Bypassing Apple's Validation to Clone Any Podcast
When hunting on Apple Podcasts Connect, I found a simple logic flaw that allowed anyone to bypass duplicate feed protections and clone existing podcasts. Here is how I did it, which led to an Apple Hall of Fame acknowledgment in February 2026.
The Flaw
To prevent spam, Apple rejects duplicate RSS feed URLs with a 403 Access Denied error. However, the system only validated the URL string, completely ignoring the actual XML content inside the feed.
Steps to Reproduce
- Find a target podcast already published on Apple Podcasts and download its
.rssfile. - Upload that exact, unmodified file to your own cloud storage (like Google Cloud Storage or AWS S3).
- Log into Apple Podcasts Connect and submit your new Cloud Storage URL.
- Bypass successful: The system accepts the new URL and creates a cloned version of the show.
Impact
This flaw allowed malicious actors to hijack show identities, clone premium content, confuse listeners, and spam the platform with duplicate feeds.
The Outcome
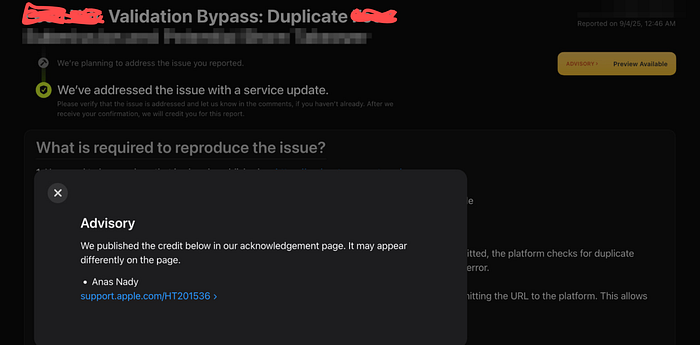
I reported this to Apple Product Security. They recognized the logic flaw and deployed a patch to validate content properly.
While the report didn't qualify for a cash bounty (Apple categorized it as platform abuse rather than a direct data breach), they resolved the issue and officially credited me in their Security Acknowledgements (Hall of Fame) in February 2026.
Timeline
- September 4, 2025: Vulnerability discovered and reported to Apple Product Security.
- September 8, 2025: Additional context and notes provided to the team.
- February 4, 2026: Apple confirms a system change was deployed and requests my validation.
- February 16, 2026: I confirmed the fix was successful.
- February 16, 2026: Apple credited me on their official Security Acknowledgements page.