People are afraid of coding languages a lot, They think IT industry is full of Programming, But Wait!
There's a lot beyond those lines of code :|
Cybersecurity is often misunderstood as a field where tools do everything. Many beginners believe that installing tools like Burp Suite, Nmap, or Metasploit is enough to become a hacker.
In reality, the strongest cybersecurity professionals are those who understand code.
Whether you are performing penetration testing, hunting bugs in web applications, building defensive detection systems, or analyzing malware — programming becomes your biggest advantage.
But here's the important truth:
You don't need to master every programming languages
Cybersecurity professionals typically learn languages based on their use cases, and many languages are required only to understand code, not necessarily write complex programs.
This guide explains:
- Which programming languages matter in cybersecurity
- Where each language is used
- How deeply you should learn them
- Which languages are essential vs optional
- What languages different cybersecurity roles require
By the end of this article, you will know exactly what to learn, what to ignore, and what to master.
Why Programming Matters in Cybersecurity
Programming in cybersecurity is mainly used for:
1. Automation
Security professionals constantly automate tasks like:
- Reconnaissance
- Vulnerability scanning
- Log analysis
- Exploit testing
- Data extraction
Example: Writing a Python script that automatically scans thousands of subdomains.
2. Exploit Development
Advanced security researchers write code to:
- Develop exploits
- Modify existing exploits
- Understand vulnerabilities deeply
Example: Buffer overflow exploits written in Python or C.
3. Tool Development
Many well-known cybersecurity tools are written using programming languages.
Examples:
Nmap : C/C++
Metasploit : Ruby
Burp Suite extensions : Java / Python
Recon tools : Python / Go
4. Understanding Target Systems
You cannot exploit something you don't understand.
For example:
- Web apps → JavaScript, PHP, Python
- Android apps → Java, Kotlin
- System software → C / C++
Understanding the code helps identify vulnerabilities.
The Most Important Language in Cybersecurity: Python
If there is one language every cybersecurity professional must learn, it is Python.
Python is used everywhere in cybersecurity because it is:
- Easy to learn
- Extremely powerful
- Perfect for scripting and automation
- Supported by thousands of security libraries
Common Cybersecurity Uses of Python
Python is used for:
- Recon automation
- OSINT tools
- Vulnerability scanners
- Exploit scripts
- Packet analysis
- Web scraping
- Malware analysis
- CTF scripts
Example tasks you can automate with Python:
- Subdomain enumeration
- Directory brute forcing
- Password brute force scripts
- Metadata extraction
- API exploitation
Important Python Libraries for Security
LibraryUserequestsWeb exploitation & API interactionscapyPacket crafting & sniffingsocketNetwork exploitationbeautifulsoupWeb scrapingseleniumAutomated web interactionpwntoolsExploit developmenthashlibCryptography tasks
How Much Python Should You Learn?
You don't need to become a full software engineer.
But you should master:
Must Know
- Variables
- Functions
- Loops
- Classes
- File handling
- API requests
- JSON handling
- Error handling
Advanced (Recommended)
- Multithreading
- Async programming
- Network programming
- Encryption libraries
Mastery Level
You should reach a level where you can:
- Write your own security tools
- Modify existing scripts
- Automate complex workflows
In cybersecurity, Python is a must-master language.
Bash: The Mandatory Skill
If Python is the brain, Bash is the muscle of cybersecurity.
Most security professionals work heavily inside Linux environments, especially distributions like Kali Linux.
Because of this, Bash scripting becomes essential.
What is Bash Used For?
Bash is used to:
- Automate command-line tools
- Chain security tools together
- Process large output files
- Build automation pipelines
Example:
Running subdomain enumeration → scanning → fuzzing automatically.
Example Bash Workflow
A bash script could:
- Run Subfinder
- Pipe output to httpx
- Send results to Nuclei
- Save vulnerabilities automatically
How Much Bash Should You Learn?
Focus on:
- Basic shell commands
- File operations
- Pipes
- Grep / awk / sed
- Bash scripting basics
- Cron jobs
Bash is not optional — it is a must-have skill And My Recommendation says Master bash at beginner level, What i feel is its a Basic skill every Hacker must have.
JavaScript: Essential for Web Hacking
If you want to perform Web Application Pentesting, JavaScript becomes extremely important.
Modern web applications rely heavily on JavaScript.
Understanding JavaScript helps identify vulnerabilities such as:
- XSS
- DOM-based XSS
- Token leakage
- API endpoints
- Client-side validation flaws
What to Learn in JavaScript
Focus on:
- DOM manipulation
- AJAX requests
- JSON handling
- API calls
- Local storage
- Event handling
You mainly learn JavaScript to read and understand code, not necessarily build large applications.
C and C++: The Language of Memory Exploitation
If you want to explore binary exploitation, reverse engineering, or malware analysis, you must understand C and C++.
