Modern cloud-native applications rely heavily on containers, CI/CD pipelines, and Kubernetes. While this ecosystem enables rapid development and scalable deployments, it also introduces a new class of security risks: software supply chain attacks.
Instead of attacking production systems directly, attackers increasingly target the build and delivery pipeline. If malicious code enters the pipeline, it can propagate across environments and clusters.
This is where Konflux comes in.
Konflux is an open-source platform designed to provide secure software delivery pipelines for Kubernetes-native development, focusing on artifact trust, build integrity, and policy enforcement.
In this article we will explore:
- The Kubernetes software supply chain problem
- Key risks in container-based pipelines
- How Konflux secures the software lifecycle
- A typical secure workflow using Konflux
The Kubernetes Software Supply Chain Problem
A typical Kubernetes application pipeline looks like this:
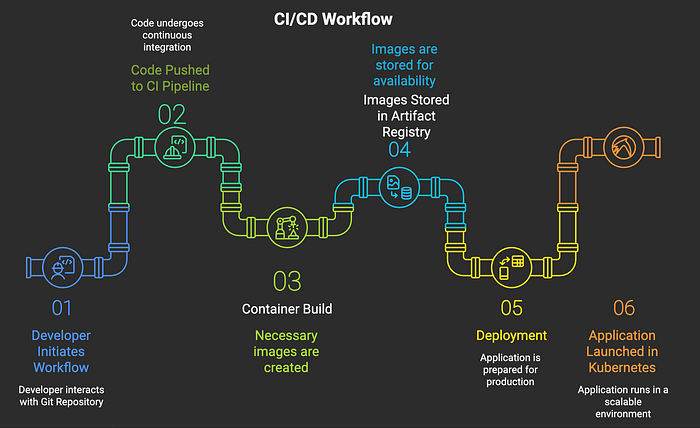
- Each stage introduces potential security risks.
- Modern applications may depend on:
- hundreds of third-party libraries
- container base images
- automated build pipelines
- external registries
- Without proper controls, a compromise at any stage of the pipeline can affect production workloads.
- Recent supply chain incidents have shown that attackers often focus on:
- build pipeline compromise
- dependency poisoning
- artifact tampering
- container registry attacks
This makes software supply chain security a critical concern for Kubernetes platforms.
Common Supply Chain Risks
Compromised Dependencies
Most applications rely on numerous external libraries. If a dependency becomes malicious or compromised, it can introduce vulnerabilities or backdoors into the build.
Untrusted Container Images
Pulling images from public registries without verification can introduce malicious containers into production environments.
Without verification mechanisms, teams cannot guarantee the integrity of container images.
Tampered Build Pipelines
If attackers gain access to CI systems, they can modify build processes and inject malicious artifacts during compilation.
Because build systems often have privileged access, this can affect large numbers of deployments.
Lack of Artifact Provenance
Many organizations cannot answer basic questions about deployed artifacts:
- Which commit produced this container image?
- Which pipeline executed the build?
- What dependencies were included?
Without provenance metadata, it becomes extremely difficult to verify whether an artifact has been modified or compromised.
What is Konflux?
Konflux is a Kubernetes-native platform designed to secure the entire software delivery lifecycle.
Konflux focuses on creating a secure software factory, where artifacts are built, verified, and released using trusted and reproducible pipelines.
The platform integrates directly with Kubernetes workflows and leverages modern cloud-native tools to provide end-to-end supply chain security.
Its goal is to ensure that every artifact deployed into production is:
- built in a trusted environment
- traceable to source code
- verified through automated policies
- free from known vulnerabilities
Core Security Concepts in Konflux
Konflux introduces several mechanisms to secure the software delivery process.
