Hello guys! 📨🧑💻
I'm Cyber Security Researcher from Myanmar. Today, I'm excited to share a new tool specifically designed for Web Security Researchers and Bug Hunters. It targets a common yet critical issue: GraphQL Misconfigurations.
I developed this Python Automation Tool to easily detect High-Risk Database Information Disclosure vulnerabilities by leveraging GraphQL Introspection.
🔍 Why did I decide to publish this tool? I first discovered the impact of this specific bug around January 2026. At that time, I found that this vulnerability affected over 3.4k global domains. I have personally reported it to about half of them and successfully collected several bounties.
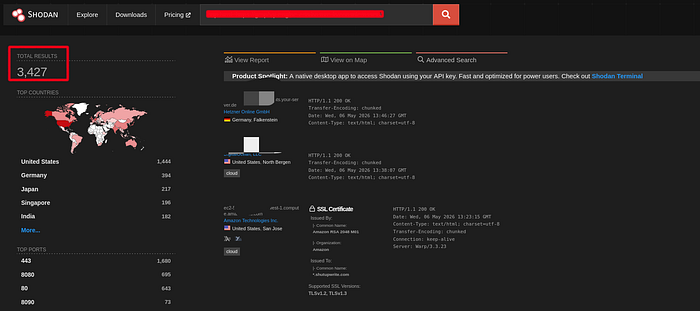
Note: Since I am still active in reporting these, I won't be sharing the Shodan dorks or giving them out via DM. 🫡
Originally, I submitted this to the vendor to claim a CVE. However, because it's a misconfiguration bug used within an exploit chain, they decided not to assign a CVE. Instead of letting the research go to waste, I thought: "If I can't get a CVE, at least my fellow hunters can find this tool useful." So, I decided to go public.
⚙️ How it works & Features Using the tool is straightforward. You just need the domain and the GraphQL endpoint. Command: $ python3 ginja.py [domain] [endpoint]
The user interface of this tool is like following:
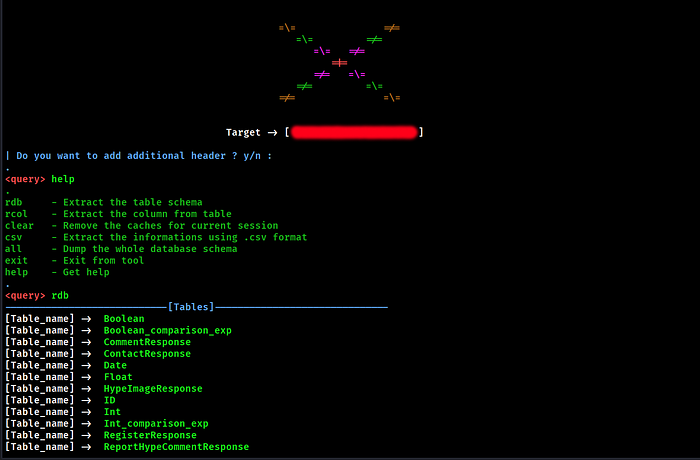
💻 Key Features: User-Friendly: Just input the target domain and the GraphQL API route. Flexible Testing: You can test for Unauthorized Access (No Token) or provide an existing Auth Token/Authorization Header for deeper testing. Full Automation: No more manual schema hunting. The tool automatically checks if GraphQL schemas are leaking sensitive database information.
- You can check the poc & usage video in my facebook page.
🚨 The Vulnerability: Why Introspection Matters? This tool works specifically on APIs where GraphQL Introspection is enabled. In a production environment, leaving Introspection enabled is a significant misconfiguration. It allows attackers to query the system for information about its internal schema, effectively handing them a map of your entire database structure.
💻 Installation You can find the source code and installation guide here: 🔗 GitHub: https://github.com/m00nisSmiling/ginja
⚠️ Disclaimer This tool is published strictly for: - Educational Purposes - Authorized Pentesting Engagements (where you have explicit permission).
Please do not use this tool for unauthorized attacks. Always ensure your actions remain legal and ethical. The responsibility lies with the user. 🫵
Happy Hunting! ✌️ #moonissmiling #GraphQL #BugBounty #CyberSecurity #InfoSec #Python #Automation
