Banking specific malware is not my daily world. I work across multiple client tenants at an MSSP, handling phishing triage, endpoint detections, identity alerts, cloud security events. The Latin American banking trojan ecosystem is not something I triage every morning. But I came across a piece this week about a newly discovered malware called VENON, and I could not put it down. Not because it was outside my comfort zone, but because of how much it connected to things I had already seen without fully understanding them.
That is what this article is. Me learning, processing, and sharing what I found interesting. If you are in a similar position, maybe it helps you too.
The Malware and Why It Stood Out
VENON is a banking malware targeting Brazilian users, discovered last month and documented by Brazilian cybersecurity firm ZenoX. What immediately sets it apart from the established LATAM banking trojan families like Grandoreiro, Mekotio, and Coyote is that it is written in Rust. Nearly every well-known banking trojan in this region has historically been built in Delphi, an older language that security teams have been pulling apart for years. Defenders know what Delphi malware looks like. Signatures exist. Rust changes that equation significantly. It is harder to reverse engineer, and most detection tooling was not written with Rust malware in mind.
But the language choice is not even the most interesting part. VENON is capable of targeting 33 financial institutions and digital asset platforms. It monitors active windows and browser domains, waiting for a target application or site to open before springing into action. What caught my attention specifically was one component sitting inside that larger capability: a shortcut hijacking mechanism built exclusively for the Itaú banking application.
Not Brazilian banking apps broadly. Not financial software generally. One named institution's desktop shortcut.
That level of targeting specificity says something about the people operating this.
ClickFix: I Knew This, I Just Did Not Know the Name
VENON is suspected to use a delivery technique called ClickFix to get onto the victim's machine. The victim is shown a fake error or CAPTCHA page telling them that verification has failed or something is broken. The page presents a fix, usually a PowerShell command to paste into a terminal. The victim runs it themselves, thinking they are resolving a technical issue. What actually executes is a script that downloads and runs the malware payload, typically delivered inside a ZIP archive.
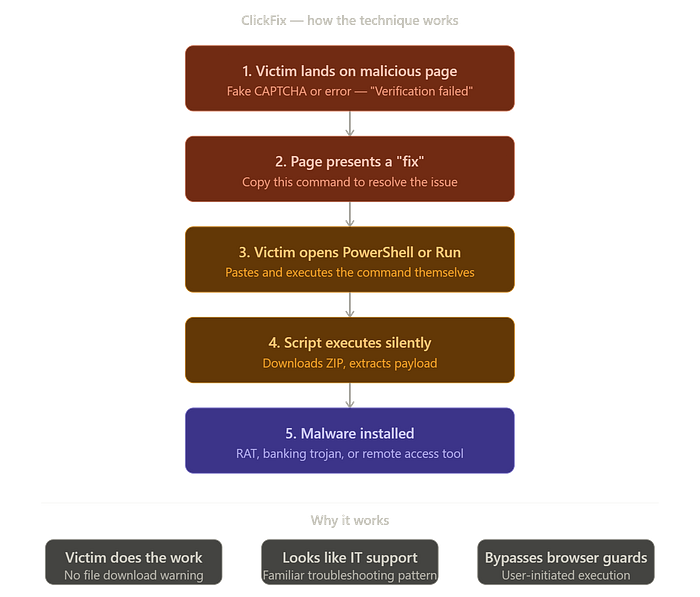
When I read this, something clicked. I had encountered exactly this in a sandbox environment. A fake CAPTCHA, a prompt to open PowerShell or Command Prompt, a command to paste. In my case, what it was trying to pull down was ScreenConnect, a remote access tool. I knew something was wrong. I did not know the technique had a name or that it was being embedded into campaigns targeting 33 banking institutions.
Knowing it now changes how I think about that case in hindsight. Remote access to the machine is the goal. Everything else, the fake page, the urgency of the prompt, the legitimate-looking instruction, is just the social engineering layer designed to make a non-technical user do the attacker's installation work for them. The people who will fall for this are not stupid. A convincing fake CAPTCHA from what looks like a legitimate site is genuinely hard to second-guess if you are not already aware this technique exists. That is the point.
Shortcut Hijacking: Invisible to Almost Everyone
This is the part of VENON I want to spend the most time on, because I think it is the technique most people, including technically aware people, would completely miss.
