This writeup documents a user enumeration vulnerability identified during a security assessment of OWASP Juice Shop. The finding was identified through manual black-box testing using Burp Suite and browser DevTools.
Severity: High CVSS: 7.5 (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N) Endpoint: POST /rest/user/security-question
Description: The endpoint reveals account existence through inconsistent server responses.
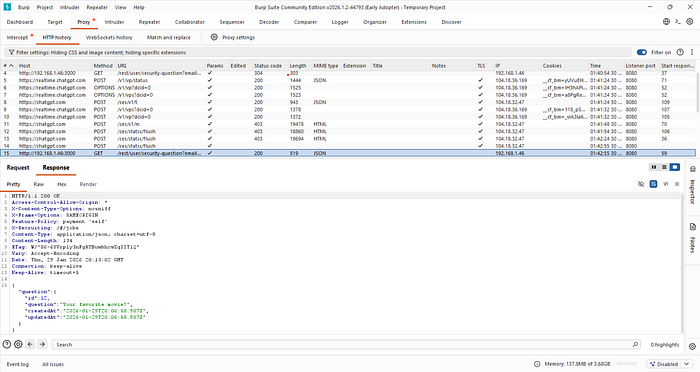
Steps to Reproduce:

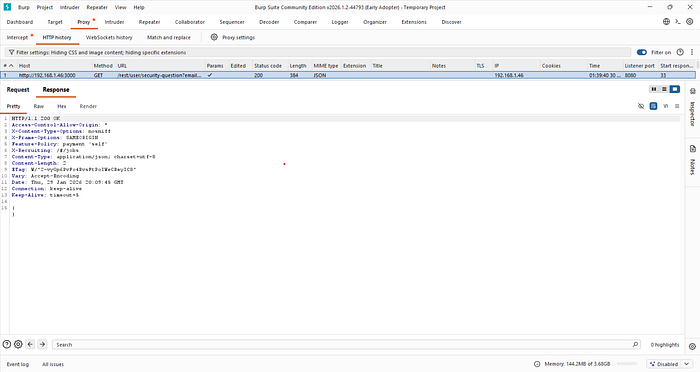
- Submit non-existent email
- Observe 304 response
- Submit valid email
- Observe 200 response with JSON Proof of Concept
POST /rest/user/security-question
{ "email": "demo@demo.com" }
→ 200 OK
Business Impact: Enables mass account discovery, phishing, and targeted attacks.

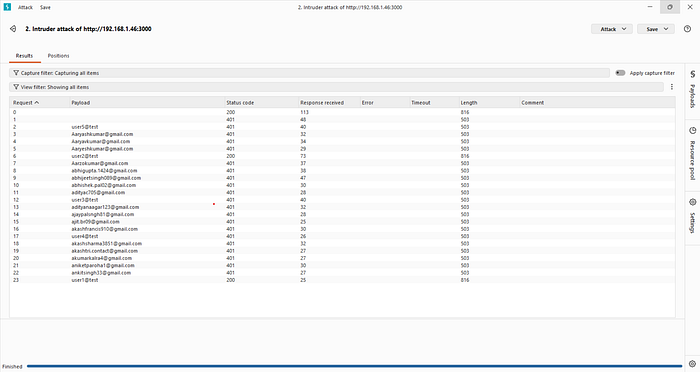
Remediation: Return uniform responses and implement rate limiting.
This vulnerability demonstrates how inconsistent server responses can leak sensitive information about registered users, enabling targeted attacks. Uniform response handling is critical to preventing account enumeration.