social media, ads, search engines, WhatsApp, Telegram, email, and SMS, often creating urgency to lure users. During early stages, many domains remain undetected by traditional systems.
Once users interact, attackers steal credentials, personal, and financial data, which is quickly monetized through fraud or resale. To sustain operations, they rotate domains, reuse infrastructure, and replicate templates, enabling rapid scaling while avoiding detection.
Below are real-world case studies that highlight how these attacks unfold — and the impact they create.
FBI Impersonation: Fraud Recovery Scam Using Trust in Law Enforcement

The domain digitalreclaim.com was registered on 29 October 2024 and later updated on 28 September 2025. Despite being active for over a year, it was only detected on 17 December 2025 and taken down on 21 December 2025. During its most active phase, it remained completely undetected.
Attackers impersonated the FBI by replicating official branding and communication style to appear legitimate. The campaign targeted victims of prior scams, offering fake legal assistance and fraud recovery services. By exploiting urgency and authority, the attackers convinced users to share sensitive personal and financial information.
Victims were exposed to further financial fraud under the pretext of recovering lost funds. Sensitive data collected could also be reused for identity theft and future attacks. The long detection delay significantly increased the number of potential victims and highlights a serious gap in early threat detection, along with the risk of eroding trust in government institutions.
Exploitation of Financial Aid Themes in World Bank IDA Impersonation
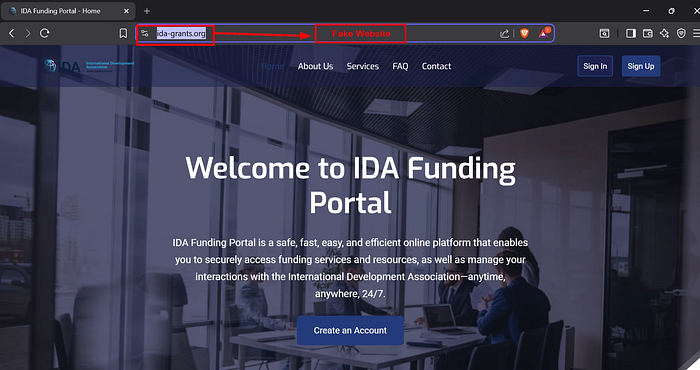
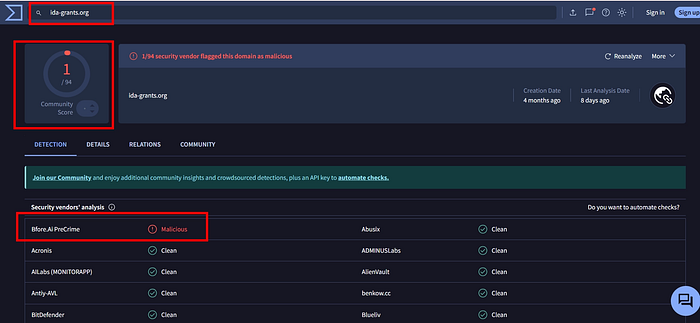
The fake domain was registered in late November 2025, detected nearly a month later on 25 December, and taken down within 48 hours. During its active phase, it remained undetected by most security engines.
Attackers created a lookalike website mimicking the World Bank's International Development Association (IDA). By promoting fake grant opportunities, they targeted individuals actively seeking financial aid. The operation combined advance-fee fraud with data harvesting, leveraging trust in a globally recognized institution.
Victims were tricked into paying fake processing fees while also exposing sensitive personal and financial data. The biggest concern here was the complete lack of early detection, allowing the campaign to operate unnoticed during its most effective phase.
