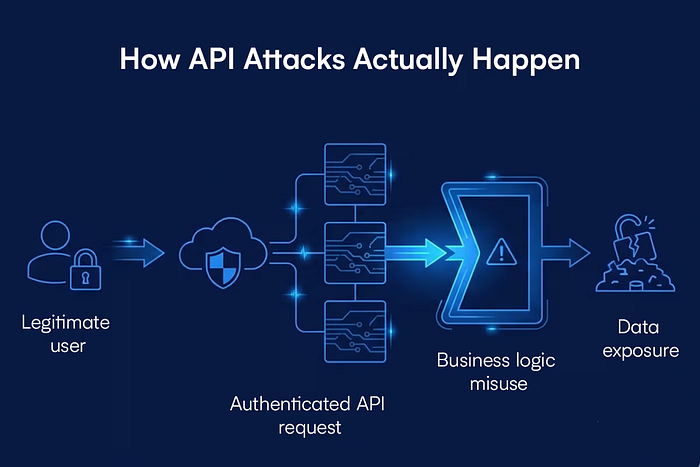
It's about noticing the window slightly open. It's about realizing the window leads to the hallway. And the hallway leads to the room no one thought you could reach.
That's how real attacks unfold.
In API security, we often get distracted by CVEs, those big, dramatic vulnerabilities with scary scores attached to them. We go hunting for the one "Godzilla" bug that will bring everything down in one move.
But here's the truth: most real-world breaches don't happen because of one flaw. They happen because of connections.
Let's make it practical.
If someone wants to take over an account by brute-forcing a login endpoint, they usually don't start with the login itself. They first need valid usernames or emails. That might come from a data exposure flaw inside the same application. Or from information leaked somewhere else. Or from an entirely different breach where users reused passwords.
One weakness opens the door for the next. And like that… the chain continues.
That's the part many teams underestimate.
In this article, I'll walk you through a lab scenario using crAPI, a deliberately vulnerable API environment designed for learning. It simulates a microservice-based web application for vehicle owners. You can order spare parts, return purchases, book mechanics, and download mechanic reports. Just the everyday functionality.
But beneath those normal features, small weaknesses can connect in surprising ways. And when they do, the impact becomes far bigger than any single bug on its own.
Lab-Based Scenario of a Chain Attack
Step 1: Observing the Application
I started as a regular user of crAPI, browsing the application while capturing traffic using Burp Suite.
While navigating through the app, I noticed two endpoints on the frontend:
get past order detailsget mechanic report
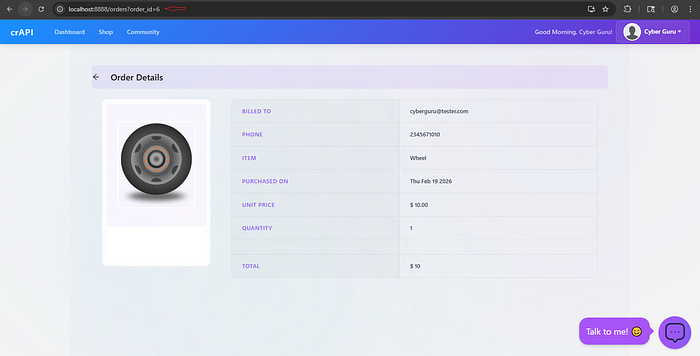
Both had something interesting:
?id={number}That immediately raised a question:
Is that ID validated on the backend, or is it just assumed to belong to the logged-in user?
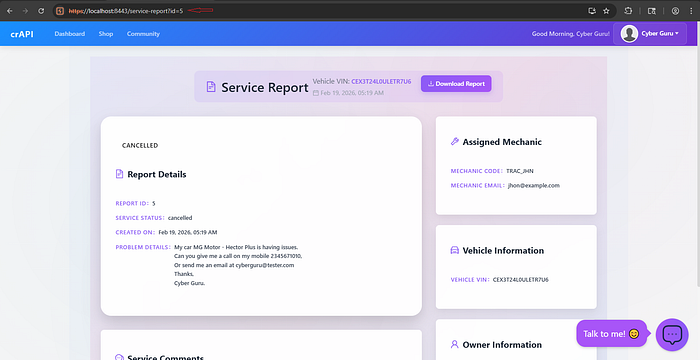
Step 2: ID-Based Access Without Proper Authorization (The Initial Weakness)
On Burp Suite, I sent the get mechanic report request to Repeater and changed:
id=5 to id=1And just like that, I could see another user's report.
