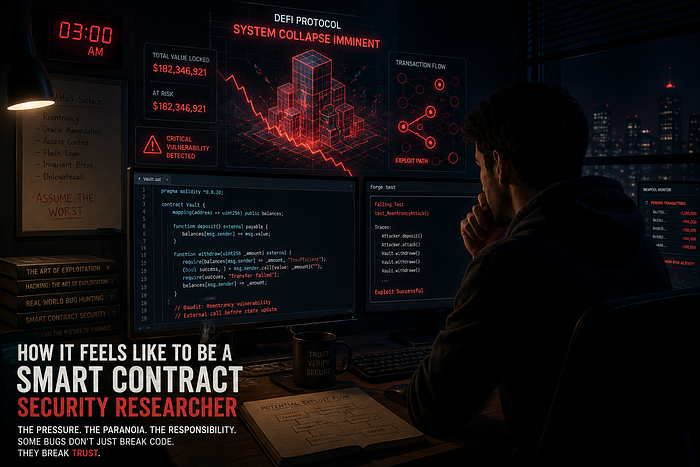
At 3:17 AM, the bug finally revealed itself.
Not loudly. Not dramatically.
Just a tiny inconsistency hidden between two innocent looking lines of Solidity code.
The protocol held over $180 million in user funds. The exploit path took less than six transactions. My heartbeat accelerated as I replayed the attack in my local fork for the fourth time, hoping I was wrong.
I wasn't.
That's the strange thing about being a smart contract security researcher. The biggest moments often happen in complete silence.
No alarms.
No cinematic hacker soundtrack.
Just you, a glowing monitor, cold coffee, and the terrifying realization that a few lines of code could erase years of trust in minutes.
And somewhere out there, someone else might already be looking at the same vulnerability.
What Smart Contract Security Research Really Is
Most people think blockchain security is just "checking code for bugs."
It isn't.
Smart contract security research is psychological warfare against invisible adversaries.
A smart contract security researcher studies decentralized systems the same way a thief studies a bank vault. The job is to think like an attacker before attackers arrive. To identify weaknesses before they become headlines. To understand how complex financial systems break under pressure, manipulation, and human assumptions.
In Web3, code is law.
And unlike traditional software, smart contracts often control real money directly. No customer support. No chargebacks. No emergency rollback button.
One vulnerability can drain millions of dollars in seconds.
That's why smart contract auditing has become one of the most critical disciplines in blockchain cybersecurity.
Every DeFi protocol, governance system, bridge, staking platform, and DAO depends on security researchers seeing what everyone else missed.
Sometimes that means catching catastrophic flaws before launch.
Sometimes it means watching exploits happen in real time and realizing nobody can stop them.
The Psychology of a Blockchain Security Researcher
Being a blockchain security researcher changes how you think.
Permanently.
After enough audits, your brain stops trusting anything.
You stop seeing applications as products and start seeing them as attack surfaces.
Every function becomes suspicious.
Every external call feels dangerous.
Every unchecked assumption sounds like a future postmortem.
You begin mentally simulating chaos everywhere.
- What happens if this oracle fails?
- What if governance gets manipulated?
- What if liquidity disappears during execution?
- What if the attacker flash-loans the entire system?
The paranoia becomes instinct.
And strangely enough, that paranoia is useful.
Because attackers are creative.
They don't care about your roadmap, branding, or investor deck. They care about one thing: finding the single mistake that everyone else ignored.
That pressure follows you constantly.
Even after audits are complete.
Even after reports are submitted.
You still wonder whether you missed something hidden deep inside thousands of lines of Solidity.
The fear never fully disappears.
The Adrenaline Nobody Talks About
There's a unique emotional rush that comes from discovering a critical vulnerability.
It's part excitement.
Part dread.
Part disbelief.
You stare at the screen thinking:
"There's no way this actually works."
Then you test it again.
And again.
And suddenly you realize you've uncovered a reentrancy exploit capable of draining an entire protocol.
Or a governance flaw that allows hostile takeover.
Or a signature replay vulnerability that compromises user funds.
Your body reacts before your mind catches up.
Adrenaline floods in.
Your thoughts sharpen instantly.
Sleep disappears.
Time becomes irrelevant.
For a few intense hours, nothing else in the world exists except the exploit path sitting in front of you.
That emotional high is difficult to explain to people outside cybersecurity.
It feels like solving a puzzle where failure has real-world consequences.
Because it does.
The Daily Life of a Smart Contract Auditor
Most days are less dramatic.
But they are mentally exhausting.
A large portion of smart contract auditing involves reading Solidity code for hours without interruption. You trace execution paths manually, searching for inconsistencies hidden beneath business logic and mathematical assumptions.
The process is methodical.
- You begin with threat modeling.
- How could this protocol fail?
- What assumptions does it rely on?
- What powers do privileged roles possess?
- What happens during extreme market conditions?
Then comes static analysis using tools like Slither, followed by fuzzing frameworks such as Echidna and Foundry.
You write invariant tests.
You simulate malicious interactions.
You attempt to break the protocol repeatedly until either:
- The protocol survives
- or reality starts leaking through the abstraction
Some vulnerabilities are obvious.
Most are not.
The dangerous bugs usually hide behind complexity.
A harmless looking arithmetic operation.
