Aaj Kya Seekhenge?
- Shodan kya hai bilkul basics se
- Censys kya hai Shodan se kaise alag
- Dono pe account setup + API keys
- Shodan search operators elite techniques
- Censys queries advanced recon
- Bug bounty ke liye real workflows
- Shodan + Censys + CLI tools ka combo
Kyun zaroori hai? Nmap mein tum khud scan karte ho Shodan aur Censys already scan karke rakh chuke hain! Poora internet index hua hai — tumhe sirf sahi query likhni hai aur bugs mil jaate hain! Bina ek bhi packet target pe bheje! 🤯
Pehle Samjho Yeh Kaam Kaise Karte Hain?
Google webpages index karta hai tum search karte ho → pages milte hain!
Shodan/Censys internet-connected DEVICES index karta hai tum search karte ho → exposed servers, cameras, databases milte hain!
Google Index:
"best pizza in mumbai" → Websites milti hain
Shodan/Censys Index:
"mongodb no auth india" → Unprotected databases milti hain! 😱
"apache 2.2.14 india" → Old vulnerable servers!
"default password" → Default credentials wale devices!Yeh passive recon ka ultimate tool hai target ko pata bhi nahi chalta ki tum dekh rahe ho!
Shodan vs Censys Kya Fark Hai?
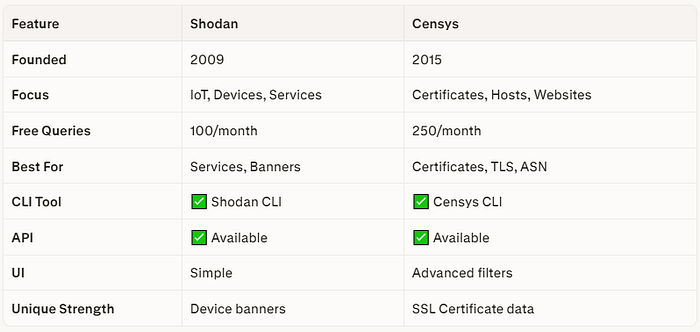
💡 Elite Strategy: Dono use karo Shodan services dhundta hai, Censys certificates se hidden subdomains nikalta hai!
PART 1: Shodan Setup
Account + API Key:
1. shodan.io pe jaao
2. Free account banao
3. "My Account" → API Key copy karo
4. Free plan: 100 queries/monthShodan CLI Install:
# Python pip se install karo
pip3 install shodan
# API key initialize karo
shodan init YOUR_API_KEY
# Test karo
shodan info
# Output: Query credits remaining: 100PART 2: Shodan Search Operators Master Karo
Basic Search: Service Ya Technology
# Web interface mein ya CLI mein:
apache # Sabhi Apache servers
nginx # Sabhi Nginx servers
"MongoDB Server Info" # Exposed MongoDB!
"redis_version" # Exposed Redis!
"elasticsearch" # Exposed Elasticsearch!Operator 1: hostname Domain Pe Focus
hostname:example.com
# example.com ke saare exposed services!
hostname:.gov.in
# Indian government exposed services!Operator 2: org Company Ka Naam
org:"Amazon"
org:"Tata Consultancy"
org:"Infosys"
# Company ke saare internet-facing devices!Operator 3: port Specific Port
port:27017 org:"Target Company"
# Target ki exposed MongoDB!
port:6379 org:"Target Company"
# Target ka exposed Redis!
port:9200 org:"Target Company"
# Target ka exposed Elasticsearch!Operator 4: country Location Filter
port:27017 country:IN
# India mein exposed MongoDB databases!
port:6379 country:IN
# India mein exposed Redis!Operator 5: product Specific Software
product:MySQL version:5.1
# Old MySQL 5.1 — vulnerabilities!
product:OpenSSH version:7.4
# Specific SSH version!
product:Apache httpd version:2.2.14
# Very old Apache!Operator 6: vuln Known CVEs!
vuln:CVE-2021-44228
# Log4Shell vulnerable servers!
vuln:CVE-2017-0144
# EternalBlue (WannaCry) vulnerable!
vuln:CVE-2021-26855
# Microsoft Exchange ProxyLogon!Warning: Yeh queries pe jo bhi milega seedha exploit mat karo! Bug bounty scope mein hai ya nahi pehle verify karo!
