📩 Read for Free CLICK HERE.
Hi, I'm Rivek Raj Tamang (RivuDon), a Security Researcher, Bug Hunter, and Ethical Hacker with a Master's in Cybersecurity, a Certified Ethical Hacker from Sikkim, India. I have secured numerous companies, received bounties, swags, Hall of Fames mentions, Letter of Appreciation / Recognition, CVEs and more.
Feel free to connect with me! You can find out more about me on my LinkedIn, I am active there.
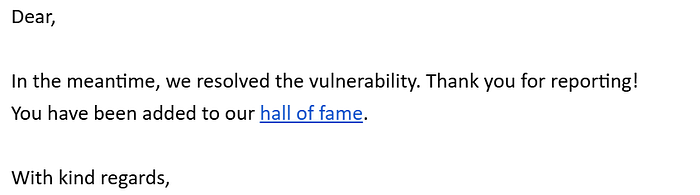
Hi readers, this write-up is a story on how I got a Hall of Fame at one of the top UEFA Champions League playing clubs. It was actually a really fun bug to discover as well.
Without further ado, let's get started!
The Hunt Begins
Firstly, let me tell you something about myself, I am deeply in love with football. I started playing when I was a small kid and have loved it ever since. Playing with my friends, dribbling like crazy, and scoring goals is what I live for. Even now that I'm a bit older, I'm still proud to say that I make time to regularly play football on weekends with my friends and brothers. With that aside, let's start the hunt.
It all started one day when I was looking for a fresh target to hunt, and I stumbled upon this one. To my surprise, it was a UEFA Champions League club which was absolutely crazy for me, so without a second thought I decided to hunt for it.
For those who don't know what UEFA Champions League is, it is one of the most celebrated football club tournaments in Europe, organized by Union of European Football Associations, it features some of the best football clubs in the world. For example, the club with the most tournament wins: Real Madrid CF, which featured "Mr. UCL" himself the most famous person in the entire world Cristiano Ronaldo (CR7).

The Bug
For security reasons, I won't disclose the target in this article. Let's assume the scope was footballclub.com.
After selecting the target, I did the usual things like any bug hunter would do, that is to collect subdomains, perform recon and check its tech stack.
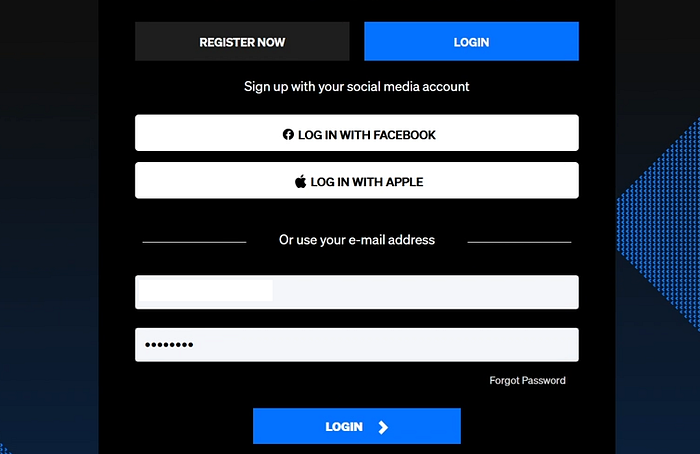
These days I am really liking the manual approach of authentication and authorization bugs along with business logic errors, so naturally I found a subdomain that has login and tickets feature, since they are a club, they sell tickets for their matches.
Application flow
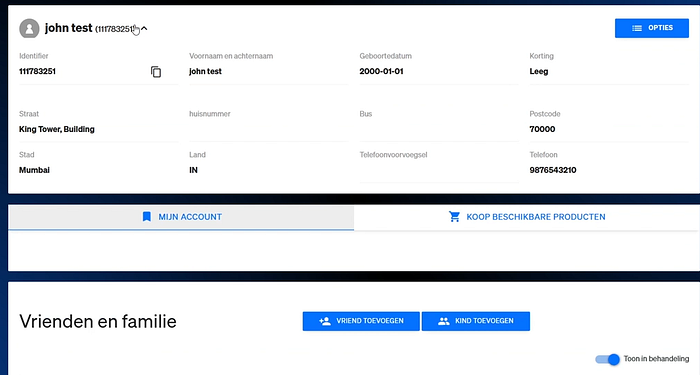
Login Page: login.footballclub.com The login page contained email login and a few SSO options, like any normal login page, however after successfully logging in, the page redirected to another subdomain called tickets.footballclub.com There, users could add their profile details such as address, phone numbers, PII and members. In the members section you can add any member with their information as well. So that was a basic gist of the application flow.
