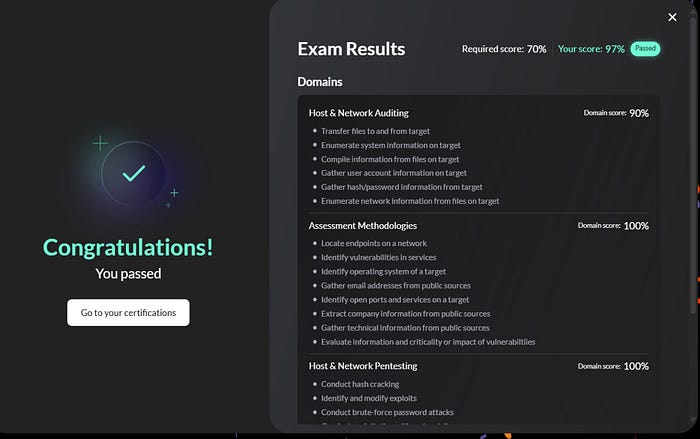
Recently I passed the eLearnSecurity Junior Penetration Tester (eJPT) certification with 97%, and it took me around 10 hours to complete the entire exam. In this article, I want to share the methodology and mindset that helped me succeed, without revealing any exam answers.
If there is one lesson I learned during the exam, it is this:
Enumeration, Enumeration, Enumeration.
Most of the answers in the exam environment reveal themselves through proper enumeration. Many beginners rush into exploitation too quickly, but careful reconnaissance often points directly to the vulnerability.

Enumeration
1. Nmap Scan
The first thing I did was identify the hosts in the DMZ network.
I started with a simple host discovery scan:
nmap -sn <target-ip>/24This command performs a ping scan to identify live machines in the network.
Once I discovered the active hosts, I scanned each machine individually using:
nmap -sC -sV -p- <target-ip>
This scan helps identify:
- Running services
- Service versions
- Potential attack vectors
The -sC option runs default scripts, while -sV performs version detection.
This information is extremely important because it tells you where to focus your efforts.
One important tip during the exam is to save your results in your own note-taking application instead of inside the lab machines.
2. Pay Attention to Web Applications
Several machines in the exam environment expose web services.
Whenever you see ports like: 80, 8080, 443
You should immediately investigate them in the browser.
Things to check include:
- Directory enumeration
- Login panels
- Hidden endpoints
- File upload functionality
Tools that help with this process:
- Gobuster
- Dirsearch
- Burp Suite
Example directory brute force:
gobuster dir -u http://target-ip -w wordlist.txtSometimes vulnerabilities hide in very simple places.
For example, some web servers allow file uploads using WebDAV, which can be accessed using tools like Cadaver. If upload functionality is allowed, you may be able to upload a web shell and gain access to the system.
3. Check for Anonymous FTP Login
Another common service you might encounter is FTP.
Sometimes FTP servers allow anonymous login.
Try logging in using:
AnonymousIf access is granted, check whether file uploads are allowed.
If the FTP server is connected to a web directory, uploading a web shell may allow you to execute commands through the web server.
Sometimes vulnerabilities hide in very simple places.
For example, some web servers allow file uploads using WebDAV, which can be accessed using tools like Cadaver. If upload functionality is allowed, you may be able to upload a web shell and gain access to the system.
4. Use Brute Force When Necessary
If enumeration does not reveal any obvious vulnerabilities, brute force can sometimes be effective.
Common services worth testing include:
- SSH
- FTP
- SMB
- RDP
Tools like Hydra can be used to attempt password attacks if login services are exposed.
However, always ensure proper enumeration is completed before attempting brute force attacks. Brute forcing blindly without understanding the service often wastes time.
Sometimes brute forcing may reveal valid credentials that can be reused on other services.
For example, if you successfully brute force an SSH login, the credentials you obtain might also work for:
- SMB access (file shares)
- Web application login panels
- Databases such as MySQL
- RDP (Remote Desktop Protocol)
- FTP services
Once credentials are discovered, you should immediately test them against other services in the environment.
