Introduction
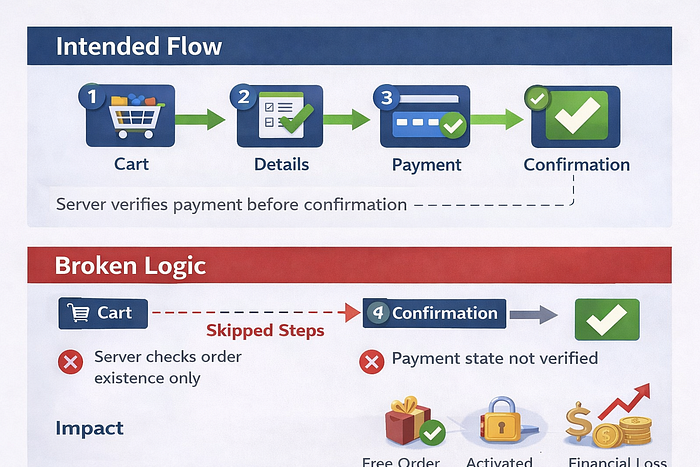
Imagine a customer completing a purchase without paying a dime — all because the system trusted the order of steps rather than verifying them. Modern applications guide users through structured workflows designed to enforce business rules. A typical purchase process follows a predefined order:
cart → user details → payment → confirmation Each step exists for a reason: user identity is verified, pricing is confirmed, and payment is validated before the order is finalized. But what happens when the system assumes users will always follow this order? This article explores how incorrect assumptions about step sequencing can introduce **Business Logic Vulnerabilities** with real-world impact.
The Intended Business Rule
In a secure purchase flow: > An order should only be completed after all required steps are successfully finished. Each step validates a specific condition:
* **Cart step** confirms items and pricing.
* **Details step** validates user information.
* **Payment step** confirms financial transaction.
* **Confirmation step** finalizes the order. The sequence itself acts as a logical control.
The Developer Assumption
Many systems assume: * Users will only navigate using the application interface. * Steps cannot be skipped. * Requests arrive in the intended order. Because of this assumption, backend systems sometimes validate individual actions but fail to validate the overall workflow sequence. Example: the system may accept a final confirmation request without verifying that payment was actually completed in the same session.
The Logic Flaw
If the backend does not enforce step order, an attacker may directly send a request intended for a later stage in the workflow. Example:
POST /confirm-order If the server only checks that an order exists, but not whether payment was completed, the order may be finalized without satisfying previous conditions. The issue is not input manipulation. The issue is that the system trusted workflow order instead of verifying it.
Example Scenario
Step 1: Add items to cart
Step 2: Enter details
Step 3: Payment
Step 4: Confirmation
Consider the following simplified logic: If the application allows direct access to Step 4 without validating Steps 2 and 3: * The order may be marked as completed. * Payment logic is bypassed. * Business rules are skipped entirely. From the system's perspective, the request appears valid because the endpoint exists and accepts requests.
Real-World Impact
When workflow sequencing is not enforced, the consequences can be significant: * Orders may be completed without payment. * Services or digital goods may be activated for free. * Discount or promotion checks may be bypassed. * Inventory may be consumed without valid transactions. At scale, this can lead to: * Financial loss. * Broken transaction records. * Inconsistent order states across systems. * Abuse of promotional or billing logic. Because each individual step appears functional, the vulnerability often remains unnoticed during normal testing.
Why Automated Tools Miss This
Automated scanners typically analyze requests in isolation. Workflow vulnerabilities require understanding: * The intended order of actions. * Dependencies between steps. * Business rules enforced across multiple requests. Detecting this requires reasoning about application behavior rather than scanning for technical signatures.
Secure Design Recommendation
To prevent workflow bypass vulnerabilities: 1. Validate required previous states before allowing progression. 2. Enforce step completion server-side. 3. Reject confirmation requests unless payment status is verified. 4. Treat workflow order as a **security control**, not just a user experience feature. The server must enforce the sequence, even if the interface already guides the user correctly.
Final Thought
Applications rarely fail because a single step is broken. They fail when systems assume users will follow the intended path. **Security improves when workflows are enforced by logic, not by expectation