Introduction
Apple's iPhone is widely known for its strong security architecture, designed to protect users from malware and unauthorized access. However, even the most secure systems are not immune to advanced threats.
One of the latest examples is DarkSword, a highly sophisticated iOS exploit chain used to deploy spyware. Recent reports indicate that this threat has affected users in multiple regions, including Malaysia, highlighting the growing reach of advanced cyber operations.
What is DarkSword?
DarkSword is an advanced exploit chain targeting iOS devices.
Rather than a single vulnerability, it is a combination of multiple security flaws that work together to:
- Compromise iPhones through the browser
- Bypass Apple's built-in protections
- Gain deep system-level (kernel) access
- Deploy spyware without user awareness
This type of attack is typically associated with:
- Commercial spyware vendors
- Nation-state or state-linked actors
- Highly advanced threat groups
Timeline of DarkSword observations and vulnerability patches

How the Attack Works
DarkSword operates through a multi-stage exploit chain, designed to fully compromise a device with minimal or no user interaction.
1. Initial Exploitation (WebKit)
The attack begins when a user visits a malicious or compromised website. A vulnerability in WebKit (Safari's browser engine) is exploited to execute code.
2. Sandbox Escape
iOS applications normally run in a restricted environment (sandbox). DarkSword bypasses this restriction, allowing access beyond the browser.
3. Kernel-Level Exploitation
The exploit chain then targets the iOS kernel, the core of the operating system. This step enables:
- Privilege escalation
- Full control over the device
4. Spyware Deployment
Once control is achieved, spyware is deployed to:
- Monitor user activity
- Extract sensitive data
- Operate stealthily with minimal traces
What Data Can Be Compromised?
A successful DarkSword infection can expose:
- Private messages and communications
- Call logs and contact information
- Location data
- Photos, files, and notes
- Potential access to device sensors (e.g., microphone)
The level of access depends on the final privileges obtained during exploitation.
Targeting and Regional Impact
Threat intelligence reports indicate that Malaysia is among the countries affected by DarkSword campaigns, alongside other regions.
This reflects a broader trend:
Advanced surveillance tools are increasingly being deployed beyond traditional high-profile targets.
Why DarkSword is Significant
DarkSword stands out due to its technical sophistication:
- Uses multiple chained vulnerabilities
- Requires little to no user interaction
- Bypasses key iOS security mechanisms
- Operates with minimal forensic traces
- Designed for targeted surveillance
Unlike common threats, this type of attack focuses on stealth and persistence, making detection extremely difficult.
Mitigation and Protection
Although DarkSword is advanced, there are still effective defensive measures:
Keep iOS Updated
Apple has released security patches addressing the vulnerabilities used in such exploit chains. Regular updates are critical.
Enable Lockdown Mode (High-Risk Users)
Lockdown Mode reduces the attack surface by limiting certain features such as web technologies.
Practice Safe Browsing
Avoid visiting:
- Untrusted or suspicious websites
- Links from unknown sources
Avoid Device Modification
Do not jailbreak your device, as this weakens built-in security protections.
Conclusion
DarkSword highlights the evolving nature of cyber threats against mobile devices. Even platforms known for strong security can be targeted using advanced exploit techniques.
While these attacks are often highly targeted, they serve as a reminder that:
- Security is constantly being tested
- Threat actors are becoming more sophisticated
- Staying updated and informed is essential
In today's threat landscape, awareness and timely updates remain the most effective defenses.
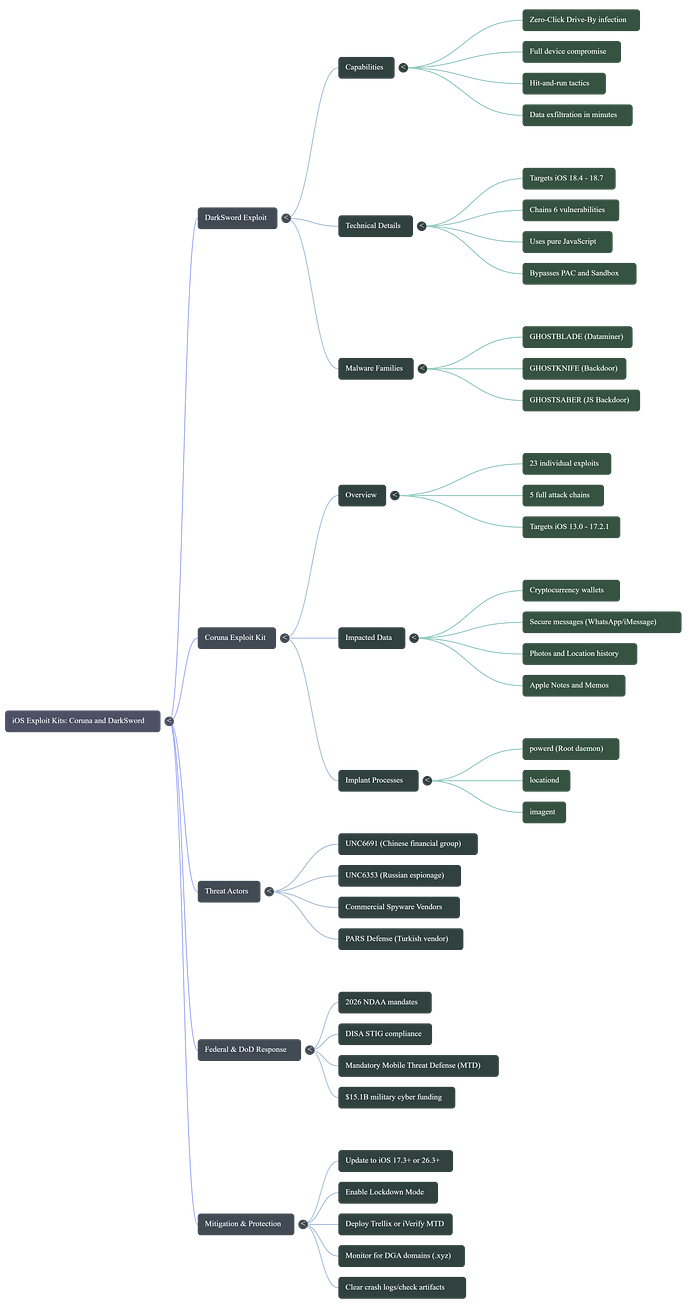
Mindmap
Reference
- https://cloud.google.com/blog/topics/threat-intelligence/darksword-ios-exploit-chain
- https://www.scmp.com/week-asia/lifestyle-culture/article/3347739/iphone-spyware-darksword-hits-malaysia-exposing-spread-sophisticated-hacking-tools
- https://www.malwarebytes.com/blog/mobile/2026/03/a-darksword-hangs-over-unpatched-iphones
- https://thehackernews.com/2026/03/apple-warns-older-iphones-vulnerable-to.html
- https://www.facebook.com/thepatriotsstudio/posts/sistem-keselamatan-apple-akhirnya-dipecah-darksword-mcmc-suruh-update-iosoleh-az/1260239906297558/