For example, if SSH credentials are discovered, you could use them to enumerate SMB shares:
smbclient -L //<target-ip> -U <username>If SMB access is available, you may find additional files, credentials, or hints that lead to further exploitation.
In some situations, SMB credentials can also allow remote command execution using tools such as:
- psexec (Metasploit module)
- psexec.py from Impacket
This can provide a remote shell on the target system.
Credential reuse is extremely common in real-world environments, and recognizing this pattern can often help you move laterally between systems during the exam.
SMB servers can often contain valuable information that helps move forward during the assessment.
When accessing SMB shares, you may discover:
- Credentials
- Backup files
- Configuration files
- Notes from administrators
- Sensitive documents
These files can sometimes contain passwords or hints that can be reused to access other services.
5. Never Ignore Credentials
During enumeration you might discover credentials in several places:
- Configuration files
- Exposed directories
- Database dumps
- Web applications
Always try reusing these credentials across multiple services.
For example:
- SSH
- FTP
- SMB
- Databases
Credential reuse is extremely common in real-world environments and also appears frequently in penetration testing labs.
6. Exploitation
Once you complete proper enumeration, the next step is exploitation. At this stage, the goal is to use the information gathered during scanning and service enumeration to gain access to the target system.
One important thing to look for is the service version. Sometimes a specific version of a service may contain known vulnerabilities.
Examples include:
- Web servers (Apache, Nginx)
- CMS platforms (WordPress, Joomla, Drupal)
- Databases
- Network services (FTP, SSH etc…)
If you discover the version of a service or CMS, you should always check whether it has any known vulnerabilities.
A useful tool for this is Searchsploit, which allows you to search the Exploit Database directly from your terminal.
Example:
searchsploit <service> <version>
searchsploit <CMS-name> <version>Sometimes these vulnerabilities may lead to Remote Code Execution (RCE), which allows you to execute commands on the target system.
Many vulnerabilities already have Metasploit modules available that can automate the exploitation process.
A good workflow is to first search for the vulnerability using Searchsploit
When reviewing the results, pay attention to entries that contain .rb files. These usually indicate that a Metasploit module exists for that vulnerability.
Once you identify that a Metasploit module is available, you can go directly into Metasploit and search for the module there.
7. Privilege Escalation
Another important part of the exam is privilege escalation. After gaining access to a machine, your goal is usually to obtain higher privileges on that system.
The most important skill here is local enumeration.
Once you gain access to a target machine, take time to enumerate the system properly before attempting any escalation technique. The PTS course explains several ways to perform local enumeration, and focusing on these techniques is usually enough for the exam.
Things you should check during local enumeration include:
- System information
- Running services
- Installed applications
- Scheduled tasks
- Misconfigured permissions
- Credentials stored in files
The key idea is to carefully inspect the system and look for misconfigurations or vulnerable services that allow privilege escalation.
If you understand the local enumeration techniques taught in the course, you should be able to identify the escalation path.
8. Pivoting
Pivoting is another important concept in penetration testing.
Whenever you gain access to a machine, you should always check whether that system is connected to other internal networks.
The first step is to inspect the network interfaces of the compromised machine.
Linux:
ifconfig
ip a Windows:
ipconfigIf you discover another internal network or subnet, the next step is to perform host discovery within that network to identify other machines.
Once potential hosts are discovered, try to ping them from the compromised machine to confirm that they are reachable. If the host responds, it becomes a pivoting target.
After confirming that the internal host is reachable, you can add a route through the compromised machine using Metasploit:
run autoroute -s <network>/<CIDR>Once the route is added, you can begin scanning the internal network. One way to perform port discovery through the pivot is by using the Metasploit module:
auxiliary/scanner/portscan/tcpAfter identifying open ports on the internal host, you can use port forwarding to access those services from your attacking machine and continue the enumeration and exploitation process.
Pivoting allows you to reach systems that are not directly accessible from your attacker machine, making it an important technique during internal network assessments.
