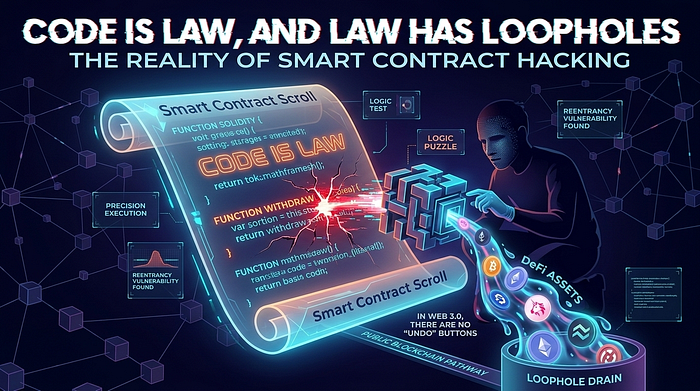
Code is Law, and Law has Loopholes: The Reality of Smart Contract Hacking. In Web 3.0, there are no "Undo" buttons. Here is why hacking decentralized finance is the ultimate test of logic and precision.
The dream of Web 3.0 was decentralization: a world where we don't need banks or middlemen because we have the Blockchain. But as any security researcher will tell you, removing the middleman also removes the safety net.
In traditional finance, if a hacker steals your credit card, you call the bank and they reverse the transaction. In the world of Smart Contracts, if a hacker finds a bug in your code, they drain the vault, and the money is gone forever. There is no customer support for a malicious transaction on the Ethereum mainnet.
Here is why Web 3.0 hacking is the most unforgiving — and potentially lucrative — field in cybersecurity today.
1. The Reentrancy Attack: The Classic "Double-Dip"
The most famous vulnerability in smart contract history (the one that led to the original DAO hack) is the Reentrancy attack.
Imagine a vending machine that gives you your snack before it subtracts the money from your balance. A Reentrancy attack is like reaching into the machine, grabbing the snack, and then quickly triggering the "give me my snack" function again before the machine realizes you've already taken one.
In code, this happens when a contract sends funds to an external address before updating its own internal state. If that external address is a malicious contract, it can call the "withdraw" function recursively until the vault is empty.
2. Logic Errors: The "Math" Hack
Most Web 3.0 hacks in 2026 aren't about complex exploits; they are about simple math errors.
- Integer Overflows/Underflows: Although modern versions of Solidity (the primary language for smart contracts) have built-in protections, legacy code and custom math libraries often fail to handle numbers that get too big or too small.
- Access Control: Forgetting to add the
onlyOwnermodifier to a sensitive function is the blockchain equivalent of leaving your front door wide open. If a function can "self-destruct" the contract or change the "Admin" address, someone will find it.
3. Oracle Manipulation: The Price of Trust
Smart contracts often need to know the price of an asset (like ETH or BTC) to function. Since they can't "Google it," they rely on Oracles.
An attacker with a massive amount of capital (often through a "Flash Loan") can temporarily pump or dump the price of a token on a decentralized exchange. If the smart contract trusts that specific exchange as its only price source, the attacker can force the contract to execute a trade or a liquidation at an absurdly unfair price.
4. Your Web 3.0 Toolkit
If you want to start auditing smart contracts, you need to move beyond the Linux terminal and into the world of EVM (Ethereum Virtual Machine):
- Remix IDE: The best web-based environment to write and test Solidity code instantly.
- Slither: A static analysis framework that automatically detects common vulnerabilities in your code.
- Foundry / Hardhat: These are the professional development frameworks. If you aren't writing unit tests for every possible edge case in Foundry, you aren't ready for production.
- Etherscan: Your "window" into the blockchain. Mastering how to read verified source code and track transactions on Etherscan is essential.
The "Code is Law" Philosophy
In Web 3.0, the hacker is the ultimate auditor. Because the code is public and immutable, every contract is a "Bounty" by default.
Securing decentralized systems requires a shift in mindset. You are no longer defending a server; you are defending a set of mathematical rules. If those rules are flawed, the system is broken. In 2026, as we move more of our global economy onto the chain, the difference between a thriving ecosystem and a multimillion-dollar headline is a single line of Solidity.
Disclaimer: I am an independent security practitioner. This article is for educational purposes only. Interacting with live smart contracts or attempting to exploit vulnerabilities on a public blockchain without authorization is illegal and can have severe legal and financial consequences. Always test on a Local Testnet.
⛓️ Is "Decentralized" always "Safer"?
Do you think the "Code is Law" approach is the future, or do we need better "emergency brakes" in DeFi? Have you ever looked at a smart contract and spotted a bug? Let's talk about the risks and rewards of Web 3.0 in the comments!
If you're ready to dive into the world of Solidity and blockchain auditing, give this article 50 claps and follow for more technical deep dives.