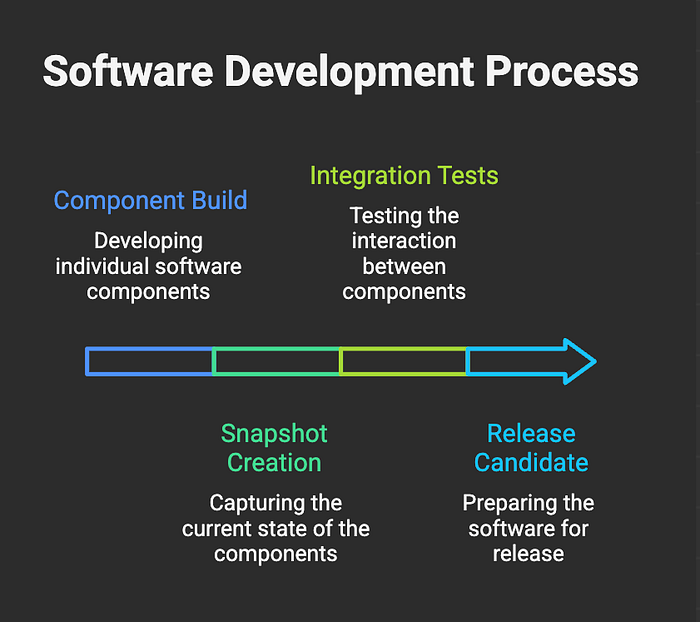
Trusted Build Pipelines
Konflux uses controlled build pipelines executed inside Kubernetes clusters.
These pipelines are implemented using Tekton, which allows pipelines to run as Kubernetes resources.
This approach ensures:
- reproducible build environments
- consistent pipeline execution
- reduced attack surface
Instead of allowing arbitrary builds on developer machines, artifacts are generated through trusted and auditable pipeline runs.
Software Bill of Materials (SBOM)
Konflux automatically generates a Software Bill of Materials (SBOM) during the build process.
An SBOM provides a complete inventory of the components included in a software artifact, including:
- libraries
- dependencies
- system packages
- base container images
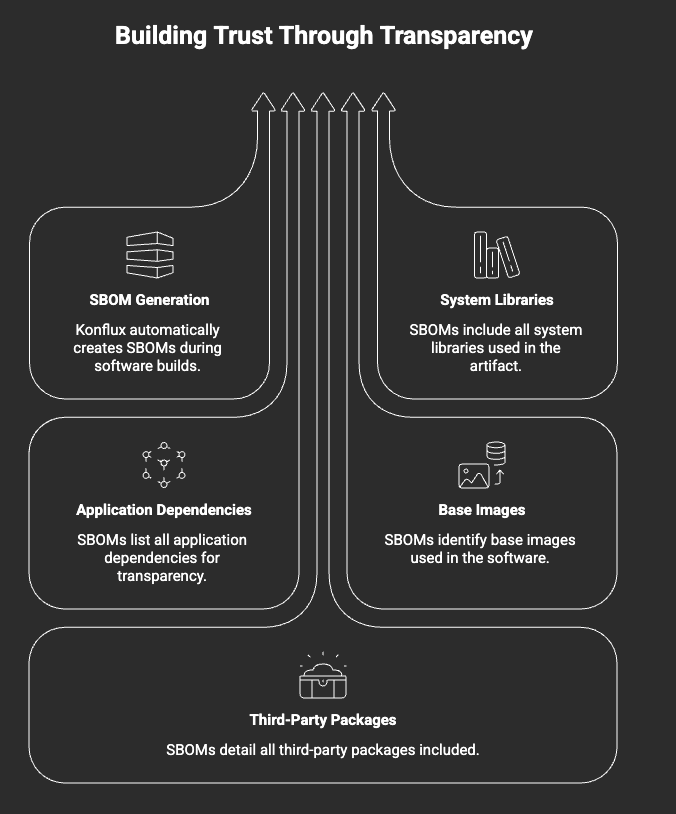
SBOMs improve visibility into software composition and make it easier to track vulnerabilities across the dependency tree.
