Do You Have What It Takes to Be an Extreme Red Teamer?
Hello everyone,
Today I'll be reviewing the Mailservice Lab from Extreme Red Team Laboratories (ERTL) a lab that truly challenges your mindset as an internal Red Teamer.
"Do you have what it takes to be an Extreme Red Teamer?" — Extreme Red Team Laboratories
What is Extreme Red Team Laboratories (ERTL)?
Before diving into the lab, let's talk about ERTL.
Extreme Red Team Laboratories (ERTL) is a specialized training provider focused on advanced Offensive Security labs. Their mission is to deliver highly realistic environments that help cybersecurity professionals sharpen their skills and prepare for real-world threats.
Their labs cover a wide range of domains:
- Linux exploitation
- Windows environments
- Active Directory attack chains
- Cloud attacks (AWS, Azure, GCP)
- Advanced Red Team operations
More information: https://extremeredlab.0x29a.it/#who-we-are
How I Discovered ERTL
Honestly, I didn't know about ERTL at first.
It was introduced to me by Jockky, the 4th Founder of Wowza. He recommended it and that was enough to make me curious.
After browsing their platform, I found two main categories:
Active Directory Chains
Focused on AD-based attack paths (with some additional integrated solutions). https://extremeredlab.0x29a.it/chains

Red Team Labs
Focused on cloud attack scenarios (AWS, Azure, GCP). https://extremeredlab.0x29a.it/redteamlabs
You already know which one I chose.
Active Directory, of course.
Choosing the Mailservice Lab
Inside the Active Directory Chains category, there are multiple labs available, each with its own description.
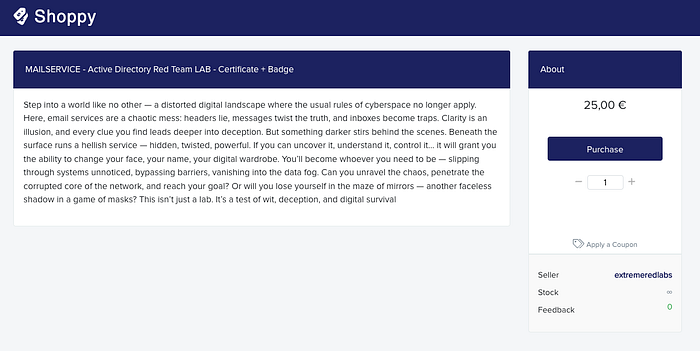
One of them is Mailservice, and its description feels almost like a cyberpunk story.
It talks about a distorted digital world where:
- Email headers lie
- Messages manipulate the truth
- Inboxes become traps
And behind the scenes, there is a hidden service capable of manipulating identities — allowing someone to change their name, appearance, and digital identity to move through systems unnoticed.
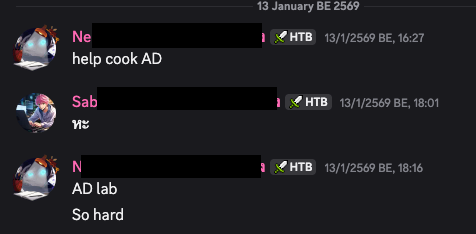
At the time, Jockky was already cooking hard in this lab, so I decided to jump in and join him.
How to Access the Lab
The onboarding process is straightforward:
- Go to the Lab Access page.
- Choose your desired lab.
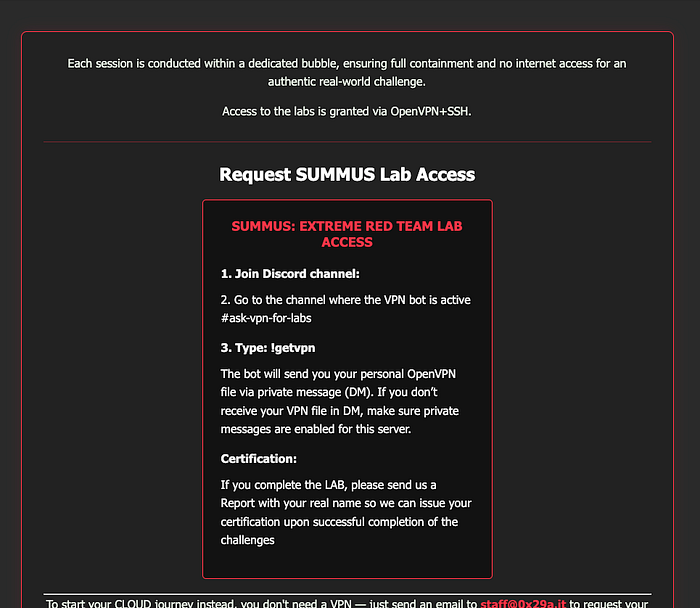
- Join the official Discord server (link at the bottom of the website).
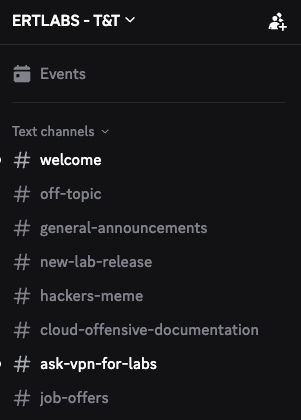
- Navigate to the specific lab channel (e.g.,
mailservice-lab-instructions).
- Follow the connection instructions.

