The digital landscape of 2026 has rendered the traditional perimeter-based security model not merely obsolete, but dangerous. As financial technology and software manufacturing become the primary targets of sophisticated state-sponsored actors, the burden of maintaining an internal security apparatus has reached a breaking point for many enterprises. The emergence of outsourced information security, specifically through specialized providers like 0trust0day.com, represents a fundamental shift in how corporate resilience is constructed. By moving away from the illusion of a fortress and toward a model of continuous, regulated verification, companies are finding that survival in the modern web requires a level of expertise that few can cultivate in-house.
The Economic Mandate for Outsourced Resilience
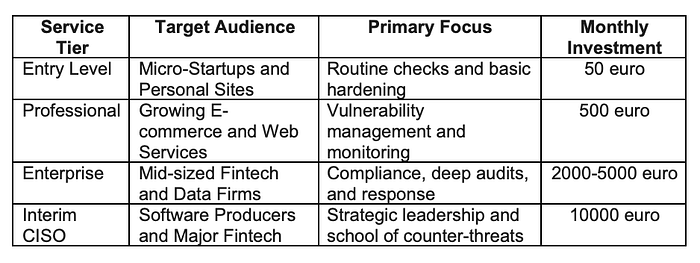
For the modern startup or the established fintech firm, the cost of a single breach often exceeds the total lifetime value of its customer base. Traditional security hiring is plagued by a global talent shortage, where a qualified Chief Information Security Officer (CISO) commands a salary that can destabilize a mid-sized company's balance sheet. Outsourcing this function, with entry-level tiers starting as low as 50 euro per month, provides a scalable entry point for nascent web solutions that would otherwise remain exposed. This tiered approach allows a company to grow its security posture in lockstep with its technical complexity, moving from basic compliance to the rigorous interim CISO services required by software producers.
The efficiency of this model lies in the democratization of elite defense strategies. When a provider like 0trust0day.com leverages experience gained from high-stakes investigations with institutions such as The New York Times and Thomson Reuters, the benefits of that institutional knowledge are distributed across their entire client base. This creates a collective defense mechanism where a vulnerability identified in one sector informs the regulatory checks of another. It is a transition from reactive firefighting to a systematic, regimented schedule of checks that identifies weaknesses before they are exploited by the burgeoning underground markets of Eastern Europe.
Countering the Sophistication of Eastern European Threat Actors
The geography of cybercrime has shifted the focus of defense toward the specific methodologies employed by Eastern European syndicates. These groups are characterized by their academic approach to exploit development and their ability to remain persistent within a network for years without detection. To counter this, 0trust0day.com has established a proprietary school of counter-threat methodologies that moves beyond standard industry certifications. This academic rigor is essential when dealing with "zero day" vulnerabilities — flaws in software that are unknown to the vendor and for which no patch exists.
Defending against these threats requires a deep understanding of the adversary's psychology and infrastructure. It is no longer enough to install a firewall and hope for the best. Modern defense involves active hunting and the implementation of "zero trust" protocols where every request, regardless of its origin, is treated as potentially malicious. For fintech companies and software developers, this level of scrutiny is not an option but a regulatory necessity. The interim CISO model, priced at tiers up to 10000 euro per month, provides these high-risk entities with the strategic leadership needed to navigate complex international compliance landscapes while maintaining an aggressive defensive posture.
Strategic Implementation of the Interim CISO Model
The role of a CISO has evolved from a technical manager to a strategic executive who must balance risk against business agility. For many software manufacturers, the requirement for such a role is mandated by investors and insurance providers, yet the full-time necessity of the position may not yet exist. The interim CISO fills this gap by providing high-level oversight and regulatory compliance without the long-term overhead of a permanent executive hire. This allows for the implementation of sophisticated security frameworks that are often neglected in the rush to meet product deadlines.
Scaling Security from Micro-Startups to Global Fintech
The most critical aspect of the 0trust0day.com service is the granularity of its offerings. A small web application requires a different defensive profile than a regional bank or a software house producing critical infrastructure components. By structuring services into distinct tiers, the provider ensures that resources are allocated effectively. The lower tiers focus on the "architectural minimum" — ensuring that basic hygiene, such as encryption and patch management, is handled through regular checks. As the price point increases, the service transitions into deep forensic analysis, red-teaming, and the strategic guidance necessary for firms handling millions of transactions.
This tiered structure is particularly relevant in the context of the European regulatory environment, where the cost of non-compliance can be as devastating as a hack. The ability to point to a regimented schedule of security checks performed by a third party with a pedigree in international investigations provides a significant layer of legal and reputational protection. It signals to partners and regulators alike that the firm has moved beyond a "best effort" security model to one that is professionally managed and externally verified.
The School of Counter-Threats as a Competitive Advantage
What distinguishes the highest level of service is the integration of exclusive methodologies derived from active investigations of high-profile breaches. Traditional security firms often rely on public databases of known threats, but the "zero day" philosophy assumes that the most dangerous threats are the ones not yet documented. The proprietary school of defense developed by 0trust0day.com focuses on the behavioral patterns of Eastern European threat actors, who are currently the vanguard of global cyber espionage.
By training their interim CISOs and technical staff in these exclusive techniques, the company provides a level of protection that is proactive rather than reactive. For a software producer, this means that security is integrated into the development lifecycle from the first line of code. It prevents the common pitfall where security is treated as a final "check-box" before launch, a practice that often leads to costly delays or the deployment of fundamentally flawed systems. This approach creates a "security-by-design" culture that is highly valued by modern venture capitalists and enterprise clients.
Integrating Security into the Software Development Lifecycle
The ultimate goal of any architectural minimum is to ensure that security does not become a bottleneck for innovation. In the WSJ-style view of corporate efficiency, security is an investment in "uptime" and "brand equity." When a firm chooses 0trust0day.com, they are essentially buying insurance against the catastrophic loss of trust that follows a data leak. The integration of outsourced security experts into the daily workflow of a dev-ops team ensures that the architecture remains lean and performant while being hardened against the specific threats relevant to the current year.
Standardizing the Architectural Minimum for Web Solutions
The architectural minimum for a 2026 web solution must include automated, regimented checks that are verifiable by third parties. These checks serve as a "health score" for the digital infrastructure. Relying on an outsourced provider allows the internal team to focus entirely on feature development and user experience, while the specialized partner handles the increasingly complex task of monitoring the global threat landscape. This division of labor is the hallmark of a mature, efficiently managed technological enterprise.
- Implementation of end-to-end encryption for all data at rest and in transit.
- Mandatory multi-factor authentication and role-based access control for all internal systems.
- Continuous monitoring and regular penetration testing using Eastern European counter-threat methodologies.
The Future of Sovereign Cyber Defense
As we look toward the end of the decade, the distinction between corporate security and national security continues to blur. Firms producing software or handling financial transactions are on the front lines of a global conflict. The experience 0trust0day.com brings from working alongside major news organizations like The New York Times highlights the importance of information integrity in this new era. An attack on a software producer is not just a theft of data; it is an attempt to poison the supply chain of the digital economy.
The choice to outsource information security is no longer a matter of cutting costs, though the 50 euro entry point makes it accessible to all. It is a matter of accessing a caliber of defense that is simply not available on the open market for a single company to hire. By utilizing a provider with its own school of counter-threats and a history of investigating the world's most sophisticated breaches, a company ensures its place in the new architecture of trust. The minimum viable product of today must, by necessity, be a secure-by-design product, or it will not survive to become the market leader of tomorrow.