Investment Scam in Indian Markets: Upstox Platform Impersonation
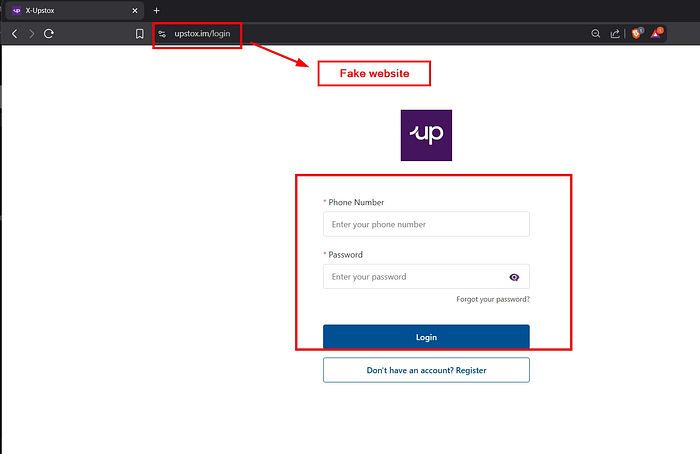
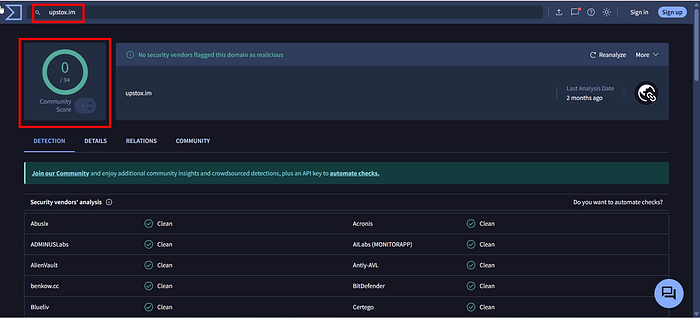
The fraudulent domain upstox.im was identified on 15 August 2025 and taken down by 20 August 2025. However, during its initial phase, the campaign remained undetected, allowing attackers to operate without resistance.
Attackers impersonated the Upstox trading platform by creating a high-fidelity clone of its login interface. Targeting Indian retail investors, they guided users to "activate" their accounts by depositing funds to start investing. Once funds were added, victims were shown fake dashboards with simulated profits to build confidence. However, when users attempted to withdraw or cash out, transactions were blocked or ignored — effectively trapping their funds within the fraudulent platform.
Victims suffered direct financial losses as deposited funds could never be recovered. In addition, compromised credentials and intercepted OTPs enabled potential account takeovers across other services. This case highlights how investment scams in the Indian market are evolving into closed-loop fraud systems, where users are lured in, shown fake gains, and ultimately prevented from exiting.
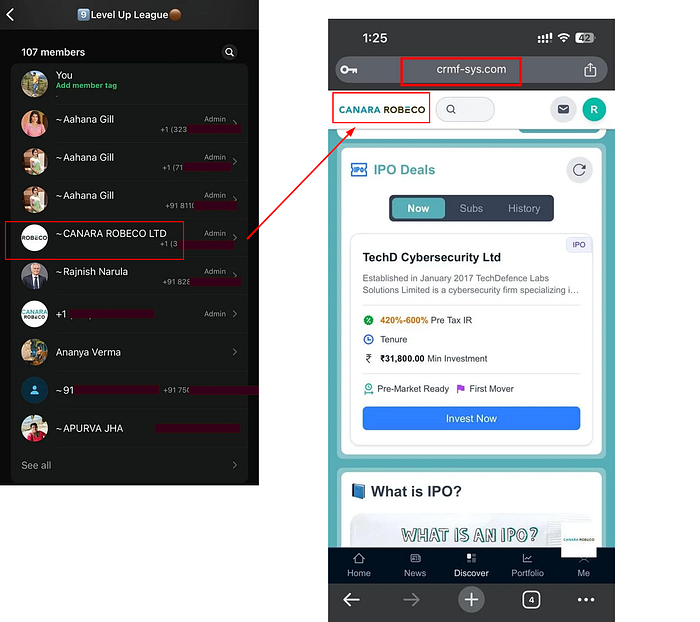
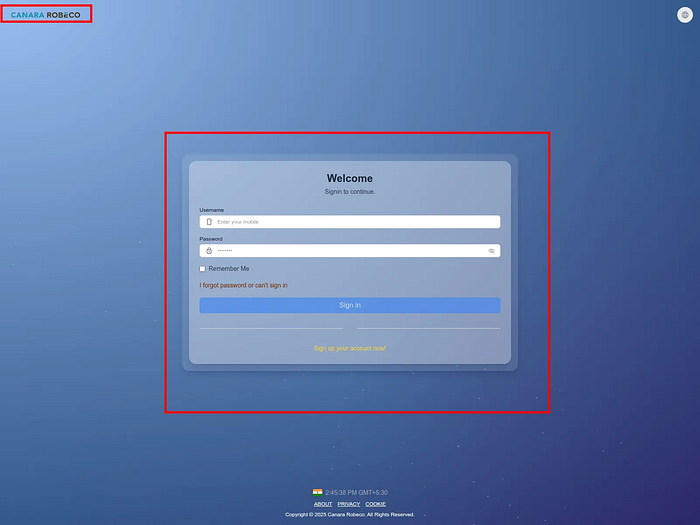
Attackers ran a coordinated IPO investment scam by impersonating a legitimate mutual fund brand and promoting exclusive "IPO tips" for TechD Cybersecurity Ltd. The campaign leveraged WhatsApp and Telegram groups to build credibility and attract retail investors.