Operator 7: ssl Certificate Se Search
ssl:example.com
# example.com ke SSL certificate wale sabhi servers!
ssl.cert.subject.cn:example.com
# Specific certificate subject!Operator 8: before/after Time Filter
port:22 org:"Example Corp" after:2024-01-01
# 2024 ke baad exposed SSH servers!PART 3: Shodan Elite Bug Bounty Queries
Query 1: Exposed Admin Panels
http.title:"Admin Panel" org:"Target Company"
http.title:"phpMyAdmin" country:IN
http.title:"Jenkins" org:"Target Corp"
http.title:"Grafana" org:"Target"
http.title:"Kibana" org:"Target"Query 2: Default Credentials
"default password" port:80
http.title:"Router Setup" port:80 country:IN
"Authorization: Basic YWRtaW46YWRtaW4="
# YWRtaW46YWRtaW4= = admin:admin base64!Query 3: Exposed Databases
"MongoDB Server Info" -authentication
port:27017 -authentication
port:6379 -requirepass
"Elasticsearch" port:9200 -authenticationQuery 4: Git Repositories Exposed
http.title:"GitLab" org:"Target"
http.html:"Repository" http.html:"Clone" org:"Target"Query 5: India-Specific Bug Bounty
# Indian companies ke exposed services
org:"Paytm" port:27017
org:"Zomato" port:6379
org:"Flipkart" port:9200
hostname:.in port:22 product:OpenSSH version:6Shodan CLI Terminal Se Use Karo
# Basic search
shodan search "hostname:example.com"
# Port filter ke saath
shodan search "hostname:example.com" --ports
# Specific facets dekho
shodan search "org:Example Corp" --facets port
# Host info nikalo
shodan host 1.2.3.4
# Target ka poora scan history
shodan host example.com
# Alert banao — naye results notify kare
shodan alert create "example_monitor" \
"hostname:example.com" 192.168.0.0/24
# Domain se sabhi IPs + ports
shodan domain example.comPART 4: Censys Setup
Account + API Keys:
1. censys.io pe jaao
2. Free account banao (Research access)
3. "API" section mein jaao
4. API ID aur Secret copy karo
5. Free: 250 queries/monthCensys CLI Install:
pip3 install censys
# Configure karo
censys config
# API ID aur Secret enter karo
# Test karo
censys accountPART 5: Censys Search Master Karo
Censys Ka Unique Power: Certificates!
# SSL Certificate mein example.com wale sabhi hosts
parsed.names: example.com
# Yeh kaam karta hai kaise?
# Jab SSL certificate issue hota hai →
# Certificate mein domain naam hota hai →
# Censys index karta hai →
# Tum search karte ho → Hidden subdomains milte hain!Operator 1: Certificate Se Subdomains Dhundho
parsed.names: example.com
# Output:
# secret-api.example.com ← Subfinder ne nahi dhundha!
# internal.example.com ← Hidden subdomain!
# old-admin.example.com ← Forgotten admin panel!Elite Technique: Certificate Transparency Logs mein woh subdomains hote hain jo DNS pe nahi hain lekin certificate issue hua tha! Yeh Subfinder + Amass dono miss karte hain!
Operator 2: Services Search
# Specific service dhundho
services.service_name: HTTP
services.service_name: REDIS
services.service_name: ELASTICSEARCH
services.service_name: MONGODBOperator 3: Software Version
services.software.product: nginx
services.software.version: 1.14.0Operator 4: ASN Filter
autonomous_system.asn: 12345
autonomous_system.name: "Example Corporation"Operator 5: Country
location.country: India
location.country_code: INCensys CLI Commands:
# Hosts search karo
censys search "parsed.names: example.com" \
--index-type hosts
# Certificates search
censys search "parsed.names: example.com" \
--index-type certificates
# Specific host ki details
censys view 1.2.3.4 --index-type hosts
# Subdomains nikalo certificate se
censys subdomains example.comPART 6: Elite Workflows Dono Tools Combo
Workflow 1: Hidden Subdomains via Certificates
#!/bin/bash
# cert_subdomains.sh
TARGET=$1
echo "🔍 Finding subdomains via certificates: $TARGET"
# Censys CLI se
censys subdomains $TARGET 2>/dev/null > cert_subs.txt
# crt.sh (free, no login!)
curl -s "https://crt.sh/?q=%.${TARGET}&output=json" | \
python3 -c "
import json,sys
data=json.load(sys.stdin)
names=set()
for cert in data:
for name in cert.get('name_value','').split('\n'):
if '$TARGET' in name:
names.add(name.strip().lstrip('*.'))
