Hey there!😁
I once found an old movie ticket in my jeans pocket and wondered how long it had been there. Developers do the same thing — except instead of movie tickets, they forget APIs. And instead of pockets, they forget them in production. That's how this story starts… with something nobody remembered existed.
The Night the Recon Rabbit Hole Got Deeper 🌙
Most of my bug bounty sessions don't start with a clear goal. It's usually just recon, some coffee, and curiosity doing the driving.
That night I was doing my usual routine:
- mapping subdomains
- checking historical URLs
- reviewing JavaScript files
- correlating infrastructure patterns
Nothing exciting at first. Just the normal noise you sift through before something interesting shows up.
Then I started reviewing publicly indexed breach data and credential leaks — not to log into anything (obviously out of scope and not ethical), but to understand naming conventions and infrastructure patterns. That alone can reveal a surprising amount.
And that's where things got interesting.
A Tiny Detail That Felt Too Specific 🧠
I noticed a recurring pattern in employee email formats tied to one company.
Some addresses included service-style suffixes that looked like internal naming conventions rather than user-facing identifiers.
That immediately raised a thought in my head:
If internal service names are predictable… API naming might be predictable too.
And predictable infrastructure is often forgotten infrastructure.
When Headers Start Talking 📡
During mass recon, I began looking closely at response behavior across multiple endpoints.
One endpoint stood out — not because of its content, but because of its headers.
There were subtle indicators suggesting:
- multiple backend services
- versioned routing
- caching behavior tied to backend selection
That combination usually means one thing:
There's more behind this gateway than what's documented.
So I started mapping behavior changes across different request variations, watching how responses changed depending on routing hints and request structure.
That's when the responses started to look different.
Not dramatically different… just enough to feel wrong.
The Moment You Realize You're Looking at an Internal API 👀
At first it was just small things:
- field names that sounded internal
- metadata that didn't belong in a public response
- inconsistent schema formatting
Those are classic signs of internal endpoints being exposed unintentionally.
Developers name things differently inside systems. And those naming habits leak clues.
When you see fields like:
- internal flags
- service identifiers
- backend-origin values
…it's usually not meant for public eyes.
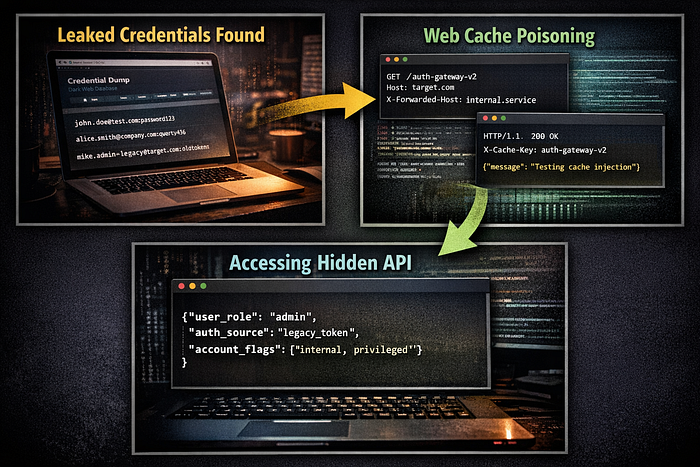
Where Credential Intelligence Came Back Into Play 🔑
Remember those breach datasets?
The interesting part wasn't the passwords. It was the patterns.
Patterns tell stories about:
- authentication flows
- service naming
- legacy systems
Using controlled testing on non-sensitive flows, it became clear that older authentication mechanisms were still partially active behind the scenes.
Not fully exposed. Not documented. But reachable in certain conditions.
And that's where risk starts to grow.
Because legacy systems often have:
- weaker validation
- outdated assumptions
- less monitoring
It's not that they're insecure by design — they're insecure because they're forgotten.
Techniques That Actually Help in Finds Like This 🛠️
If there's one thing I've learned in bug bounty, it's this:
Big bugs rarely come from one trick. They come from stacking small observations.
Here are some approaches that helped in this case:
1. Behavior-Based Recon Instead of looking only at parameters, watch how applications behave:
- response timing
- header changes
- schema differences
Applications reveal themselves in patterns.
2. Infrastructure Pattern Analysis Naming conventions can reveal:
- staging environments
- microservices
- versioned APIs
Developers are consistent — and consistency leaves footprints.
3. Cache Behavior Observation Caching layers sometimes route requests differently than expected.
Watching how responses change under different request structures can reveal:
- alternate backends
- hidden routing paths
- legacy services
This is one of the most underrated recon skills in my opinion.
4. Schema Comparison When two responses look almost identical but not quite, compare them carefully.
Sometimes a single extra field tells you everything.
A Quick Reality Check From the Dark Web 🕶️
If you spend time reading breach reports or threat intelligence feeds, you'll notice something:
Attackers aren't just stealing databases anymore. They're mapping infrastructure.
Many recent incidents discussed in underground forums revolve around:
- forgotten admin panels
- legacy APIs
- exposed internal tools
Modern attacks often follow a simple path:
- leaked information
- infrastructure discovery
- abusing forgotten systems
Not dramatic. Not flashy. Just patient observation.
And honestly, that's exactly how many bug bounty findings happen too.
Final Thoughts ☕
Bug bounty hunting sometimes feels less like hacking… …and more like detective work.
You follow patterns. You notice small inconsistencies. You trust that weird feeling when something doesn't look quite right.
And every once in a while, those tiny clues lead to something nobody even knew was still there.
Those are the bugs I enjoy the most.
Not because they're flashy. But because they remind you that security isn't just about protecting what you see…
It's about finding what everyone forgot.
Connect with Me!
- Instagram: @rev_shinchan
- Gmail: rev30102001@gmail.com

