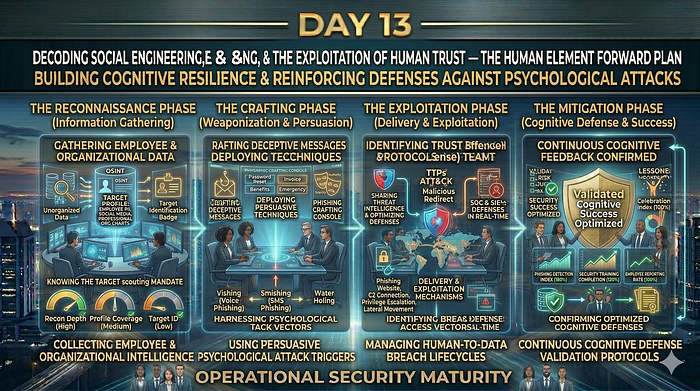
Day 13: Cybersecurity Mastery series
Welcome to Day 13 of our 30-Day Cybersecurity Mastery series. We are continuing our journey through Phase 3: Offensive Security & Vulnerability Exploitation.
Over the first twelve days, we engineered highly resilient, multi-layered digital fortresses. We deployed Next-Generation Firewalls, implemented mathematically rigorous cryptographic protocols, and established Zero Trust Identity architectures.
However, a fundamental axiom of offensive security is this: An attacker will always take the path of least resistance. Why spend weeks writing complex zero-day exploit code to bypass an AES-256 encrypted firewall when you can simply send an email, create a sense of panic, and convince an employee to hand over their password?
Today, we step away from code and examine the exploitation of human psychology. This is the devastating art of Social Engineering.
1. The Core Philosophy of Social Engineering
Definition: Social engineering is the psychological manipulation of individuals into performing actions or divulging confidential information. It is a confidence trick designed to bypass technological security controls by exploiting human nature.
If a firewall evaluates packets based on rules, a human evaluates requests based on emotion. Threat actors engineer their attacks to trigger specific psychological levers that override an employee's critical thinking:
- Authority: Posing as the CEO, the IT Director, or a law enforcement officer. Humans are socially conditioned to comply with leadership without questioning the request.
- Urgency/Fear: "Your account will be permanently deleted in 10 minutes if you do not log in to verify your credentials." Panic forces immediate, thoughtless action.
- Familiarity/Trust: Compromising a vendor's email account and sending a malicious invoice from a trusted, recognized address.
- Curiosity/Greed: Offering a fake corporate bonus or leaving a malicious USB drive labeled "Q4 Layoff List" in the company parking lot.
2. The Typology of Deception: Phishing and Beyond
To defend the enterprise, you must intimately understand the specific delivery mechanisms of social engineering. They are categorized by their medium and their target.
The Email Vectors
- Phishing: The shotgun approach. Sending thousands of generic, malicious emails (e.g., a fake Netflix password reset) hoping a small percentage of recipients click the link.
- Spear Phishing: The sniper approach. A highly targeted attack against a specific individual or department. The attacker conducts reconnaissance (Day 12 Kill Chain) to include specific details, such as mentioning the target's actual manager by name, making the email incredibly convincing.
- Whaling: A subset of Spear Phishing that exclusively targets high-level executives (the "Whales"). CEOs and CFOs hold the most authority and the highest level of system access, making them the most lucrative targets.
The Alternative Mediums
- Vishing (Voice Phishing): The attacker calls the target on the phone, often using caller ID spoofing to make it appear as though the call is coming from the internal IT helpdesk. They verbally guide the user into resetting a password or reading out an MFA token.
- Smishing (SMS Phishing): Sending malicious links via text message. As enterprise work shifts to mobile devices, users are inherently more trusting of text messages and less likely to verify the sender's URL.
Physical Social Engineering
- Baiting: Exploiting human curiosity by leaving a physical media device (like a USB flash drive) infected with malware in a location where an employee will find it and plug it into the corporate network.
- Tailgating (Piggybacking): An attacker without an ID badge closely follows an authorized employee through a secure physical door. They exploit the social awkwardness of confronting a stranger or the polite instinct to "hold the door." (The countermeasure for this is the physical Mantrap, discussed in Phase 1).
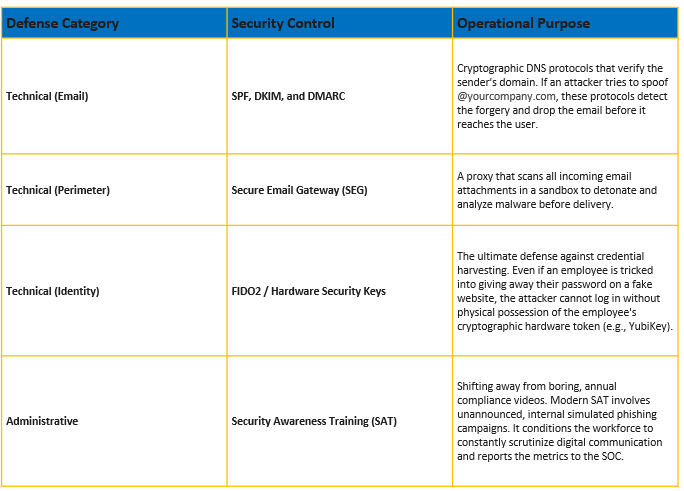
3. Architecting the Defense: Technical vs. Human Controls
You cannot patch human nature, but you can build an architecture that anticipates and mitigates human error. A robust defense requires a fusion of technical safety nets and continuous human conditioning.
The Architect's Summary
Social Engineering represents the largest, most persistent vulnerability in any enterprise. The most sophisticated cryptography in the world is instantly rendered useless if an attacker can simply ask for the decryption key. By understanding the psychological triggers adversaries use — and deploying a combination of strong email authentication (DMARC), phishing-resistant MFA, and rigorous simulated training — you transform your workforce from the weakest link into an active layer of the security perimeter.
Looking Ahead
Today, we covered how attackers trick users into giving up their credentials. But what if the attacker doesn't want to talk to the user at all? What if they want to sit silently on the network and invisibly capture the passwords as they travel across the wire?
Tomorrow, in Day 14, we dive deep into the technical mechanics of the network layer. We will explore Packet Sniffing, Wireshark, and Man-in-the-Middle (MitM) Attacks.