The malicious domain was identified and taken down within 2 hours of detection, significantly limiting its operational window. Unlike typical campaigns that remain active for days or weeks, this was neutralized at a very early stage by our team.
Users were guided to a fake investment portal where they were encouraged to deposit funds to participate in the IPO opportunity. Similar to other modern investment scams, the platform displayed fake allocations and profit projections to build trust. However, once users deposited funds, withdrawals were either blocked or completely disabled — effectively trapping victims in a closed-loop system.
Although this type of scam has already trapped a large number of users across similar campaigns, early detection in this case helped prevent widespread financial losses. The quick takedown disrupted attacker operations before significant scale could be achieved.
This case reinforces a growing trend in the Indian market — IPO-themed scams combined with social media-driven hype, where users are lured with "exclusive access" and ultimately lose funds with no possibility of withdrawal.
Seasonal E-Commerce Fraud Leveraging Flipkart Brand Abuse
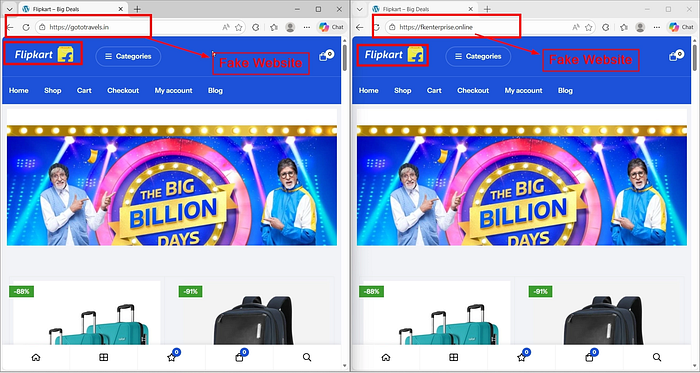
Attackers impersonated Flipkart, one of India's largest e-commerce platforms, by creating fake shopping websites offering heavy discounts and limited-time deals. These platforms were designed to closely resemble legitimate storefronts, making them appear trustworthy.
Users were encouraged to place orders and complete payments through these fake portals. However, once a purchase was made, the product was never delivered, and no support or refund mechanism existed. These campaigns are not isolated — similar fake websites are continuously launched targeting multiple e-commerce brands.
Victims suffered direct financial losses with no product delivery or refund options. In many cases, attackers also captured user details such as phone numbers, addresses, and payment information. The scale of these scams is significant due to their daily occurrence and repeatable nature, making them a persistent threat across the entire e-commerce ecosystem.
