Many people imagine penetration testing as a series of dramatic exploits against vulnerable systems. In reality, experienced penetration testers spend most of their time doing something far less visible: studying their targets.
Before a single exploit is launched, testers map infrastructure, discover hidden assets, and gather intelligence about the environment. This process known as reconnaissance often determines whether a penetration test succeeds or fails.
Penetration Testing Methodology
The Penetration Testing Execution Standard (PTES) provides a structured methodology for conducting penetration tests.
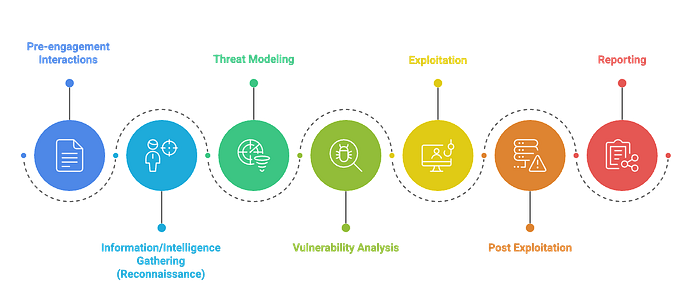
1. Pre-engagement Interactions Define scope, objectives, authorization, communication channels, and rules of engagement between testers and the organization.
2. Information/Intelligence Gathering (Reconnaissance) Collect technical and organizational information about the target using passive and active reconnaissance techniques.
3. Threat Modeling Identify potential attackers, valuable assets, trust boundaries, and likely attack paths within the target environment.
4. Vulnerability Analysis Analyze discovered systems, services, and configurations to identify exploitable security weaknesses.
5. Exploitation Attempt controlled exploitation of confirmed vulnerabilities to obtain access or demonstrate security impact.
6. Post-Exploitation Evaluate the impact of compromise through privilege escalation, lateral movement, persistence, and sensitive data access.
7. Reporting Document testing methodology, findings, evidence, risk severity, and remediation recommendations for stakeholders.
Information/ Intelligence Gathering (Reconnaissance)
Most people perceive penetration testing as a sequence of exploits against vulnerable systems. In practice, experienced testers rarely begin there.
Before any scanning, exploitation, or privilege escalation takes place, penetration testers invest time in studying their target environment. They map infrastructure, identify technologies, and collect information of the target. This process is known as reconnaissance.
The effectiveness of a penetration test often depends less on advanced exploitation techniques and more on how thoroughly the reconnaissance stage is performed.
Key observation from real security assessments The most valuable vulnerabilities are rarely discovered through blind scanning. They emerge from patterns uncovered during reconnaissance.
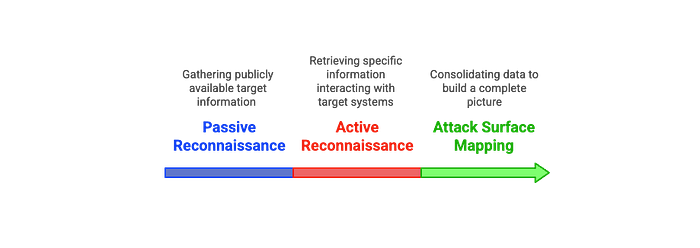
Passive Reconnaissance
Passive reconnaissance focuses on open-source intelligence (OSINT) sources. These methods help testers understand the organization's digital footprint while remaining undetected.
Common Passive Recon Techniques
- Domain and subdomain discovery
- Email and employee enumeration
- Technology stack identification
- Public document metadata analysis
- Infrastructure discovery through search engines
Common Passive Recon Tools
- theHarvester: Collect emails, domains, and hostnames from public sources
- Amass: Subdomain discovery using multiple OSINT sources
- Maltego: Visual relationship mapping between people, domains, and infrastructure
- Shodan: Identify exposed devices and services on the internet
Active Reconnaissance
Active reconnaissance involves direct interaction with the target infrastructure to obtain detailed technical information. These actions may generate logs or alerts in monitoring systems.
Common Active Recon Techniques
- Host discovery
- Port scanning
- Service enumeration
- Operating system fingerprinting
- Web application directory discovery
Common Active Recon Tools
- Nmap: Network discovery, port scanning, and service detection
- Masscan: High-speed scanning of large network ranges
- Nikto: Identify web server misconfigurations and vulnerabilities
- Dirsearch: Discover hidden directories and files on web server
- Netcat: Manual interaction with network services and banner grabbing
Real-World Case: WannaCry Ransomware & National Security Agency (NSA) Exploit Tools
The 2017 Equifax Data Breach exposed sensitive data of approximately 147 million people. While the technical root cause was a vulnerability in Apache Struts, the attackers first had to identify a reachable system running the vulnerable software.
Target Discovery & Reconnaissance
The WannaCry outbreak in 2017 leveraged the EternalBlue exploit, which was an NSA-developed tool later leaked by the Shadow Brokers.
Before deploying ransomware, attackers conducted extensive network reconnaissance: scanning for unpatched Windows machines exposing SMBv1 (port 445) externally or internally.
Techniques used included:
- Mass IP scanning to identify vulnerable subnets and ranges.
- Banner grabbing to detect Windows versions and service packs.
- Using leaked exploit signatures to verify targets without triggering full exploitation yet.
Information Correlation
Recon data wasn't just a list of IPs, it included patch status, system architecture, and even regional targeting patterns.
This step was crucial. EternalBlue only worked on unpatched Windows 7 and Server 2008 machines, so mapping OS versions at scale was a reconnaissance problem.
Pivoting and Lateral Movement Preparation
Once initial vulnerable hosts were identified, the attackers used reconnaissance results to plan propagation paths.
Lateral movement leveraged internal recon: SMB shares enumeration, weak credentials, and machine trust relationships.
By knowing the network layout, attackers optimized the ransomware spread for maximum impact.
Operational Success
- Recon enabled the malware to jump across corporate networks almost instantly.
- Security teams were caught off guard because the attack vector was not generic phishing but highly precise targeting based on OS and network topology data.
- Had reconnaissance been incomplete, many of the infection attempts would have failed, limiting the attack's reach.
This incident demonstrates key takeaways:
Real-world attacks rely on detailed asset profiling before any exploitation.
Recon isn't just passive anymore. It blends passive intelligence gathering (shodan, DNS, WHOIS) with active fingerprinting (ports, services, OS detection).
Understanding patch levels, service configurations, and trust relationships can determine the success or failure of an entire offensive operation.
References
http://www.pentest-standard.org/index.php/PTES_Technical_Guidelines
https://www.kaspersky.com/resource-center/threats/ransomware-wannacry
https://unit42.paloaltonetworks.com/unit42-threat-brief-wanacrypt0r-know/