for n in sorted(names): print(n)
" > crtsh_subs.txt
# Combine karo
cat cert_subs.txt crtsh_subs.txt | sort -u > all_cert_subs.txt
echo "✅ Total: $(wc -l < all_cert_subs.txt) subdomains via certs"
# Live check karo
cat all_cert_subs.txt | httpx -silent -status-code > cert_live.txt
echo "🌐R Lve: $(wc -l < cert_live.txt)"Workflow 2: Shodan CLI Company Scan
#!/bin/bash
# shodan_company_scan.sh
COMPANY=$1
DIR="shodan_${COMPANY}"
mkdir -p $DIR
echo "🔥 Shodan Scan: $COMPANY"
# All services
shodan search "org:\"$COMPANY\"" > $DIR/all_services.txt
# Exposed databases
shodan search "org:\"$COMPANY\" port:27017" > $DIR/mongodb.txt
shodan search "org:\"$COMPANY\" port:6379" > $DIR/redis.txt
shodan search "org:\"$COMPANY\" port:9200" > $DIR/elastic.txt
# Admin panels
shodan search "org:\"$COMPANY\" http.title:admin" \
> $DIR/admin_panels.txt
# Old software
shodan search "org:\"$COMPANY\" product:Apache version:2.2" \
> $DIR/old_apache.txt
# Summary
echo "MongoDB exposed : $(wc -l < $DIR/mongodb.txt)"
echo "Redis exposed : $(wc -l < $DIR/redis.txt)"
echo "Elastic exposed : $(wc -l < $DIR/elastic.txt)"
echo "Admin panels : $(wc -l < $DIR/admin_panels.txt)"
echo "Old Apache : $(wc -l < $DIR/old_apache.txt)"Workflow 3: Ultimate Passive Recon Pipeline
#!/bin/bash
# ultimate_passive.sh
TARGET=$1
DIR="passive_${TARGET}"
mkdir -p $DIR
echo "═══════════════════════════════════"
echo "🕵️ ULTIMATE PASSIVE RECON: $TARGET"
echo "═══════════════════════════════════"
# Step 1: Subfinder
echo "⚡ Subfinder..."
subfinder -d $TARGET -all -silent > $DIR/subfinder.txt
# Step 2: Amass passive
echo "🕸️ Amass..."
amass enum -passive -d $TARGET > $DIR/amass.txt 2>/dev/null
# Step 3: Certificate subdomains
echo "📜 Certificate Transparency..."
curl -s "https://crt.sh/?q=%.${TARGET}&output=json" | \
python3 -c "
import json,sys
try:
data=json.load(sys.stdin)
names=set()
for c in data:
for n in c.get('name_value','').split('\n'):
if '$TARGET' in n:
names.add(n.strip().lstrip('*.'))
[print(n) for n in sorted(names)]
except: pass
" > $DIR/cert_subs.txt
# Step 4: Shodan
echo "🔍 Shodan..."
shodan search "hostname:$TARGET" \
--fields ip_str,port,org,product,version \
> $DIR/shodan.txt 2>/dev/null
# Step 5: Combine all
cat $DIR/subfinder.txt \
$DIR/amass.txt \
$DIR/cert_subs.txt | sort -u > $DIR/all_subs.txt
# Step 6: Live hosts
echo "🌐 Live check..."
cat $DIR/all_subs.txt | httpx -silent \
-status-code -title -tech-detect \
> $DIR/live_hosts.txt
# Step 7: Interesting findings
echo "🎯 Interesting targets..."
cat $DIR/live_hosts.txt | grep -iE \
"admin|swagger|jenkins|grafana|kibana|
phpmyadmin|gitlab|jira" \
> $DIR/high_value.txt
echo "═══════════════════════════════════"
echo "📊 RESULTS"
echo "═══════════════════════════════════"
echo "Total Subdomains : $(wc -l < $DIR/all_subs.txt)"
echo "Live Hosts : $(wc -l < $DIR/live_hosts.txt)"
echo "High Value : $(wc -l < $DIR/high_value.txt)"
echo "Shodan Results : $(wc -l < $DIR/shodan.txt)"
echo "Cert Subdomains : $(wc -l < $DIR/cert_subs.txt)"
echo "Results in : $DIR/"
echo "═══════════════════════════════════"Free Alternative crt.sh
Shodan/Censys paid hai crt.sh bilkul FREE hai aur certificates se subdomains dhundta hai!