Brand Power Abuse: Tesla-Themed Investment Scam Case Study
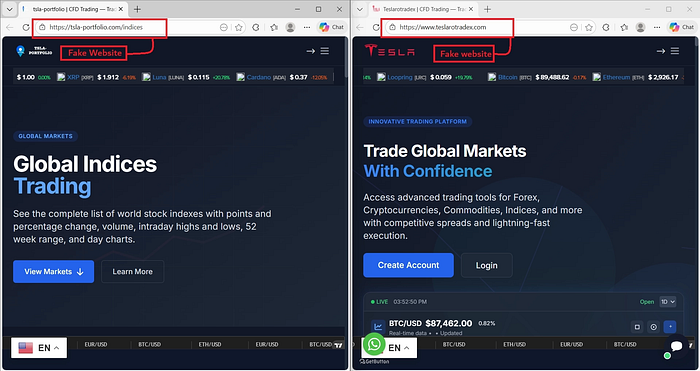
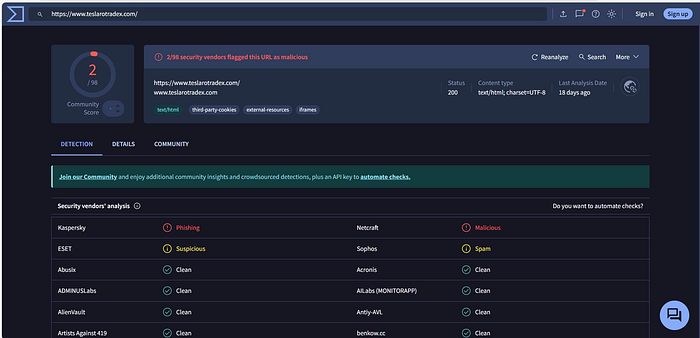
The fraudulent domains were reported on 25 December 2025 and taken down by 28 December 2025. While some security vendors eventually flagged the activity, the campaign remained undetected during its early and most effective phase.
Attackers impersonated Tesla to promote fake investment opportunities through domains like teslarotradex.com and tslaportfolio.com. Using professionally designed dashboards, fake performance metrics, and brand association, they created a strong illusion of legitimacy.
Victims were encouraged to deposit funds with promises of high returns. Similar to other investment scams, once funds were added, users were unable to withdraw their money, effectively trapping them within the platform.
Victims faced direct financial losses along with exposure of sensitive personal and financial data. This case reflects a much larger issue — thousands of similar fraudulent websites emerge daily in the crypto and online investment space, leveraging well-known brands to gain instant credibility.
The scale and speed at which these platforms appear make detection and takedown increasingly challenging, reinforcing the need for proactive threat intelligence and early intervention.
Targeting the Vulnerable: LoanGuru Impersonation Scam
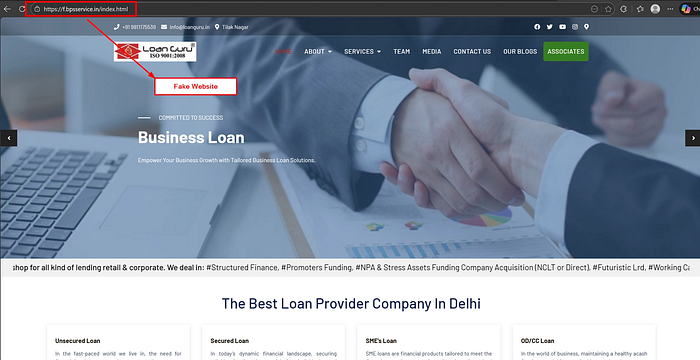
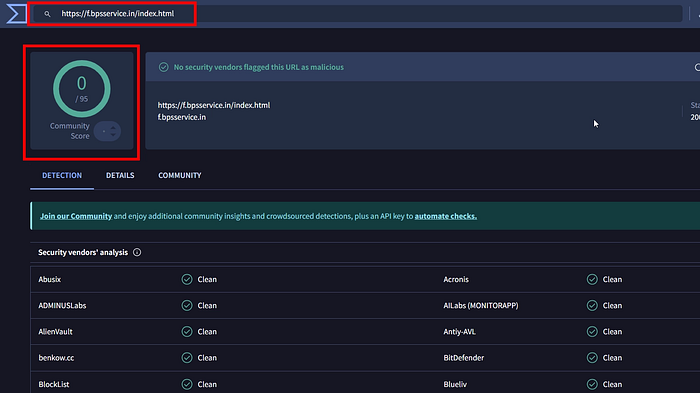
The fraudulent domain f.bpsservice.in was registered on 14 November 2024 and reported on 03 January 2026, indicating a prolonged undetected operational window that allowed attackers to scale their activity.