Hacker Mindset
Now that we understand the application flow, let us try to think like a hacker and try to break the flow, Since the goal would be to potentially leak the PII and maybe a golden goal would be to break the Authorization/ Authentication flow. So, I tried to do so.
The winning Goal
I basically logged in with a valid account first, filled up all the PII details and added the member with their details, checked the PII details in the profile section endpoint like tickets.footballclub.com/profile and clicked the log out button, waited for the website to load completely then I simply clicked the browser back button to check if it was handling a proper session management and cache-control issue, Surprisingly, it did not handle this properly and leaked all the PII details and the member details. Great! We found a bug, However, this was actually a low severity bug even though it is leaking PII, So I thought, let's try the extraordinary. Wouldn't it be epic if we managed to add members even after logout? and see if it is actually checking authentication and authorization properly, So I took the shot.
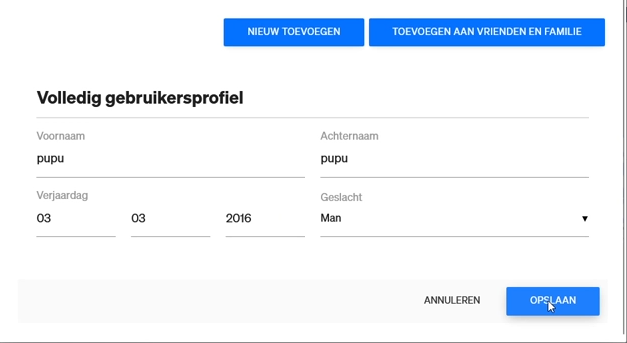
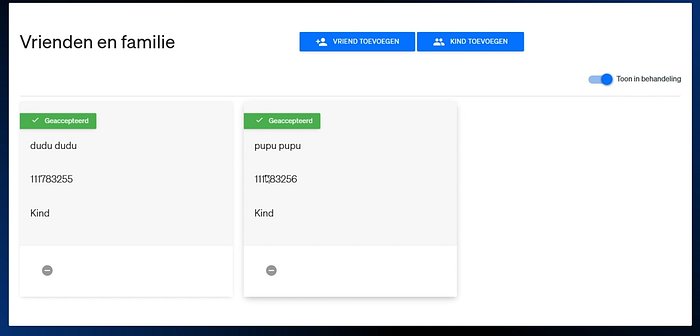
I logged in again, added the PII details and member details, on the profile endpoint, clicked the log out button, waited for some time then pressed the browser back button, saw the PII leak but then on the same page remember there was a member add option with their details, So I tried adding a new member with their details even though I was completely logged out of the session, The page kept loading with a small bar in the member addition section, I waited for few minutes then re-logged in using the same credentials and Guess what? We had scored an Epic Goal, The new member had been successfully added. This meant that not only was the application bugged with session management issue, cache-control but it also lacked proper authentication/authorization checks which allowed editable actions even after logout.

Vulnerability Summary
Type: Session Management + Cache-Control Issue
Impact: PII Exposure + Post-logout Authorization Bypass
Severity: Medium-High (Due to post-logout modification)
Tip: Understand the application thoroughly, try to think like a hacker, understand what needs to be broken, and attempt something extraordinary. Hack the World!
The Win
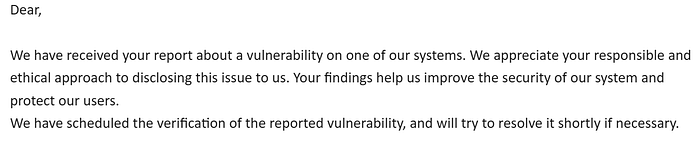
After finding the bug, I made a POC video, wrote a detailed report including detailed steps to reproduce and POC then reported my findings to them and here were their responses.
Happy Hacking✨
The End
If you find this article helpful, please do follow, claps and leave a comment to read more from me and encourage me to write more. ♥️
🎯Read my other Bug Bounty Writeups here ⬇️
Feel Free to connect with me on LinkedIn: (P.S. Do drop a message when sending a connection request.) https://www.linkedin.com/in/rivektamang/
🧑🏻💻Interested to start Bug Bounty / Ethical Hacking and Cybersecurity
Book a 1:1 mentor session with me: ➡️ RivuDon — Rivek Raj Tamang