The response included:
- Email address
- Phone number
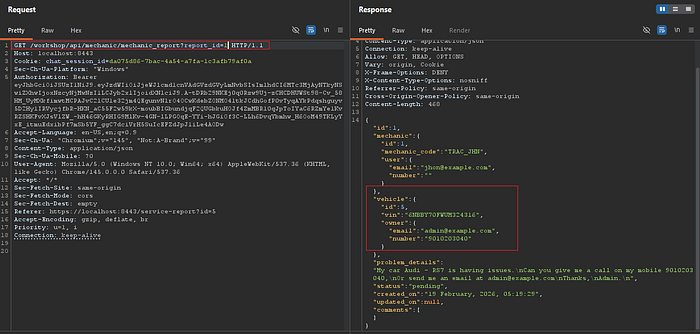
That was the first red flag.
The API wasn't checking who actually owned the data. It just looked at the ID in the request, found a matching record, and sent it back.
This is a classic Broken Object Level Authorization (BOLA) vulnerability. BOLA is typically rated anywhere from High to Critical, depending on what kind of data is exposed or what actions become possible. Some teams might look at it and say, "It's just contact information. That's high severity at most." But that thinking misses the bigger picture. What looks small on its own can become the first step in something much larger. BOLA isn't dangerous only because of the data it reveals. It's dangerous because of what that data can lead to.
Step 3: Enumeration with Intruder (Expanding The Initial Weakness)
Next, I sent the request to Intruder and performed a simple Sniper attack.
I tested IDs from:
1 to 20
The result?
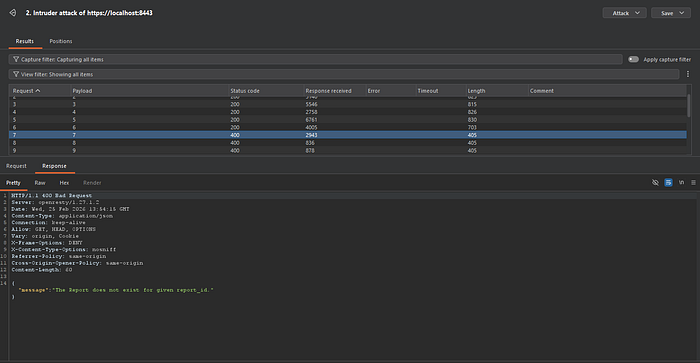
- Valid responses until ID 6
- After that: "Report does not exist"
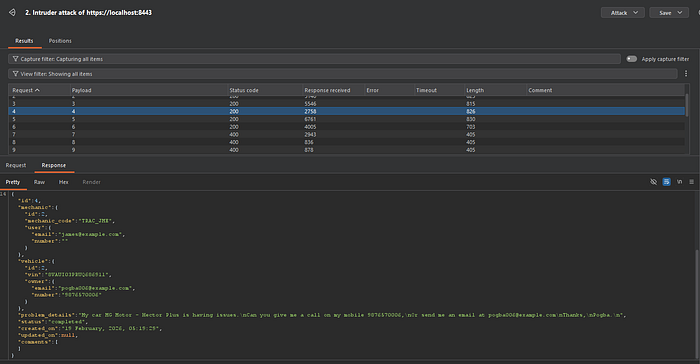
From this, I gathered multiple valid user records
Then I repeated the same process on the past order details endpoint.
This time, I got more email addresses before I hit the does not exist response.