Common SBOM standards include:
SPDX
CycloneDXArtifact Provenance
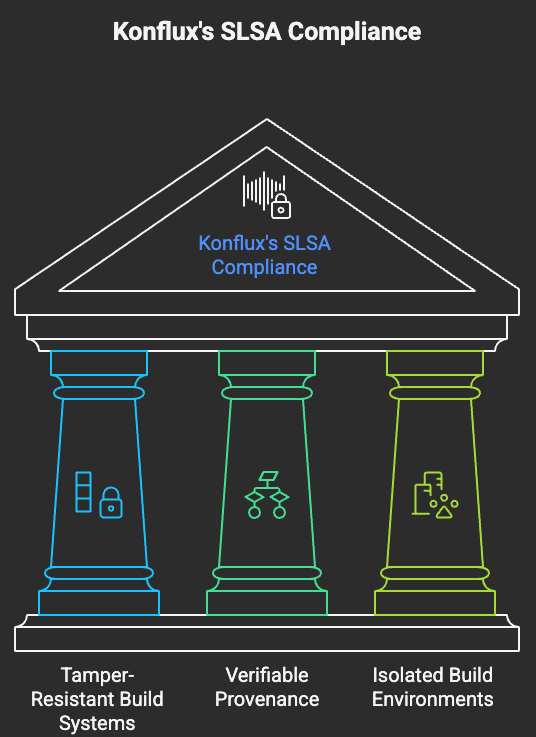
A critical part of supply chain security is artifact provenance.
Provenance metadata records information about how an artifact was built, including:
- source repository
- commit hash
- build pipeline
- build environment
Konflux generates cryptographically verifiable provenance data, ensuring that artifacts can be traced back to their origin.
This helps establish a chain of trust between source code and deployed containers.
Automated Security Scanning
Security checks are integrated directly into the pipeline.
These checks can include:
- container vulnerability scanning
- dependency analysis
- misconfiguration detection
By embedding security into the pipeline itself, Konflux ensures that insecure artifacts are detected before they reach production environments.
Policy-Based Enforcement
Konflux also integrates policy validation mechanisms to enforce security requirements.
Policies can enforce rules such as:
- container images must be signed
- SBOM must exist
- pipelines must use trusted tasks
- required tests must pass
These policies are validated automatically before artifacts can be promoted to production.
Policy-based enforcement helps organizations maintain consistent security standards across deployments.
Example Secure Workflow with Konflux
A typical secure delivery pipeline using Konflux may look like this:
1. Developer pushes code to a Git repository
2. Konflux triggers a trusted pipeline execution
3. The application is built inside a controlled environment
4. A container image is generated
5. SBOM is produced for dependency transparency
6. Security scans are executed automatically
7. Artifact provenance metadata is generated
8. Verified container images are pushed to a registry
9. Kubernetes deployments use only trusted artifactsThis workflow ensures that every deployed artifact has been verified, scanned, and traced back to its source.
Why Supply Chain Security Matters for Kubernetes
Kubernetes environments often run large distributed systems composed of many services and containers.
A single compromised image can impact:
- multiple microservices
- multiple clusters
- entire production environments
Because container images are reused across deployments, supply chain attacks can propagate rapidly.
By integrating security directly into the build pipeline, platforms like Konflux help organizations prevent compromised artifacts from entering production systems.
Benefits of Using Konflux
Using Konflux to secure Kubernetes supply chains provides several advantages.
End-to-End Artifact Trust
Artifacts are traceable from source code to deployment.
Automated Security Controls
Security checks run automatically during pipeline execution.
Reproducible Builds
Build environments are controlled and deterministic.
Improved Compliance
SBOM generation and artifact provenance help organizations meet security and regulatory requirements.
Conclusion
As Kubernetes adoption continues to grow, securing the software supply chain has become a critical priority for modern DevOps teams.
Traditional security practices often focus on runtime protection, but many modern attacks target earlier stages of the development lifecycle.
Konflux addresses this challenge by integrating security directly into the software delivery process.
By combining:
- trusted build pipelines , artifact provenance , SBOM generation, automated security policies
Konflux helps organizations establish end-to-end trust in their Kubernetes software supply chain.
Final Thoughts
Supply chain security is quickly becoming a core requirement for cloud-native platforms.
Tools like Konflux represent a shift toward secure-by-default software delivery, where verification, transparency, and policy enforcement are embedded directly into the development workflow.
For developers working in Kubernetes and DevSecOps, understanding these concepts will become increasingly important as the cloud-native ecosystem evolves.