Using SOCKS Proxy for Pivoting
Another powerful pivoting technique is SOCKS proxying, which allows your attacker machine to route traffic through the compromised host and interact with internal systems as if you were inside the network.
After adding the route with autoroute, you can start the SOCKS proxy module in Metasploit.
use auxiliary/server/socks_proxy
show options
set SRVPORT 9050
set VERSION 4a
exploitThis will start a SOCKS proxy server on port 9050.
You can verify that the proxy is running by checking the jobs:
jobsOnce the SOCKS proxy is running, you can configure proxychains on your attacker machine to route traffic through the compromised host.
After configuring proxychains, you can perform scans and interact with internal services such as:
proxychains nmap -sT -sV -p- <internal-ip>This technique is extremely useful when the internal machines are not directly reachable from your attacker machine, but are accessible through the compromised host.
9. Think Like a Pentester, Not a CTF Player
The eJPT exam focuses on realistic penetration testing methodology, not puzzle solving.
Instead of randomly trying exploits, follow a structured approach:
- Information Gathering
- Scanning
- Enumeration
- Exploitation
- Post-Exploitation
If you follow this workflow consistently, the attack path usually becomes clear.
10. Take Notes While You Work
The exam environment contains multiple machines, services, and credentials. Without notes, it becomes very easy to lose track.
I strongly recommend documenting:
- Discovered hosts
- Open ports
- Credentials
- Possible vulnerabilities
Tools that are great for note-taking include:
- CherryTree
- Notion
- Obsidian
Proper documentation makes the exam much easier to manage.
11. Practice Before the Exam
Before attempting the exam, it is extremely helpful to practice on platforms like TryHackMe to strengthen your penetration testing fundamentals.
Some great beginner-friendly rooms include:
That said, it is important to mention that the PTS course material itself, along with the labs and especially the Skill Check exercises, are more than enough preparation for the eJPT exam. If you thoroughly understand the concepts taught in the course and complete the labs carefully, you will already have the necessary knowledge to succeed in the exam.
The TryHackMe rooms are simply an additional way to gain more hands-on practice and become more comfortable with the methodology before starting the exam.
12. Stay Calm During the Exam
The eJPT exam provides plenty of time, so there is no need to rush.
If you get stuck:
- Go back to enumeration
- Revisit previous machines
- Recheck credentials
Often the solution is something simple that was overlooked.
Patience and persistence are key.
13. Recommended Wordlists for Enumeration and Brute Force
For username discovery, you can use the following wordlist from the Metasploit framework:
/usr/share/metasploit-framework/data/wordlists/unix_users.txtFor common password attempts, another useful list is:
/usr/share/metasploit-framework/data/wordlists/unix_passwords.txtThese lists are helpful when performing login attempts against services such as SSH, FTP, or SMB.
For larger password brute force attacks, one of the most popular wordlists is rockyou.txt, which contains millions of real-world passwords.
/usr/share/wordlists/rockyou.txtThis wordlist is commonly used with tools such as Hydra when brute forcing login services.
Example usage:
hydra -L unix_users.txt -P rockyou.txt ssh://<target-ip>Using the right wordlists during enumeration can significantly improve your chances of discovering valid credentials during the exam.
Note :
In some cases during the exam, the username may already be provided in the question itself. This means you do not need to brute force usernames — you only need to brute force the password.
For example, if the question mentions a user named bob, you can directly attempt a password brute force against the service using that username.
Using Hydra, this can be done like this:
hydra -l bob -P /usr/share/wordlists/rockyou.txt ssh://<target-ip>Final thoughts
Passing the eJPT exam was a great learning experience for me. It reinforced the importance of following a structured penetration testing methodology
If there is one piece of advice I would give to anyone preparing for this exam, it is this:
Enumeration, Enumeration, Enumeration.
Most of the vulnerabilities and attack paths become clear once you properly enumerate the network, services, and applications. Many times the answer is already there — you just need to look carefully.
Take your time during the exam, stay organized, and trust the methodology
Best of luck to everyone preparing for the eJPT exam — stay patient, trust the process, and enjoy the learning journey!