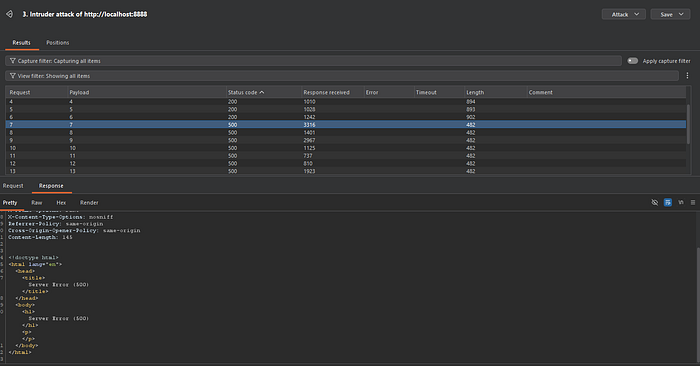
At this point, I had:
✔ Valid user emails ✔ Confirmation that IDs were predictable ✔ No ownership validation
See How a Second Vulnerability Amplifies Impact
Step 4: No Rate Limiting on Login and Weak Password Policy
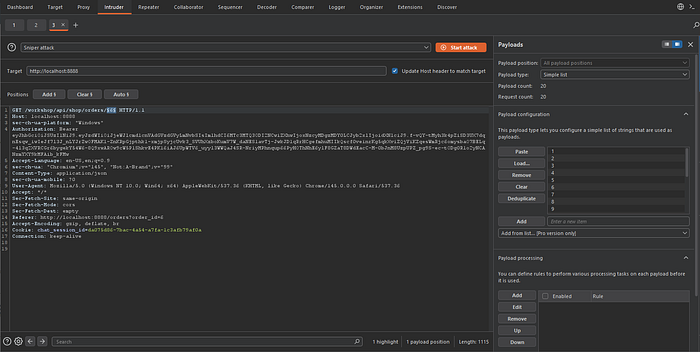
I captured the login request on Burp Suite and sent it to Intruder:
POST /identity/api/auth/loginUsing Intruder's Cluster Bomb attack, which generates all possible combinations of the lists. I:
- Added a list of collected emails
- Added a list of common passwords
- Then, launched the attack

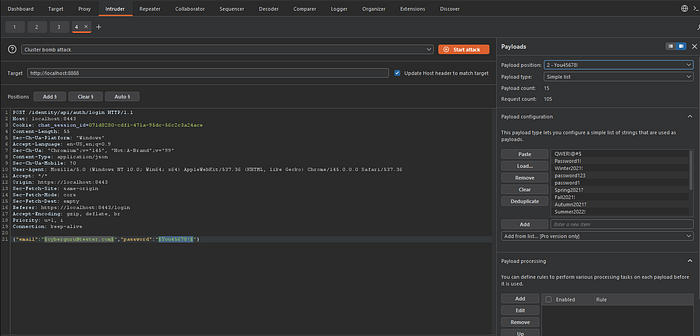
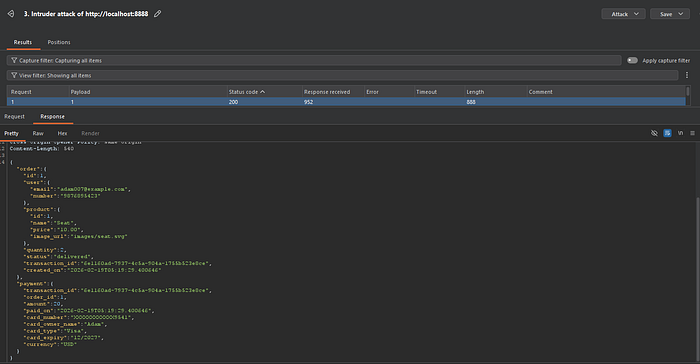
Out of 105 combinations, two login attempts were successful.

There was:
❌ No rate limiting ❌ No account lockout ❌ No CAPTCHA ❌ No brute-force protection
With those credentials, I successfully logged in as two different users.
Again, on its own, lack of rate limiting may be dismissed as "medium priority." But connected to the first weakness? It becomes dangerous.
How the Chain Forms
Let's break the chain down:
First, a BOLA issue allowed me to access records that didn't belong to me. By simply changing IDs, I was able to harvest real user email addresses.
Next, the login endpoint had no rate limiting. That meant I could take those harvested emails and run them through a brute-force attack without being slowed down or blocked.
Finally, weak password choices made the attack successful. And just like that, I had valid logins.
Step by step. Small gap after small gap.
This is the part many people miss: Real API breaches is rarely caused by one single catastrophic flaw. It's usually the result of multiple small failures lining up perfectly.
Individually, each issue might seem minor. Together, they open the door.
How Attackers Connect Weaknesses
Attackers look for:
- Data harvesting opportunities
- Authentication weaknesses
- Authorization gaps
- Input predictability
- Lack of monitoring or rate limits
They don't stop after finding one bug.
They ask:
"What does this unlock?"
In our scenario:
- BOLA unlocked valid emails.
- Emails unlocked brute-force attempts.
- Brute-force unlocked accounts.
- Accounts unlocked full user access.
Each step feeds the next. That's an attack path.
The Final Business Impact
Now zoom out from the technical side.
What does this mean for the business?
- Customer trust is broken.
- Private reports and order history are exposed.
- Accounts are taken over.
- Potential regulatory consequences (especially if personal data is involved).
- Reputational damage that lasts longer than the vulnerability itself.
Notice something important:
None of this required a "critical CVE." No zero-day. No advanced exploit.
Just high to moderate weaknesses connected together. Impact is what matters.
