Welcome back to the Metasploitable exploitation series. Today, we'll enumerate open ports on the target machine and analyze a bind shell service. We'll demonstrate how to identify the service, connect to it, and assess the level of access it provides.
What is a Bind shell ?
A bind shell is a type of shell where a compromised machine opens a port and "binds" a command-line interface (like Bash or sh) to that port. This means the attacker can connect directly to the target system by reaching that open port over the network. Once connected, the attacker gains remote command execution on the machine. Bind shells are straightforward to use but rely on the target system being reachable from the attacker's machine, which can be limited by firewalls or network restrictions blocking inbound connections.
What is a Reverse Shell ?
A reverse shell, on the other hand, works in the opposite direction. Instead of the attacker connecting to the target, the compromised machine initiates an outbound connection back to the attacker's system. The attacker sets up a listener, and once the connection is established, they gain command-line access to the target. Reverse shells are often more effective in real-world scenarios because outbound connections are usually allowed through firewalls, making them easier to establish even in restricted network environments.
What is the difference between the two ?
The key difference between the two lies in who initiates the connection and how they interact with network defenses. A bind shell requires the attacker to connect into the target (inbound connection), while a reverse shell has the target connect out to the attacker (outbound connection). Because of this, bind shells are simpler but less reliable in secured environments, whereas reverse shells are more flexible and commonly used in penetration testing and real-world attacks due to their ability to bypass firewall restrictions.
Step 1 :
To begin the assessment, we performed a service enumeration scan on the target machine using Nmap. This helps identify open ports and the services running on them. We used the command nmap -sV -T4 192.168.85.129, where the -sV flag enables service version detection and -T4 increases the scan speed for faster results in a lab environment. This scan provides valuable insight into potential entry points, including any exposed or misconfigured services such as a bind shell.
nmap -sV -T4 192.168.85.129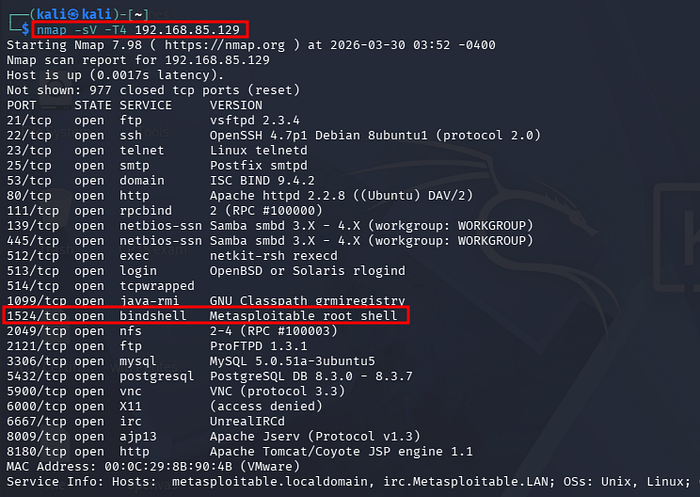
Based on the scan results, we identified an open port associated with a potential bind shell service. With this information, the next step is to attempt a connection to the target and verify whether the shell is accessible. To do this, we will use Netcat, a versatile networking tool often used for connecting to open ports and interacting with services. By establishing a connection to the bind shell, we can determine if it provides direct command execution on the target system.
Step 2 :
To connect to the bind shell, we use the command nc -nv 192.168.85.129 1524. In this command, Netcat is used to initiate a connection to the target machine. The IP address 192.168.85.129 represents the Metasploitable system, while 1524 is the port on which the bind shell service is running. The -n flag disables DNS resolution for faster connections, and -v enables verbose output to provide feedback on the connection status. If the service is accessible, this command allows us to establish a direct connection to the bind shell and interact with the target system.
nc -nv 192.168.85.129 1524
As shown, we were able to successfully connect to the bind shell without any authentication, immediately gaining root-level access to the system. This indicates a critical misconfiguration, as it allows unrestricted control over the machine. With this level of access, an attacker could execute commands, modify or delete files, install malicious software, or further pivot within the network. In a real-world scenario, this would represent a complete system compromise and a severe security risk.
Mitigation
To mitigate this vulnerability, the bind shell service must be identified and removed immediately. Unnecessary open ports should be closed, and firewall rules should be configured to block unauthorized inbound connections. Strong authentication must be enforced, and direct root access should be disabled. Regular system updates, network scans, and continuous monitoring should also be implemented to detect and prevent similar issues.
Conclusion
In this lab, we identified an exposed bind shell through enumeration and successfully connected to it using Netcat, gaining root access without authentication. This demonstrates how misconfigured services can lead to complete system compromise. Proper security controls, including service hardening and network restrictions, are essential to prevent such vulnerabilities in real-world environments.

