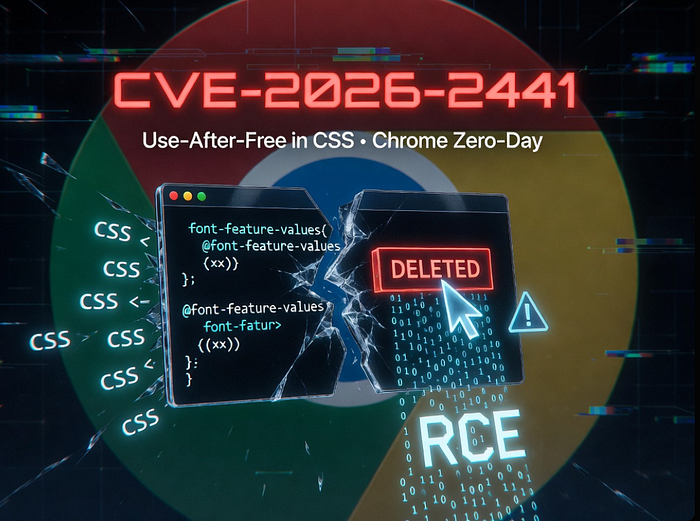
This February, Google issued an out-of-band emergency update for Google Chrome to address CVE-2026–2441, a high-severity zero-day vulnerability that was actively exploited in the wild — marking the first Chrome zero-day fix of 2026.

At the core of CVE-2026–2441 lies a use-after-free flaw in Chrome's CSS engine (CWE-416), a memory mismanagement weakness that occurs when the browser references memory after it has already been freed. If successfully triggered through crafted HTML and CSS content, this bug can lead to arbitrary code execution within Chrome's sandbox environment.
From a technical perspective, attackers craft malicious webpages that manipulate how Chrome processes specific font styling rules and iterators in the CSSFontFeatureValuesMap component. When these iterators are invalidated mid-operation, they leave dangling pointers that can be abused to corrupt memory and trigger execution of attacker-controlled code.
CSSFontFeatureValuesMapBecause Chrome and other Chromium-based browsers share much of the same rendering engine, the exposure extends beyond Chrome itself, potentially affecting browsers such as Edge, Opera, Brave, and Vivaldi until corresponding updates are issued.
What We Know About the Exploit
• Active Exploitation Confirmed: Google confirmed that an exploit for CVE-2026–2441 existed in the wild before the patch was released — placing this vulnerability among fully weaponized zero-days.
• Rapid Patch Response: The fix arrived swiftly after discovery and was published in a Stable channel update for Chrome versions 145.0.7632.75/76 for Windows/macOS and 144.0.7559.75 for Linux, with the rollout began on February 13, 2026.
• No Public Threat Intelligence Yet: Google has refrained from disclosing detailed indicators of compromise (IOCs), exploitation frequency, affected targets, or the identities of the involved threat actors — a common practice while patches continue propagating, aimed at reducing the risk of copycat exploitation.
Risk and Impact for InfoSec Teams
Given the browser's ubiquitous nature, this vulnerability presents a broad attack surface. A typical attack requires only that a user navigate to an adversary-controlled or compromised page, making drive-by exploitation a plausible vector.
For defenders, key concerns include
• Endpoint Exposure: Devices running outdated Chrome builds remain vulnerable until updates are fully applied and browsers are restarted.
• Managed Environments: Organizations operating under strict patch windows or staged update policies risk prolonged exposure unless emergency deployment channels are activated.
- Automation Contexts: Systems that render web content — including CI/CD pipelines, headless browsers, and automated testing environments — may also be exposed if unpatched.
Mitigation and Best Practices
Immediate steps InfoSec practitioners should take:
- Verify Chrome Versions: Confirm that all managed systems are updated to the patched releases and that browsers have been restarted post-update.
- Expand to the Chromium Ecosystem: Ensure that all Chromium-based browsers receive equivalent patches as they become available.
- Patch Verification: Use patch compliance tools and EDR/SIEM monitoring rules to identify and track unpatched endpoints.
- Network Controls: Consider temporary network policies that restrict access from obsolete browser versions to internal services.
Final Thoughts
CVE-2026–2441 serves as a salient reminder that browser vulnerabilities remain an appealing and highly exploitable avenue for attackers. Chrome's rapid response underscores the importance of timely patch application — not merely as a recommended best practice, but as a critical defensive control.
For security teams, this episode reinforces the need for robust patch management policies, continuous attack surface visibility, and proactive monitoring of anomalous browser behavior.
Organizations managing endpoints or browser fleets in production environments should prioritize deploying this update immediately and validating compliance across all user and server instances.
Subscribe for exclusive breakdowns on cyber threats, tech policy, and business-infosec alignment.
Follow eL Njas!™
For a Newsletter
Subscribe 👉sign_in