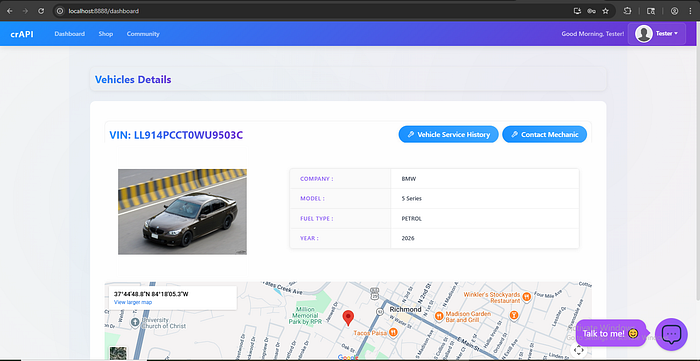
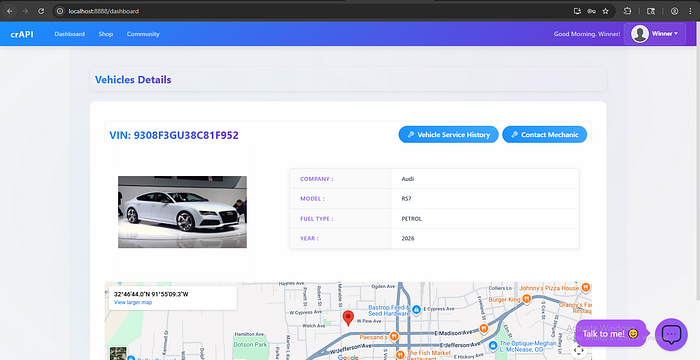
So What Does the Final User Impact Actually Look Like?
This is where it stops being "just a vulnerability" and starts becoming someone's real problem.
Once I gained access in the lab scenario, I realized I could go further. I could change the user's password and completely lock them out of their own account. Imagine waking up and not being able to log in, not because you forgot your password, but because someone else changed it.
It doesn't stop there.
If a credit card was already linked to the account, I could make purchases, a new car booking, spare parts, services, and the actual owner wouldn't even be able to remove the card from their side anymore. Their only option would be to call customer support and start explaining that their account had been taken over.
And by the time that process begins? The damage could already be done. That's just in a vehicle service application.
Now pause and think about something more sensitive, a financial platform or a health application. Access to transaction histories. Medical records. Personal identifiers. The consequences wouldn't just be frustrating; they could be devastating.
That's why chaining vulnerabilities matters so much. Because what starts as "just exposed emails" or "just no rate limiting" can quickly turn into account takeover, financial loss, reputational damage, and a very real loss of trust.
Why Impact Matters More Than CVEs
Security teams sometimes focus too heavily on CVSS scores and CVEs.
But attackers don't think in CVEs.
They think in:
- "What can I access?"
- "What can I reuse?"
- "What can I combine?"
A medium vulnerability plus another medium vulnerability can equal a critical breach.
A system with ten "low-risk" issues may be far more dangerous than one system with a single "high" issue, if those ten issues connect.
How Defenders Should Think in Terms of Attack Paths
If you're responsible for defending APIs, there's a small but powerful mindset shift that makes a huge difference.
Instead of asking:
"How severe is this bug?"
Start asking:
"What could this bug turn into?"
Because attackers don't see isolated findings. They see stepping stones.
Here's how I've learned to think about it.
1. Exposure Chains If some data leaks here, emails, user IDs, internal references, where else could that data be useful? Could it support enumeration? Password attacks? Social engineering? Small leaks rarely stay small.
2. Privilege Escalation Paths If a user can access Object A, what's stopping them from pivoting to Object B? Is there a hidden assumption in the authorization logic? Is trust being placed where it shouldn't be?
3. Authentication Abuse If login protections are weak, what other exposed data makes that worse? Valid usernames + no rate limiting + weak password policies, that combination is far more dangerous than any one issue alone.
4. System Relationships How do your endpoints relate to each other? What does one API response enable in another workflow?
Conclusion
APIs are interconnected by design. That's their strength. But it's also why attack paths exist.
If you're building or securing APIs, train yourself to see connections. Map attack paths. Think like someone trying to combine weaknesses, not just find them.
Because in API security, the real risk isn't the single bug. It's what happens when someone connects the dots.
So don't just fix the bugs, but break the chain before someone else connects it.
If you found this helpful, feel free to clap, like, or share it. And follow me for more hands-on insights into cloud security and API security, focused on real behavior.