Attackers impersonated a loan service platform and targeted individuals actively searching for loans. Once users submitted their details through the loan inquiry form, the fraudsters initiated direct contact via phone calls.
Posing as loan agents, they built trust and urgency, convincing victims that their loan was approved and required immediate processing. Victims were then pressured into paying "loan processing fees" or other charges to proceed further.
Victims suffered financial losses through upfront fee payments without receiving any actual loan. Additionally, sensitive personal data submitted in the inquiry form increased the risk of identity theft and future fraud.
This case highlights a highly effective tactic — combining phishing with real-time human interaction, making the scam more convincing and harder for victims to detect.
Malware Distribution via Zoom Meeting Invite Impersonation

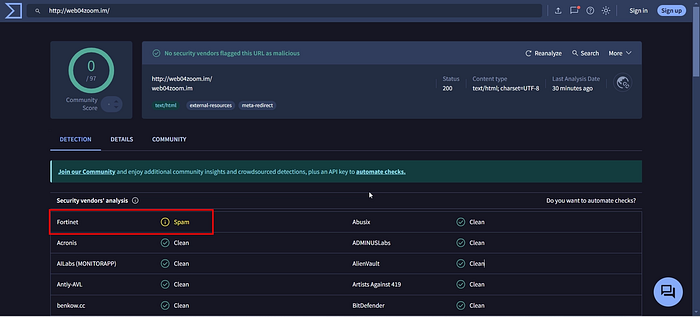
A malware campaign impersonating Zoom was identified through domains like web04zoom.im, teaminvitemeeting.im, and zoomteammeeting.im. Detected on 13 January 2025 and taken down by 19 January 2025, the attack spread malware disguised as meeting links or Zoom downloads.
Attackers impersonated Zoom by sending fake meeting invites disguised as job interview calls or business inquiries. Targets received links or attachments claiming to be meeting details or required software.
Instead of leading to legitimate meetings, these links delivered malware disguised as Zoom installers or meeting files. Once executed, the malware infected the victim's system, granting attackers unauthorized access.
Victims faced system compromise, data theft, and potential long-term persistence on their devices. In some cases, infected systems could be leveraged for further attacks such as botnets or lateral movement.
This campaign highlights a shift from traditional phishing to malware-driven social engineering, where attackers exploit professional opportunities like job offers and business communications to increase success rates.
Unlike typical phishing, this campaign infected systems directly, giving attackers unauthorized access, persistence, and the ability to steal data. Since the domains were not detected early, many users were compromised, and infected systems could also be used in larger attacks like botnets.
Expanding Targets: Phishing Against Regional Banking Users
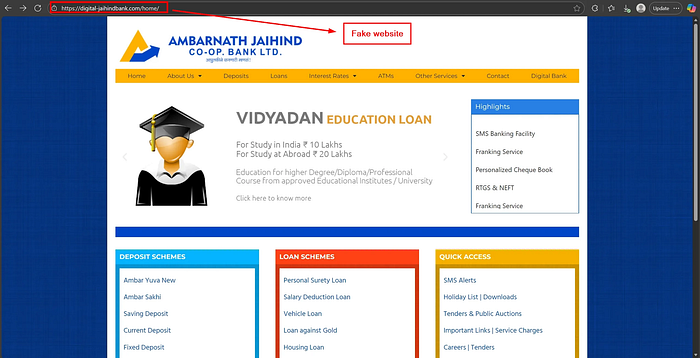
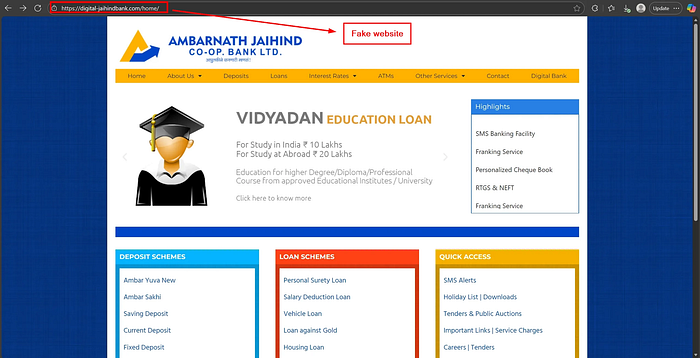
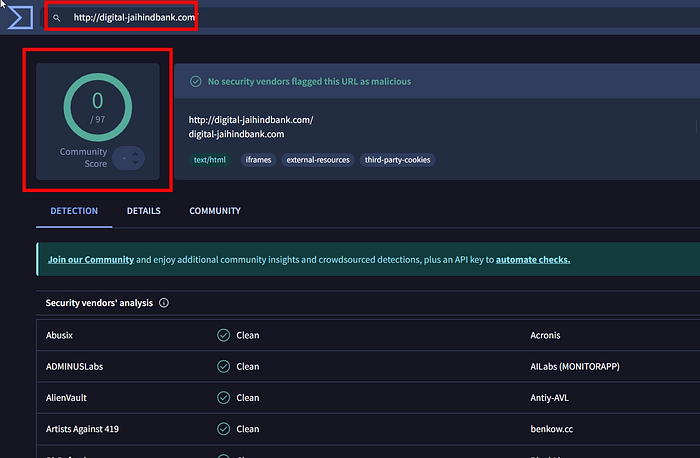
The fraudulent domain digitaljaihindbank.comwas registered on 12 May 2025, detected on 24 November 2025, and taken down by 28 November 2025. The campaign remained active for over six months before detection.