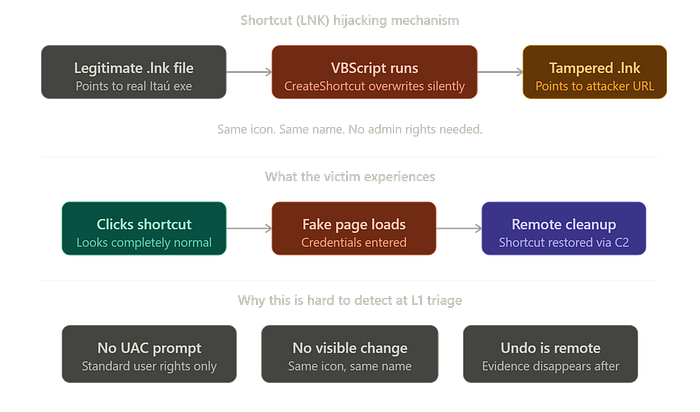
When you pin an application to your desktop or taskbar on Windows, what you are actually clicking is not the application itself. It is a .lnk shortcut file, a small pointer that tells Windows where the real executable lives. Most people never think about this. The shortcut looks like the app. It has the app's icon, the app's name. You click it, the app opens. That is the entire mental model, and there is no reason to question it.
VENON's VBScript component exploits exactly that assumption. Using the Windows Script Host Shell object, the script locates the Itaú shortcut, creates a new .lnk file at the same location with the same name and the same icon, but changes the target. Instead of pointing to the legitimate Itaú executable, it now points to an attacker-controlled page. The victim clicks what they have always clicked. They land somewhere else entirely. The overlay captures their credentials. They may not even notice anything felt wrong.
What makes this more unsettling is that it requires no administrator privileges. If the shortcut lives in the user's own Desktop or AppData folder, which most application shortcuts do, the script can overwrite it silently with standard user permissions. No UAC prompt. No warning. Nothing visually changes.
And then there is the undo.
Once the operator has what they came for, they send a remote command down the WebSocket connection to the C2 server. The VBScript runs again in reverse, restoring the original shortcut target. Everything goes back to normal. If nobody was already investigating at the point the cleanup runs, there may be no obvious trace that anything happened at all.
From a SOC perspective, whether you would catch this depends entirely on which stage you enter the investigation. An L1 analyst doing standard triage works with what is visible right now. If the shortcut has already been restored, nothing looks wrong. There is no active alert pointing you at LNK file modification history. You would need to be doing deeper forensic work, comparing file metadata, looking at what changed and when, to find the evidence that something was ever tampered with. That is not a criticism of L1 triage. It is just the reality of how these investigations are staged, and it tells you something about the discipline of whoever is running this operation. They understood that cleanup is part of the attack.
The Full Chain, Simplified
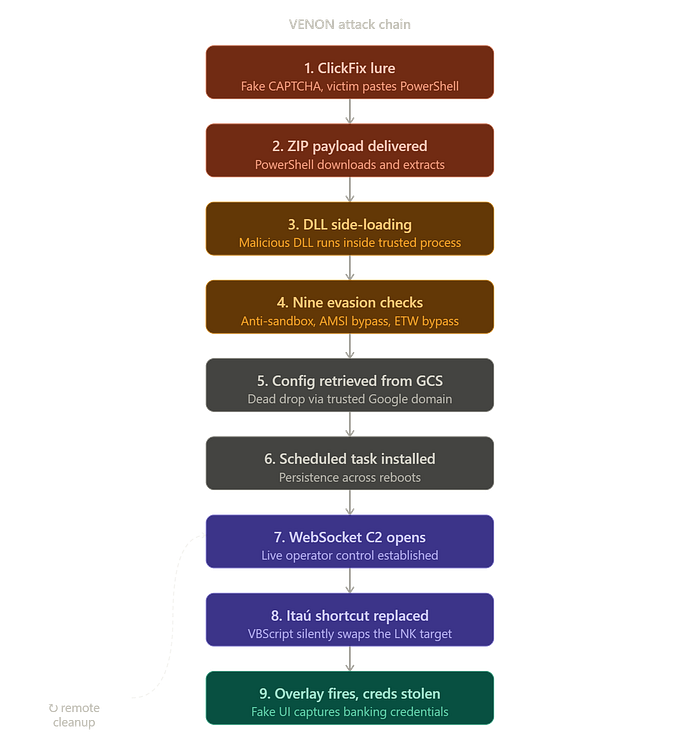
For those who want to understand how VENON moves from initial contact to credential theft, here is the sequence as I understand it:
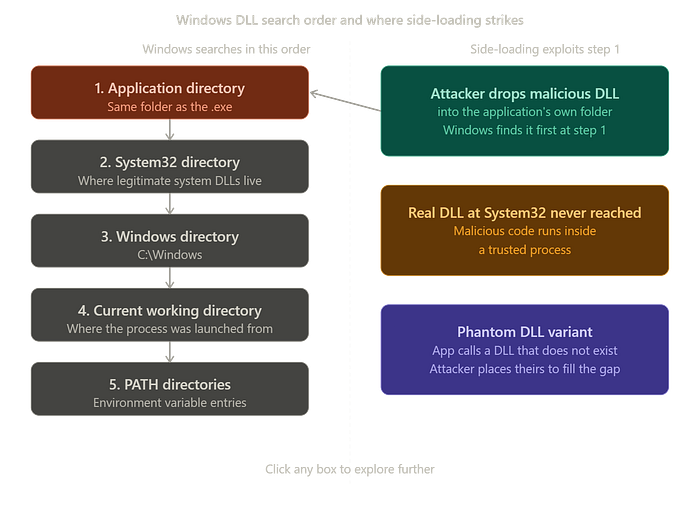
The victim is socially engineered through a ClickFix-style lure, pastes a PowerShell command, and downloads a ZIP containing the payload. DLL side-loading executes the malicious DLL inside a trusted process, so by the time anything malicious runs it is already wearing the costume of something the system trusts.