# Browser mein:
https://crt.sh/?q=%.example.com
# Terminal se:
curl -s "https://crt.sh/?q=%.example.com&output=json" | \
python3 -c "
import json,sys
data=json.load(sys.stdin)
subs=set()
for c in data:
for n in c['name_value'].split('\n'):
subs.add(n.strip())
[print(s) for s in sorted(subs)]
"Cheat Sheet Quick Reference
# ─── SHODAN CLI ──────────────────────────
shodan search "org:Target" # Company search
shodan search "hostname:example.com" # Domain
shodan search "port:27017 org:Target" # MongoDB
shodan host 1.2.3.4 # Host info
shodan domain example.com # Domain details
shodan alert create name "query" cidr # Monitor
# ─── SHODAN WEB QUERIES ──────────────────
hostname:example.com # By domain
org:"Company Name" # By company
port:6379 country:IN # Redis in India
vuln:CVE-2021-44228 # Log4Shell
http.title:"Admin" # Admin panels
ssl:example.com # SSL certs
# ─── CENSYS CLI ──────────────────────────
censys search "parsed.names: target.com" # Cert search
censys subdomains example.com # Subdomains
censys view 1.2.3.4 --index-type hosts # Host info
# ─── CRT.SH (FREE) ───────────────────────
curl -s "https://crt.sh/?q=%.example.com&output=json"Aaj Ka Homework
# 1. Shodan.io pe free account banao
# 2. Yeh queries try karo (public data):
shodan search "hostname:hackerone.com"
# Kya mila? Note karo
# 3. crt.sh se subdomains nikalo:
curl -s "https://crt.sh/?q=%.hackerone.com&output=json" | \
python3 -c "
import json,sys
data=json.load(sys.stdin)
subs=set()
for c in data:
for n in c['name_value'].split('\n'):
if 'hackerone' in n:
subs.add(n.strip().lstrip('*.'))
[print(s) for s in sorted(subs)]
" | head -20
# 4. Compare karo Subfinder results se —
# Cert mein kaunse extra subdomains mile?
# 5. Comment mein batao:
# Shodan search mein kya interesting mila?Quick Revision
🌍 Shodan = Internet scanner — services, banners, devices
📊 Censys = Certificate + host database
📜 crt.sh = FREE certificate transparency logs
🔍 Passive = Target ko pata nahi chalta
💡 Combo = Shodan (services) + Censys (certs) = Maximum coverage
🎯 Bug Types = Exposed DBs, Admin panels, Default creds,
Old versions, Hidden subdomains
🔥 Elite = Subfinder+Amass+Shodan+Censys+crt.sh = COMPLETE!Meri Baat…
Ek baar maine ek company ke liye bug bounty kiya normal recon mein kuch nahi mila
Phir Shodan pe gaya:
org:"Target Company" port:6379Ek result aaya
Redis server no authentication!
redis-cli -h [target-ip] -p 6379
> KEYS *
# 50,000+ session tokens!
> GET session:admin_user_12345
# Admin ka active session token!Session token use kiya → Admin account access!
Bounty: $4,500 Critical! 🎉
Lesson: Normal recon sab karte hain Shodan woh dhundta hai jo baaki miss karte hain!
Recon section complete hone wala hai! Agle article mein Google Dorks Google ko bana do apna hacking tool! Bilkul free, bilkul powerful! 🔥
HackerMD Bug Bounty Hunter | Cybersecurity Researcher GitHub: BotGJ16 | Medium: @HackerMD
Previous: Article #9 Nmap Port Scanning Next: Article #11 Google Dorks: Google Se Bugs Dhundho Free Mein!
#Shodan #Censys #BugBounty #Recon #EthicalHacking #Hinglish #PassiveRecon #HackerMD