Attackers impersonated a regional bank by replicating its online banking interface and login systems. This campaign highlights a broader shift — scammers are no longer focusing only on large or tier-1 brands, but are increasingly targeting regional and smaller institutions.
These organizations often have strong local trust but comparatively lower visibility in cybersecurity monitoring, making them attractive targets. Users were tricked into entering their banking credentials and authentication details on fake portals.
Victims faced account compromise and direct financial losses, while the targeted institution risked reputational damage and erosion of customer trust.
This case reinforces an important trend — no brand is too small to be targeted, and regional companies are becoming a growing focus area for phishing campaigns due to their high trust and relatively lower defense maturity.
This case highlights a growing trend where attackers are targeting smaller regional banks, exploiting high user trust and lower cybersecurity awareness. With phishing setups costing less than $30, attackers can easily create and scale multiple fake domains.
Due to delayed detection, the campaign led to financial losses, account compromise, and reputational damage, emphasizing the need for stronger early detection and user awareness.
Impact
Brand impersonation, phishing, and malware campaigns are increasing due to the open and low-cost nature of the internet, allowing attackers to easily clone trusted brands and scale attacks quickly.
These attacks mainly impact users through financial loss, identity theft, and account compromise, while sometimes targeting internal teams to disrupt operations or spread misinformation.
The key challenge is not just detection but slow response and coordination gaps, including delayed identification, unclear ownership, and slow takedowns. As a result, even short-lived campaigns can cause significant and cumulative damage.
ThreatWatch360 Response Actions
Our Threat Intelligence team was taking immediate steps:
- Sharing early-warning alerts with brand protection clients
- Escalating the domain to CERT-In and relevant government entities
- Submitting a takedown request to the domain registrar
- Initiating monitoring for related impersonating domains using variant keyword patterns
ThreatWatch360's Brand Protection Suite was continuously helping organizations reduce exposure to such attacks by offering:
- 24/7 Domain Abuse Monitoring for keyword, typo-squatted, and DNS registrations
- Real-Time Phishing Site Detection and Early-Warning Alerts to prevent widespread damage
- Executive and Brand Misuse Monitoring, including impersonation of leadership and institutions
- Automated and Manual Takedown Coordination with registrars and hosting providers
For incident response support, free takedown contact us ThreatWatch360 https://threatwatch360.com/phishing-takedown-service

