Enumeration
HTTP (5000)
After accessing the target on port 5000, I was presented with a web application.

I checked the /robots.txt file, which is commonly used to specify restricted directories for web crawlers. This file revealed a disallowed directory:
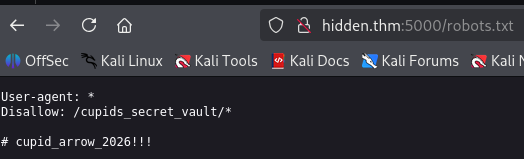
Additionally, a commented line was present. This comment appeared to contain a password or credential, which could potentially be used for authentication.
This demonstrates improper exposure of sensitive in publicly accessible files.
/cupids_secret_vault
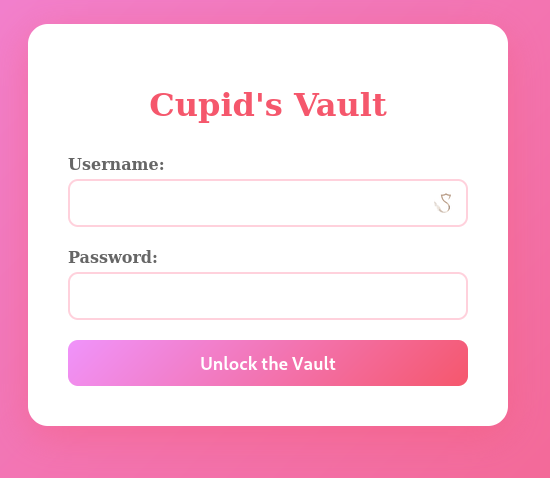
Here I found Cupid's Secret Vault.

To further enumerate the application, I performed directory enumeration and discovered an administrator endpoint:
[17:15:00] 200 - 2KB - /cupids_secret_vault/administrator/administrator
The endpoint contained a login form, indicating that administrative access was protected via authentication.
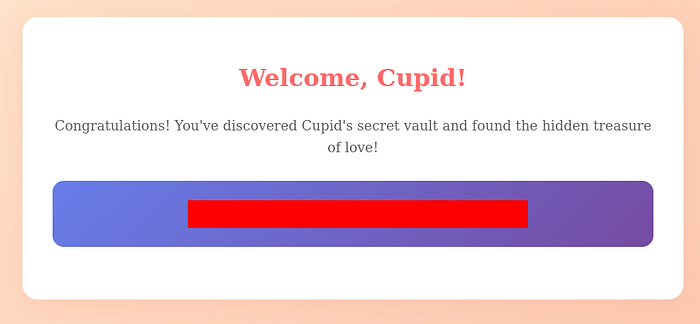
Using the password obtained from robots.txt and attempting common usernames such as "admin" I successfully authenticated to the administrator panel and gained access to Cupid's Secret Vault.
Root Cause
The vulnerability exists due to sensitive credentials being exposed in the robots.txt file. Since this file is publicly accessible, attackers can easily discover hidden directories and extract authentication information.
Observation leads. Exploitation follows
- P4NTHR

