Information Disclosure is a security vulnerability where a system or application unintentionally exposes sensitive or internal information to users. This means that information is visible that is not intended for normal users to see.
Hey me dear reader…..
This lab from the PortSwigger Web Security Academy demonstrates how information disclosure can lead to an authentication bypass. Applications sometimes reveal sensitive information that attackers can use to gain unauthorized access. Even small leaks — such as hidden parameters or debug information — can expose critical details about how the authentication system works.
This lab shows how exposed information can be used to bypass the login process and access restricted areas of the application.

Authentication bypass occurs when an attacker gains access to a protected area of an application without providing valid credentials. Instead of breaking the password, attackers exploit weaknesses in how authentication is implemented.
Common causes include:
- hidden authentication parameters
- misconfigured access control
- exposed debug information
- predictable tokens
In this lab we can log in to our own account using the following credentials -> wiener:peter
We already know that there is an authentication bypass vulnerability in the administrative interface of this lab, but it is impractical to exploit it without knowledge of a custom HTTP header used by the front-end. Now we need to delete the user Carlos by accessing the admin interface.
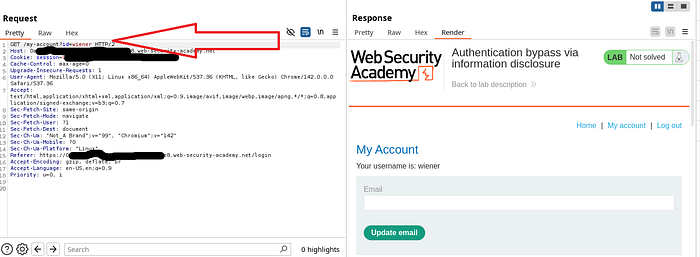
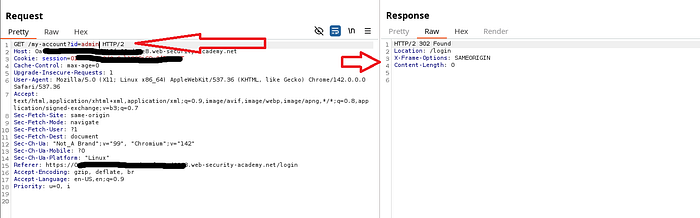
We first login to our account and capture it in burp suite. Now if we change the username wiener to admin and method (GET to TRACE), its status code shows 200. So we can understand that it can be accessed.
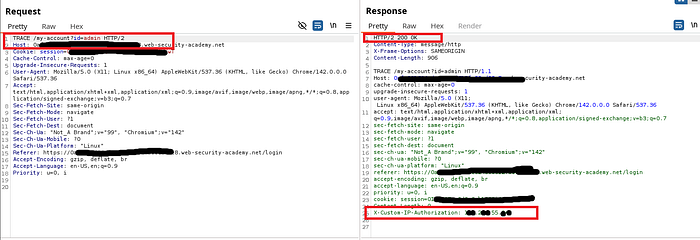
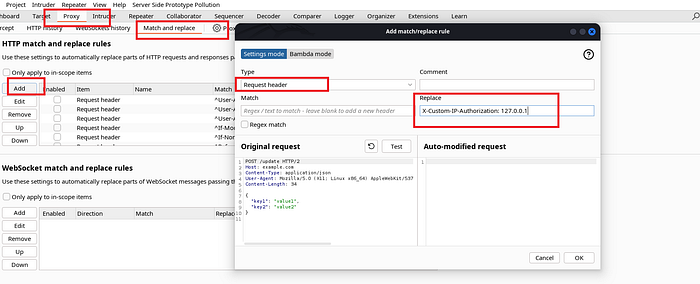
Whenever we replace the authorization in the proxy (local host_127.0.0.1) we easily get admin access.
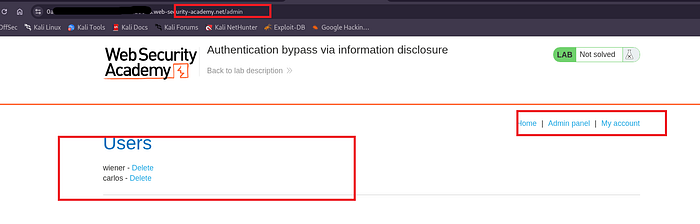
The thing to note here is, Using the disclosed information, it becomes possible to modify the login request in a way that bypasses the normal authentication checks. As a result, the application grants access to the administrator account without requiring valid credentials. This demonstrates how even minor information leaks can lead to serious security vulnerabilities.
This lab demonstrates how information disclosure can directly lead to authentication bypass. Even small leaks can reveal internal system logic, enabling attackers to manipulate authentication mechanisms. Organizations should ensure that sensitive implementation details are never exposed to users and that authentication systems are securely designed.