Many system programs and operating systems are written in these languages.
Where C/C++ is Used
- Buffer overflow exploitation
- Kernel vulnerabilities
- Reverse engineering
- Malware development
- Exploit development
- Embedded system security
What to Learn
Focus on understanding:
- Memory management
- Pointers
- Stack vs heap
- Buffer overflow
- Assembly interaction
You don't necessarily need to write huge programs, but you must understand how the language interacts with memory.
SQL: Essential for Database Attacks
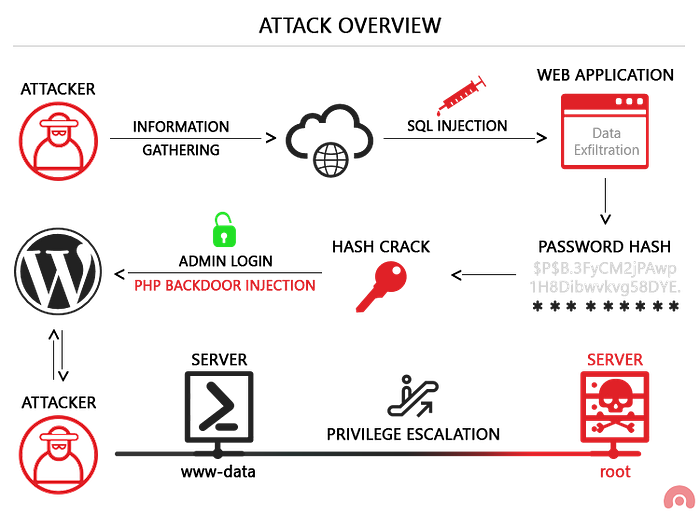
SQL is critical for understanding database vulnerabilities.
Almost every web application uses a database.
Understanding SQL allows you to exploit:
- SQL Injection
- Blind SQL Injection
- Authentication bypass
- Database enumeration
What to Learn
You only need to understand:
- SELECT
- INSERT
- UPDATE
- DELETE
- JOIN
- UNION
- WHERE clauses
You don't need to master SQL development.
Just learn enough to understand and manipulate queries.
Java / Kotlin: Android Pentesting
Android applications are primarily written in:
- Java
- Kotlin
Understanding these helps during:
- APK reverse engineering
- Mobile application pentesting
- Static analysis
- API analysis
Tools like:
- JADX
- APKTool
- MobSF
decompile apps into Java code.
Understanding Java helps identify:
- Hardcoded credentials
- API keys
- Security flaws
You mainly need code reading ability.
Go (Golang): The Rising Star
Go has become extremely popular for cybersecurity tools.
Many modern tools are written in Go because it is:
- Fast
- Lightweight
- Easy to compile
- Great for networking
Examples:
- Subfinder
- Amass
- Nuclei
- Httpx
You don't need to master Go early, but learning it later can help build high-performance security tools.
Programming Languages by Cybersecurity Domain
Web Application Security
Languages to understand:
- JavaScript
- SQL
- Python
- PHP (reading level)
Android Security
Languages:
- Java
- Kotlin
- Python (for automation)
Network Security
Languages:
- Python
- Bash
- Go
Malware Analysis
Languages:
- C
- C++
- Assembly
- Python
Exploit Development
Languages:
- Python
- C
- Assembly
Languages You Should NOT Focus On Initially
Many beginners waste time learning languages that have limited cybersecurity value early on.
Examples:
- Swift
- Rust (advanced use cases)
- Dart
- R
- MATLAB
These may be useful in specific niches but are not necessary for most cybersecurity paths.
The Real Skill: Scripting
Cybersecurity relies heavily on scripting, not large software development.
Scripting means writing small programs to automate tasks.
Example scripts:
- Subdomain scanner
- Wordlist generator
- Log parser
- Automated vulnerability tester
Most professionals write hundreds of small scripts instead of large applications.
The Recommended Cybersecurity Coding Path
If you are starting cybersecurity, follow this order:
1️⃣ Bash 2️⃣ Python (master it) 3️⃣ JavaScript (Not to master, but for understanding the code for web security) 4️⃣ SQL (Basics only — essential for injection attacks) 5️⃣ C/C++ (only for advanced exploitation) 6️⃣ Go (Not in the beginning stage — optional but powerful)
Final Wordings I infer
Cybersecurity is not about knowing every programming language.
It is about knowing the right languages for the right purpose.
Master the fundamentals, automate everything you can, and focus on understanding how systems actually work.
The strongest security professionals are not the ones who run tools.
They are the ones who build them, break them, and improve them.
If you enjoyed this guide and want more deep cybersecurity breakdowns, hacking concepts, and practical learning paths, make sure to follow for more content.
And if this article helped you learn something new, don't forget to drop a claps — it helps this guide reach more aspiring cybersecurity learners.
Till the next blog, See yaah!!