Hello, I am Anggarizmi. I am a cybersecurity enthusiast with a strong interest in web exploitation, penetration testing, and bug bounty hunting. This is the first write-up I have ever written, and I decided to start documenting my learning journey so I can track my progress, improve my technical skills, and build a portfolio over time.
Through this platform, I will not only document CTF write-ups, but also share my learning from cybersecurity research, vulnerability analysis, and bug bounty experiences. My goal is to build a habit of writing and documenting technical findings, because I believe that documenting what I learn is one of the best ways to truly understand how security vulnerabilities work and how attackers think.
This write-up was written about a week after Eid al-Fitr. After spending time with family and taking a short break during the holiday, I wanted to get back on track and continue sharpening my cybersecurity skills. I realized that solving challenges alone is not enough, so documenting the process is what really helps me understand the technical details and the mindset behind each attack.
In this write-up, I will explain how I solved the "Old Sessions" web exploitation challenge from picoCTF 2026. I will go through the reconnaissance process, analyze the vulnerability, and explain the exploitation steps that led to obtaining the flag.
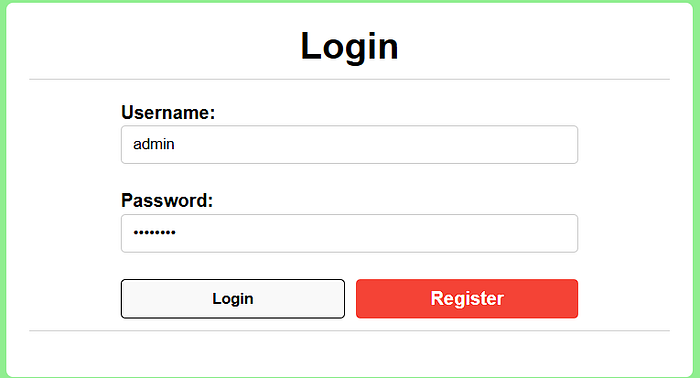
Ok, so let's jump to the link where this challenge has been provided.

Okay, for me, when it comes to web exploitation, I usually start by doing some reconnaissance first, beginning with checking the View Page Source.

In this case, sometimes the developers give a clue from the comments or maybe the script has its own vulnerability. But in this case, there also doesn't seem to be any script that really piques my curiosity, just a script related to a username and password.
Okay, so let's get right to the interesting and fun part on "how I do it". I previously took a cybersecurity training course, and my mentor was a security expert who shared his tips and experiences from his professional career in penetration testing. Here's a shout-out to my mentor: https://www.linkedin.com/in/williams-williams-345344129/
And he said that when you encounter a situation like logging in with a username and password, DO NOT JUMP RIGHT IN OR AUTOMATICALLY THINK OF USING TOOLS. Because that's not how hackers or attackers do it. First, make sure that there's a JavaScript that can be exploited, or what might happen when you enter something, so don't immediately use tools.
And my mentor said that during his penetration tests, when using credentials like admin:admin, admin:admin123, or even admin:password, he could bypass the login session immediately. Sometimes developers overlook trivial details like this, but the consequences can be severe.
So after that, I tried the credentials that usually bypass the ones listed above, and when I tried logging in with the admin:password credentials..
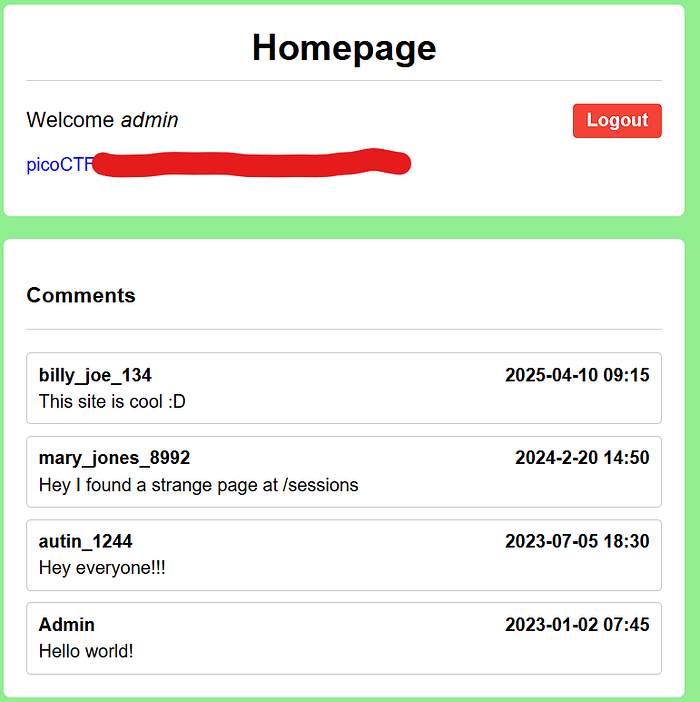
Yes, you'll get the flag.
At first glance, this challenge seemed relatively easy. However, it highlights a very common real-world issue: the use of weak or easily guessable credentials. Many real-world breaches do not happen because of complex zero-day vulnerabilities, but because of simple mistakes such as weak passwords, credential reuse, or exposed login panels. This challenge serves as a reminder that basic security misconfigurations can lead to serious compromises if overlooked.