An edge case in governance delegation.
A subtle issue involving token accounting during flash loan execution.
The deeper you go into Web3 security, the more you realize that exploits rarely come from "bad code."
They come from dangerous assumptions.
The Weight of Responsibility
One of the hardest parts of smart contract security research is understanding how much responsibility sits on your shoulders.
People often joke about "finding bugs for money."
But behind every protocol are real people.
- Retail users.
- Developers.
- Communities.
Entire teams whose livelihoods depend on the integrity of the system.
When you audit a protocol managing hundreds of millions in TVL, you feel that pressure constantly.
You know attackers are actively searching for weaknesses too.
The difference is that they only need one successful exploit.
You need to find everything.
That imbalance can become mentally brutal.
Especially during deadline heavy audits where protocols rush deployments while investors demand launch dates.
Security rarely moves as fast as hype.
And in crypto, hype moves dangerously fast.
The Emotional Highs of Web3 Security
Despite the stress, there are moments that make the work deeply rewarding.
Finding a critical vulnerability before launch feels incredible.
Not because of ego.
Because you prevented disaster.
Sometimes a single report saves a protocol from becoming the next exploit headline.
Sometimes your findings protect thousands of users from losing funds.
And occasionally, you receive messages from founders genuinely grateful that their system survived because of your work.
Those moments matter.
Bug bounties can also be life changing.
Some security researchers earn more from identifying vulnerabilities than traditional software engineers earn in years.
But money isn't the only reward.
There's also intellectual satisfaction.
Smart contract security is one of the few fields where curiosity itself becomes a weapon.
You are constantly solving puzzles at the edge of finance, cryptography, distributed systems, and adversarial thinking.
It's exhausting.
But it's never boring.
The Dark Side Nobody Posts About
The internet glamorizes ethical hacking in crypto.
The reality is much heavier.
Burnout is common.
So is impostor syndrome.
No matter how experienced you become, there's always another exploit sophisticated enough to humble you.
Every public hack becomes a learning experience wrapped in anxiety.
You read exploit postmortems obsessively, wondering:
"Would I have caught that?"
Sometimes protocols ignore warnings entirely.
That's one of the most frustrating experiences in blockchain security.
You identify a dangerous vulnerability.
You explain the exploit path clearly.
You recommend mitigation steps.
And the team still ships vulnerable code because deadlines matter more than security.
Then weeks later, the exploit happens publicly.
Watching users lose funds after raising concerns privately is emotionally draining in ways most people never see.
There's also the strange loneliness of the profession.
Most people outside Web3 do not understand what you actually do.
Trying to explain flash loan attacks during casual conversation feels absurd.
So you keep most of the stories to yourself.
The near misses.
The panic.
The nights without sleep.
The moments where billions of dollars rested on whether you understood a protocol correctly.
Lessons Learned From Years in Smart Contract Security
After enough audits, certain truths become impossible to ignore.
Never Trust Assumptions
Attackers thrive on assumptions.
If developers assume a function will "never" be called a certain way, attackers will call it exactly that way.
Every Line of Code Is an Attack Surface
Complex systems create unpredictable interactions.
The vulnerability is often not in the obvious function.
It's in how multiple components interact under abnormal conditions.
Complexity Is the Enemy of Security
The most dangerous protocols are usually the most complicated ones.
More features mean more assumptions.
More assumptions mean more ways to fail.
Attackers Only Need One Mistake
Security researchers operate under asymmetrical pressure.
Defenders must secure everything.
Attackers only need a single overlooked vulnerability.
That reality changes how you think forever.
The Future of Smart Contract Security
The future of smart contract auditing will become increasingly automated.
AI assisted auditing tools are already improving vulnerability detection.
Formal verification is gaining traction.
Autonomous exploit monitoring systems are becoming more advanced.
Static analyzers continue evolving rapidly.
But automation alone will never solve Web3 security.
Because smart contracts are not just technical systems.
They are economic systems.
Human systems.
Behavioral systems.
Attackers exploit psychology as much as code.
And intuition still matters.
Experienced security researchers develop pattern recognition that tools cannot fully replicate.
They notice strange assumptions.
Unusual incentive structures.
Subtle governance risks.
Tiny inconsistencies that feel "off."
That instinct often prevents catastrophic exploits before they happen.
What It Really Feels Like
Being a smart contract security researcher feels like standing between order and chaos with nothing but logic and skepticism.
It feels exciting and exhausting at the same time.
You spend your life studying how systems fail while hoping your own analysis never does.
You learn to think like criminals without becoming one.
You learn that brilliance means nothing without discipline.
And you realize that in Web3, trust is often just mathematics surviving hostile environments.
Most people will never see the vulnerabilities that never became exploits.
They will never know how close certain protocols came to disaster.
And honestly, that's probably a good thing.
Because the best day for a security researcher is often the day nothing happens at all.
The exploit never goes public.
The users never lose funds.
The protocol survives.
And somewhere at 3 AM, another researcher quietly closes their laptop after finding the bug first.
If you enjoyed this deep dive into the life of a smart contract security researcher, follow for more insights on Web3 security, smart contract auditing, blockchain exploits, and the psychology behind securing decentralized systems.
Have you ever explored smart contract security or ethical hacking in crypto? Share your thoughts or experiences in the comments.