Overview
While exploring the platform, I discovered a feature that allows users to send reports directly to the support team. The form was not limited to submitting a message — it also allowed users to upload PDF attachments.
At first glance, this seemed like a normal feature designed to help users share documents with support staff.
However, this upload functionality quickly became the focus of my testing.
Discovery
I started experimenting with the PDF upload feature to understand how the platform validates files.
After several tests, I noticed that the system was mainly checking the file type or extension, without deeply inspecting the internal structure of the uploaded PDF.
This raised an interesting question: Could a modified PDF contain something more than just static content?
Key Finding
The real idea appeared when I started looking into the internal structure of PDF files.
Instead of trying to place visible links or obvious payloads inside the document, I explored a different approach.
What if the code executes before the document content even appears?
And this is where the /OpenAction feature in PDF files becomes important.
By modifying the internal structure of the PDF, I added a simple payload using the /OpenAction directive.
This feature instructs the PDF viewer to execute the action immediately when the file is opened.
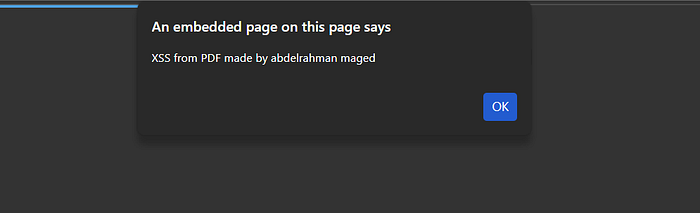
For safety purposes, the payload only displayed a simple alert message.

Vulnerability Behavior
After preparing the modified file, I uploaded it through the support report feature.
The platform accepted the file normally without detecting any issue.
When the file was previewed inside the platform, nothing happened. Some built-in viewers disable script execution for security reasons.
However, when the file was downloaded and opened locally, the payload executed instantly and the alert appeared before the PDF content was even displayed.
Impact
This behavior could potentially create a risky scenario:
- An attacker uploads a crafted PDF through the support report feature
- The file reaches internal support staff
- A staff member downloads the attachment and opens it locally
- The embedded action executes automatically when the PDF is opened
Conclusion
File upload features often appear simple and harmless.
But when uploaded files are only validated by their type or extension, they can unintentionally become delivery mechanisms for active content.
Sometimes the most interesting security findings come from the simplest features.
Finally it's Duplicated ..