Before doing anything visible, the malware runs through nine evasion checks including anti-sandbox detection, AMSI bypass, ETW bypass, and indirect syscalls. It then reaches out to a Google Cloud Storage URL to retrieve its configuration. Using a legitimate, trusted domain for this step means the traffic blends in and the actual C2 address can be rotated without touching the binary. A scheduled task is installed for persistence so the malware survives a reboot. A WebSocket connection opens to the C2 server, giving the operator live, real-time control. The VBScript component replaces the Itaú shortcut. The malware watches for any of 33 target institutions to be opened. When one is, the overlay fires and credentials are captured. The operator sends the cleanup command. The shortcut is restored. The tracks are covered.
Every stage of that chain has a specific defensive implication. But the window to catch it is narrow at several points, and the cleanup at the end is designed to close it entirely.
AI Is Not Only Creating New Threats. It Is Removing the Barriers to Existing Ones.
ZenoX assessed that the VENON developer was already familiar with existing LATAM banking trojan capabilities but used generative AI to rewrite and expand those functions in Rust. The techniques are not new. The overlays, the window monitoring, the shortcut manipulation, all of this has existed in the LATAM ecosystem for years. What AI did here was close the gap between knowing what you want to build and being able to build it in a language that makes it significantly harder to detect.
There has always been a distinction in this industry between a script kiddie and someone who genuinely understands what they are doing. The former runs tools they did not build against targets they do not fully understand. The latter has the technical depth to build, adapt, and operate deliberately. That line is getting blurry. Someone who understands the attack concept but previously lacked the ability to implement it in Rust can now produce something in Rust with AI assistance. The barrier to entry is lower. Which means there is more entry.
For defenders, that cuts in both directions. More sophisticated attacks, more convincing phishing lures with no grammatical errors, malware ported into evasion-resistant languages by people who could not have done it two years ago. But defenders have access to the same tools. The question is whether we are using them with the same urgency. I think we need to be.
Why This Matters Even If It Is Not Your Ecosystem
VENON is targeting Brazilian users. It is not what I am triaging across my client tenants right now. But nothing about the techniques it uses is geographically restricted. Shortcut hijacking works on any Windows machine targeting any application. ClickFix works on any user who does not know to be suspicious of a fake CAPTCHA. Overlay attacks work against any web-based platform worth targeting. The LATAM banking trojan ecosystem has a documented history of expanding outward as it matures. What gets refined against high-volume Brazilian banking users does not stay in Brazil.
And even setting that aside, there is a healthcare organisation somewhere with a lean IT department and a line-of-business application that most of the SOC has never heard of. There is a shortcut on someone's desktop that nobody is watching. The technique does not care what sector you are in.
The thing I keep coming back to is this: many of the more sophisticated attacks are complicated enough that they might not be caught, especially if they are caught late. But every stage of the chain is also a stage where it could have been caught earlier. Earlier detection, at any point, limits what the attacker can do downstream. And you can only catch something earlier if you know what to look for before you are looking for it under pressure.
That is why I read articles like this even when the threat is not in my daily queue. Not because I expect to triage a VENON alert tomorrow morning. But because the day something like this shows up in an environment I am responsible for, I want to already know what I am looking at.