- Request VPN access via the
ask-vpn-for-labschannel using the command:
!getvpn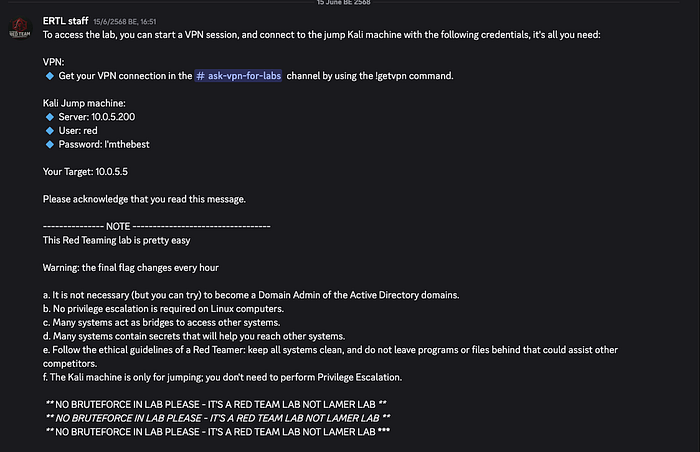
- You will receive an
.ovpnfile (OpenVPN configuration). - Connect and begin.

Important rule stated clearly:
NO BRUTEFORCE IN LAB PLEASE — IT'S A RED TEAM LAB NOT LAMER LAB
That line alone tells you what kind of mindset this lab demands.
Scope & Starting Point
After connecting via VPN, you receive a jump machine and target information.
In my case, the primary target domain was:
10.0.5.5Attack Overview
Since the lab owners do not allow public write-ups, I will only describe the high-level overview.
The environment includes both Linux and Windows systems.
The provided Jump Machine is a Linux host, which plays a critical role in the attack process. It is mainly used for:
- Uploading or transferring files into the environment
- Staging tools inside the internal network
- Pivoting to other machines within the network
The attack chain usually begins from an external perspective, then gradually expands through lateral movement across multiple machines.
Normally, in an Active Directory attack scenario, the primary objective is to compromise the Domain Controller, since it represents the central authority of the domain.
However, this lab takes a slightly different approach.
Although the domain environment is still important, the real objective is not simply gaining domain dominance.
You don't necessarily need to become the "king of the domain."
Instead, the real goal is to extract sensitive information from the environment (the flag).
This design makes the lab feel closer to real-world red team operations, where the mission is not always to own the entire domain, but to achieve the mission objective.
And that mission is simple:
Exfiltrate critical data from the target network.

Knowledge Required
CVE Exploitation
You should be able to identify vulnerable versions of services and search for available exploits using sources such as:
- Exploit-DB GitHub and Metasploit modules

Linux Knowledge
Basic to intermediate Linux knowledge is required.
You should be comfortable using commands and navigating the system.
For example:
rm -rf *(You can try practicing that command… it's a very "powerful" one 😄)
Active Directory Knowledge
You should understand tools such as BloodHound, which helps reveal hidden and often unintended relationships within Active Directory.

It helps identify possible attack paths and determine where to move next.
Pivoting
Since the lab involves multiple network segments, pivoting is required.
Recommended tools include:
It has evolved significantly and now includes a GUI version:
ligolo-mpIf you prefer something classic, Chisel is also a good option.
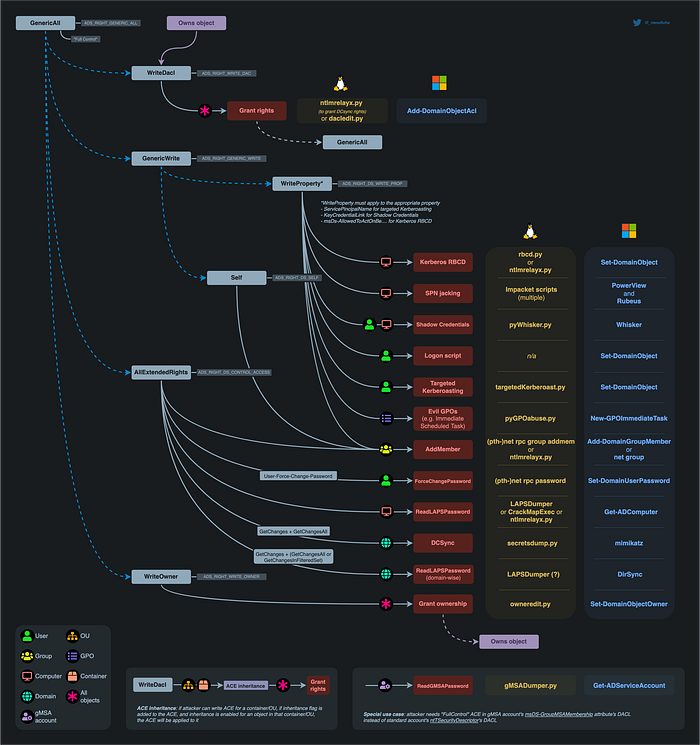
DACL Abuse
Understanding DACL permissions is important for controlling access rights.
Examples include:
- AddMember
- ForceChangePassword
- Targeted Kerberoasting
NetExec
One of the most powerful tools available.
You will see it mentioned in many blogs because it can perform many tasks, such as:
- Host discovery
- User enumeration
- Share enumeration
- LSA dumps
- SAM extraction
- Secrets dumping
- And more
Getting the Certificate
After successfully retrieving the flag, you can contact the ERTL staff via Discord and provide the flag.
They will ask you to:
- Submit your report
- Pay the certification fee (if you want the certificate)
The certificate costs 25 €. Which is roughly 960 THB.
You can purchase from staff (staff sent link to you )
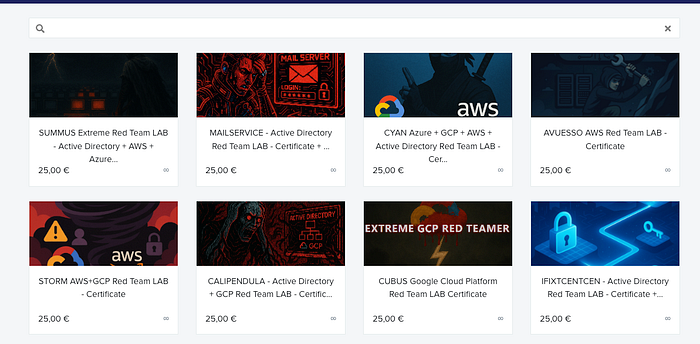
After payment, you will receive the certificate via email.
Of course, purchasing the certificate is optional — but if you want something cool to flex, it's worth it.
(And apparently I might be the first person in Thailand to complete it… since I seem to be the only one playing it.)

Final Thoughts
Mailservice is fun but expect rabbit holes.
It will test:
- Your discipline
- Your pivoting ability
- Your AD knowledge
- Your operational patience
If you are serious about improving as an internal Red Teamer especially in Active Directory environments this lab is worth your time.
So the real question remains:
Do you have what it takes to be an Extreme Red Teamer?
Profile : Sabastiaz
Facebook: https://www.facebook.com/sabastian.fhantomhive Medium : https://medium.com/@sabastiaz Linkedin: https://www.linkedin.com/in/ratthapong-sommanus-465b661b2/

